- Home
- Technology
- LiteLLM PyPI Compromise: What Happened & How to Stay Safe
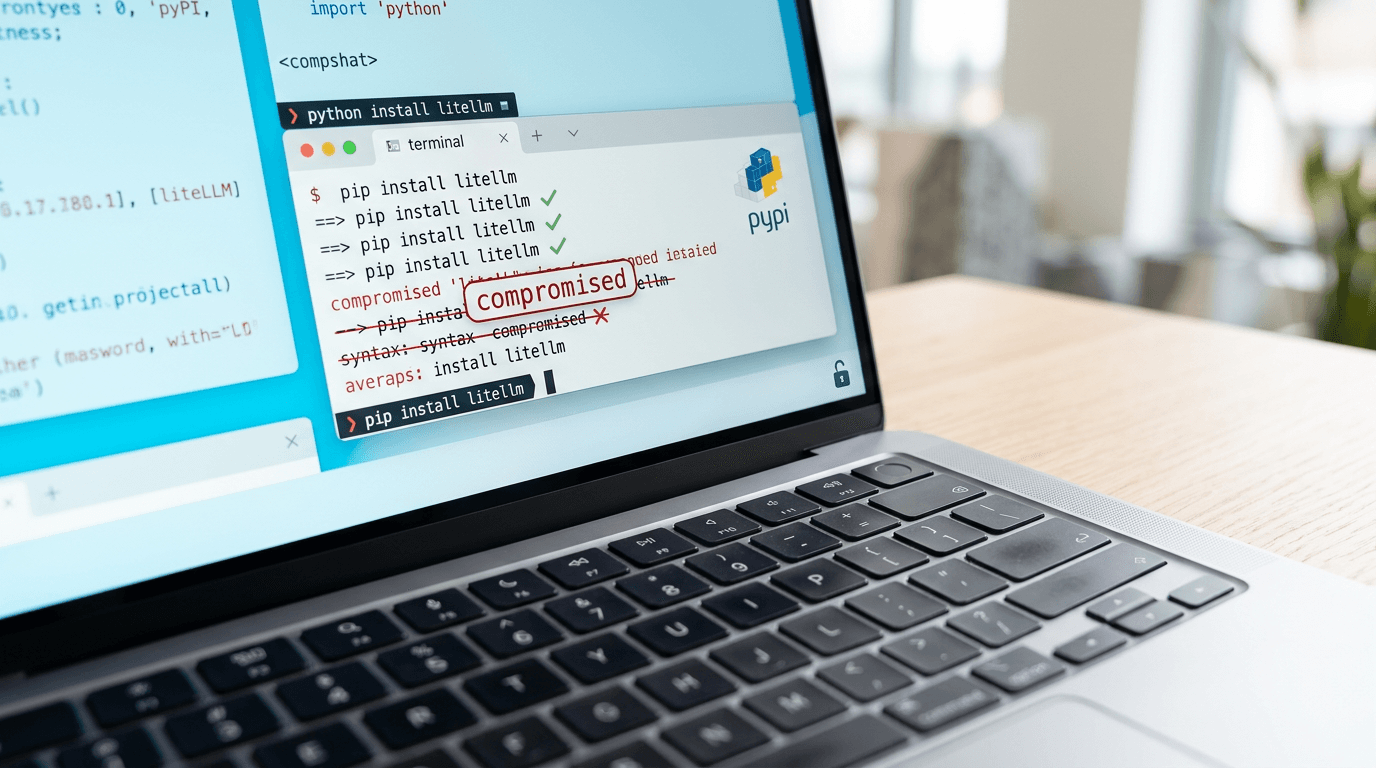
LiteLLM PyPI Compromise: What Happened & How to Stay Safe
LiteLLM versions 1.82.7 and 1.82.8 on PyPI were compromised in a supply chain attack. Discover how to check your dependencies, protect your credentials, and prevent future security breaches.
LiteLLM PyPI Compromise: Understanding the Security Breach
Learn more about litellm python package compromised by supply-chain attack
The Python Package Index (PyPI) ecosystem faced another security incident when LiteLLM versions 1.82.7 and 1.82.8 were compromised. This breach affects developers using the popular library for managing multiple LLM providers through a unified interface. Understanding what happened and how to protect your projects is critical for maintaining secure development environments.
Supply chain attacks targeting package repositories have become increasingly common. The LiteLLM compromise serves as a stark reminder that even widely-used packages can become vectors for malicious code distribution.
What Is LiteLLM and Why Does This Matter?
LiteLLM is a Python library that simplifies interactions with various large language model providers. It allows developers to switch between OpenAI, Anthropic, Cohere, and other LLM services using consistent API calls. The library has gained significant traction in the AI development community.
When a package with this level of adoption gets compromised, the potential blast radius extends across countless applications. Developers who automatically update dependencies or install these specific versions unknowingly introduce malicious code into their systems. The compromise potentially exposes API keys, credentials, and sensitive data handled by applications using the affected versions.
How Do Package Compromises Happen?
Attackers typically gain access to package maintainer accounts through several methods:
- Credential theft via phishing or password reuse
- Session hijacking through compromised developer machines
- Exploiting weak two-factor authentication implementations
- Social engineering targeting package maintainers
Once inside, attackers upload malicious versions that appear legitimate. These versions often include subtle backdoors or data exfiltration code designed to evade initial detection.
