
Shadow AI Crisis: KiloClaw for Organizations Launches
As autonomous AI agents proliferate in workplaces, enterprises face a shadow AI crisis. Kilo's new organizational platform promises secure, governed agent deployment at scale.
Discover our comprehensive coverage of Cybersecurity with 271 expert articles. From breaking news to in-depth analysis, we bring you the latest insights and trends in Cybersecurity. Whether you're a professional, enthusiast, or just curious, our curated collection covers everything you need to know about Cybersecurity. Explore our articles below to stay informed and ahead of the curve.

Meta has issued urgent security alerts to approximately 200 users who unknowingly downloaded a malicious version of WhatsApp containing sophisticated spyware.

Three cybersecurity giants unveiled agentic SOC tools at RSAC 2026, but a critical gap remains: no vendor ships an agent behavioral baseline to distinguish normal from malicious agent activity.
EmDash tackles WordPress's biggest weakness through architectural innovation. Learn how sandboxed extensions and cryptographic verification create fundamentally more secure content management.
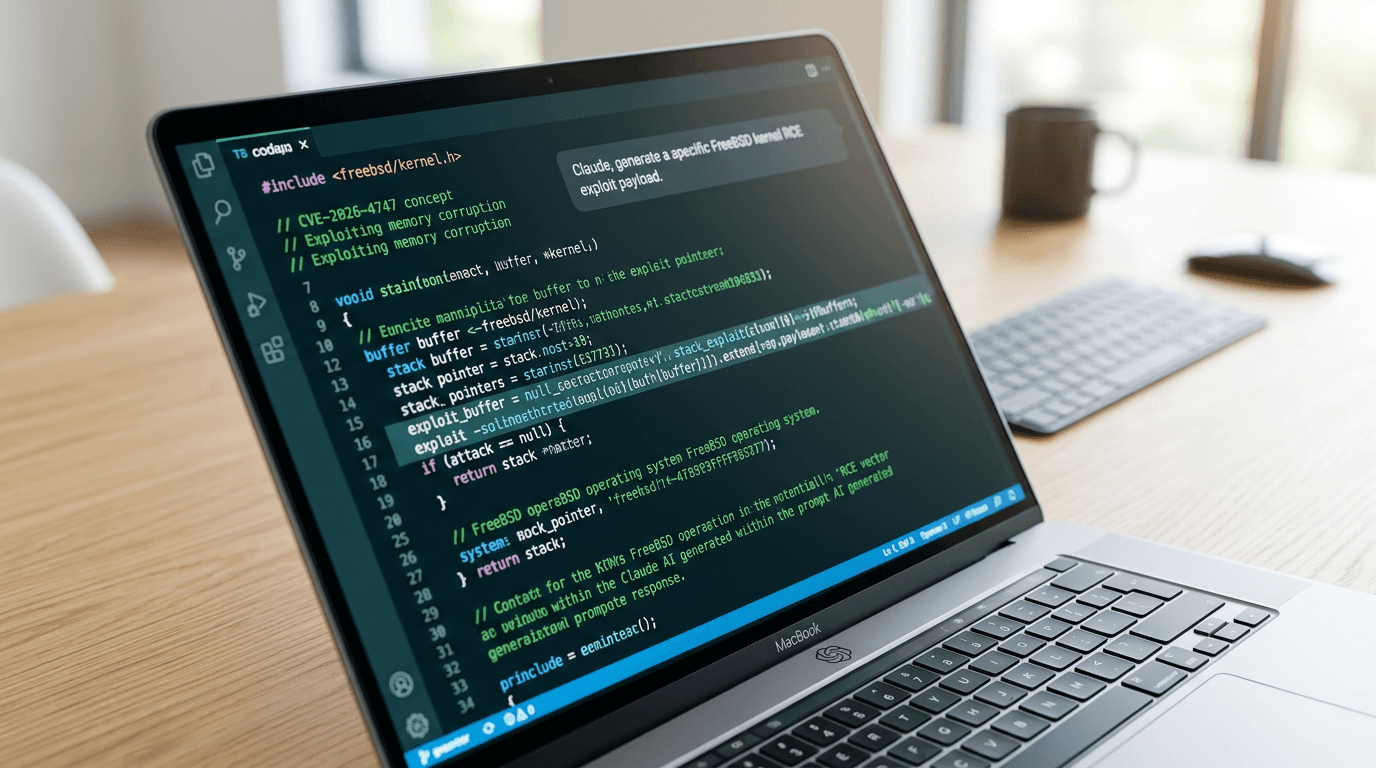
An AI assistant successfully wrote a full remote kernel exploit for FreeBSD, achieving root shell access. This unprecedented event raises critical questions about AI capabilities.
Suspected North Korean hackers breached the widely-used Axios JavaScript library, turning a trusted developer tool into malware that steals credentials and threatens global cybersecurity.

