ChatGPT Won't Let You Type Until Cloudflare Reads React S...
Ever noticed a frustrating delay before you can type in ChatGPT? The culprit is Cloudflare's security system reading your browser's React state before granting access.
The Windows 11 25H2 update has left countless producers staring at deactivated DAWs and plugins. Here's what happened and your path forward as a music creator.

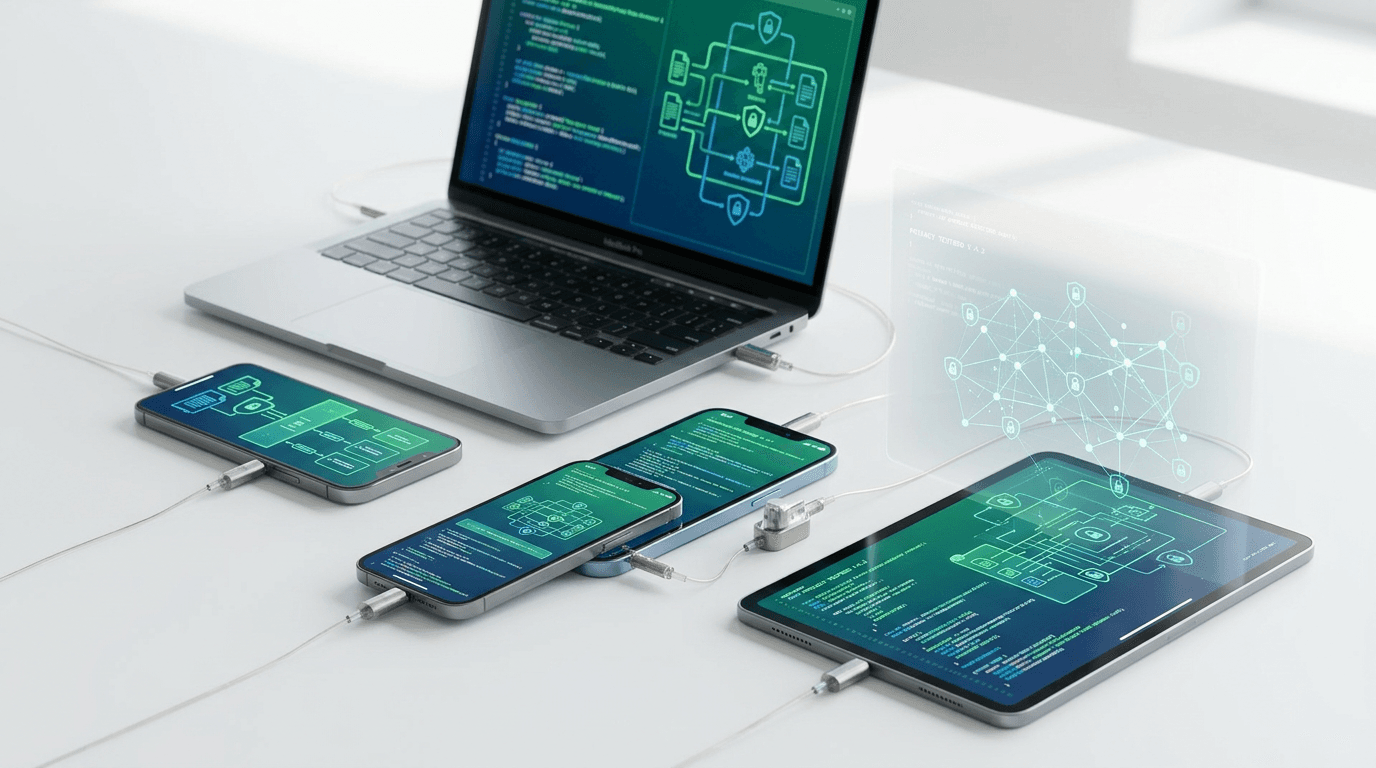
A deep dive into the White House's official mobile application reveals fascinating technical choices, security implementations, and design decisions that reflect modern government tech.
Apple quietly tests revolutionary privacy capabilities that go beyond current protections. These enhancements could set new industry standards for user data security and control.

Discover legitimate methods to intentionally degrade macOS performance for testing, development, and educational purposes. Learn how systems fail to build better applications.

Gulf states issued a joint statement condemning Iran's attacks and declaring readiness for self defense. This shift carries major implications for businesses, energy markets, and global trade.