For a deep dive on microsoft's windows 11 fix: flowers after the beating, see our full guide
What Were the Compromised LiteLLM Versions Doing?
The malicious code in LiteLLM versions 1.82.7 and 1.82.8 likely contained functionality to steal sensitive information. While specific details about the payload vary by incident, compromised packages typically target environment variables, configuration files, and authentication tokens.
For a deep dive on iphone exploit kit leak: business security implications, see our full guide
Developers using these versions may have inadvertently sent API keys, database credentials, or other secrets to attacker-controlled servers. The code executes during package installation or import, making detection challenging without proper monitoring tools.
How Can You Identify If You're Affected?
Check your project dependencies immediately. Run "pip list | grep litellm" or examine your requirements.txt, Pipfile, or pyproject.toml files. If you find version 1.82.7 or 1.82.8 listed, your environment is compromised.
Review your application logs for unusual network activity during the period these packages were installed. Look for unexpected outbound connections or data transfers that coincide with package installation times.
What Immediate Actions Protect Your Projects?
If you discover the compromised versions in your environment, take swift action. Time is critical when dealing with potential credential exposure.
First, immediately uninstall the affected versions using "pip uninstall litellm". Then install a verified safe version, preferably 1.82.6 or earlier, or the latest patched release confirmed by the maintainers.
How Should You Rotate Compromised Credentials?
Rotate all credentials and API keys that could have been accessed by applications using the compromised packages. This includes:
- LLM provider API keys (OpenAI, Anthropic, etc.)
- Database connection strings and passwords
- Cloud service credentials (AWS, Azure, GCP)
- Internal service authentication tokens
- Any secrets stored in environment variables
Don't assume your credentials are safe. The cost of rotation is minimal compared to the potential damage from exposed credentials.
How Do You Scan for Indicators of Compromise?
Examine your system logs for suspicious activity. Look for unauthorized API calls, unexpected data access patterns, or new user accounts created during the exposure window. Network monitoring tools can reveal data exfiltration attempts to unknown IP addresses.
Consider running security scanning tools across your codebase and infrastructure. Tools like Bandit for Python code analysis or Trivy for container scanning can help identify lingering issues.
How Can You Prevent Future Supply Chain Attacks?
Dependency management requires a proactive security posture. Treating package installation as a potential security risk changes how you approach development workflows.
Implement dependency pinning in your projects. Specify exact versions in your requirements files rather than using loose version constraints. This prevents automatic updates to compromised versions before you can verify their safety.
Which Security Scanning Tools Should You Use?
Integrate automated security scanning into your CI/CD pipeline. Tools like Safety, Snyk, or GitHub Dependabot alert you to known vulnerabilities in your dependencies before they reach production.
Configure these tools to block builds when high-severity vulnerabilities are detected. This creates a security gate that prevents compromised packages from entering your production environment.
How Do You Implement Package Verification?
Verify package checksums and signatures when possible. PyPI supports package signing, though adoption remains limited. When available, signature verification provides cryptographic proof of package authenticity.
Consider using private package repositories for critical projects. Tools like Artifactory or AWS CodeArtifact let you mirror approved packages, giving you control over what enters your environment.
What Can We Learn from the LiteLLM Security Incident?
The LiteLLM compromise highlights systemic vulnerabilities in the open-source ecosystem. While PyPI has implemented security improvements, including mandatory two-factor authentication for maintainers, determined attackers continue finding ways through defenses.
Developers must adopt a zero-trust approach to dependencies. Every package represents potential risk, regardless of popularity or maintainer reputation. Building security practices around this reality creates more resilient systems.
What Role Does Community Vigilance Play?
The security community's quick detection and reporting of this compromise prevented wider damage. Monitoring tools, security researchers, and alert developers form a crucial defense layer against supply chain attacks.
Stay connected with security advisories for your critical dependencies. Follow project maintainers on social media, subscribe to security mailing lists, and participate in community discussions about package security.
How Should You Move Forward Securely?
The compromised LiteLLM versions serve as an important case study in supply chain security. As AI development accelerates and LLM integration becomes standard, securing the tools we use grows increasingly critical.
Implement the protective measures outlined above. Regular security audits, credential rotation, and dependency monitoring should become standard practice rather than reactive measures. The open-source ecosystem thrives on trust, but that trust must be verified through consistent security practices.
Continue learning: Next, explore reddit ceo plans to hire recent grads over ai cuts
Stay informed about security incidents affecting your technology stack. The faster you respond to compromises, the less damage they can inflict on your systems and data. Building security awareness into your development culture protects not just your projects but the broader community that depends on secure software.
Related Articles
AI's Role in Unveiling ICE Officers' Identities
AI unmasking ICE officers underscores a shift towards transparent law enforcement, raising questions about privacy and ethics in the digital age.
Sep 2, 2025
AI's Role in Unveiling ICE Officers' Identities
AI is revolutionizing transparency in law enforcement by identifying ICE officers, raising critical ethical and cybersecurity questions.
Sep 2, 2025
AI Tools Reveal Identities of ICE Officers Online
AI's emerging role in unmasking ICE officers spotlights the intersection of technology, privacy, and ethics, sparking a crucial societal debate.
Sep 2, 2025