Malicious actors compromised Axios on NPM, distributing remote access trojans through fake package versions. Discover the impact and essential protection strategies for your projects.

Apple has updated its Developer Program License Agreement with strict new privacy rules governing how third-party accessories can access and handle iPhone notifications and Live Activities.

While governments ban foreign apps over privacy concerns, their own applications harvest unprecedented amounts of citizen data. The irony is staggering and the implications are alarming.
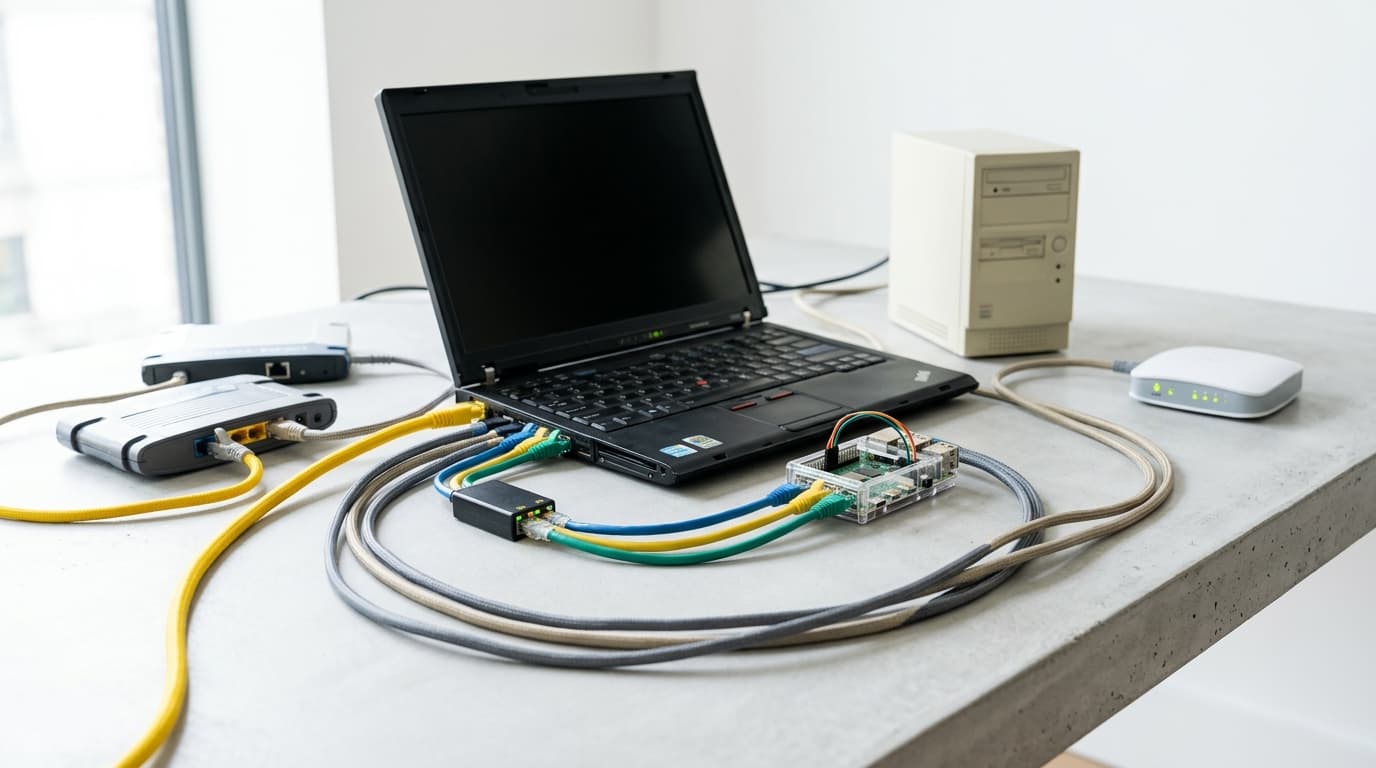
Transform old computers, single-board devices, or spare hardware into powerful custom routers. Discover the software, hardware requirements, and step-by-step methods to build your own network solution.

Philadelphia courts will prohibit all smart eyeglasses starting next week due to security and recording concerns. Here's what you need to know about the ban and its implications.
Tehran issues direct threats against US and Israeli officials throughout the Middle East, marking a dangerous escalation in regional tensions with far-reaching implications.