GitHub now uses Copilot Free, Pro, and Pro+ interaction data for AI training starting April 24. Discover what changed, how it affects your code, and steps to opt out.
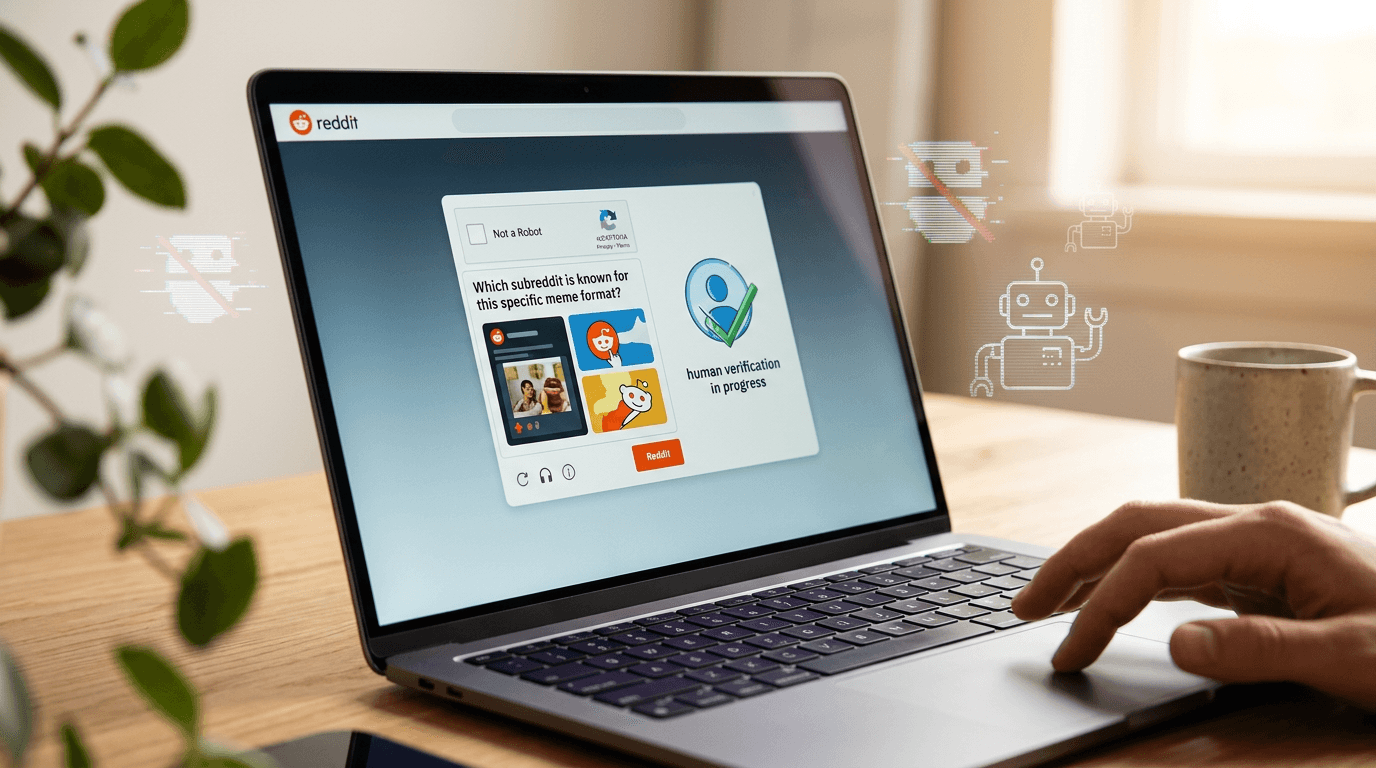
Reddit now requires accounts with suspicious behavior to verify they are human-operated. This anti-bot measure has significant implications for businesses and marketers using the platform.

The European Union is pushing forward with legislation that could force tech companies to scan your private messages and photos. Here's what's at stake for digital privacy and encryption.
Apple's upcoming privacy enhancements final release could include surprising additions beyond typical security updates. Industry insiders reveal features that may reshape digital privacy standards.
LiteLLM versions 1.82.7 and 1.82.8 on PyPI were compromised in a supply chain attack. Discover how to check your dependencies, protect your credentials, and prevent future security breaches.

A supply-chain attack compromised the LiteLLM Python package, exposing developers to security risks. Discover what happened and how to protect your projects from similar threats.