- Home
- Technology
- EmDash: WordPress Successor Solving Plugin Security Issues
EmDash: WordPress Successor Solving Plugin Security Issues
EmDash tackles WordPress's biggest weakness through architectural innovation. Learn how sandboxed extensions and cryptographic verification create fundamentally more secure content management.
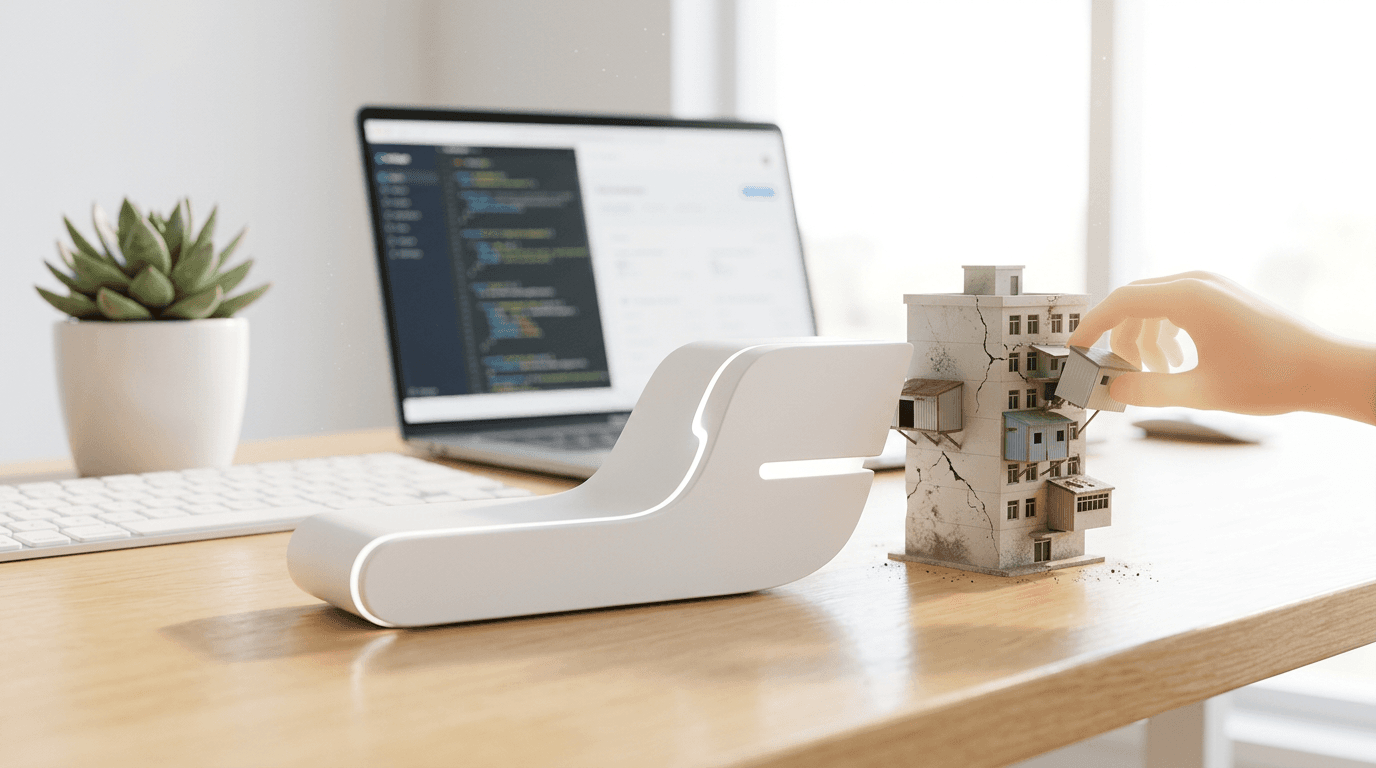
WordPress Security Crisis: How EmDash Fixes Plugin Vulnerabilities
Learn more about claude ai wrote freebsd kernel rce exploit (cve-2026-4747)
WordPress powers over 40% of the web, yet security vulnerabilities continue to plague its ecosystem. Plugin-related breaches account for nearly 90% of all WordPress security incidents, leaving millions of websites exposed to attacks. EmDash emerges as a spiritual successor to WordPress, reimagining content management with security baked into its foundation rather than bolted on as an afterthought.
What Is EmDash and Why Does It Matter?
EmDash represents a fundamental rethinking of how content management systems handle extensibility. While WordPress revolutionized web publishing by making it accessible to non-developers, its plugin architecture has become its Achilles heel.
EmDash addresses this by implementing a security-first approach to extensions without sacrificing the flexibility that made WordPress dominant. The platform maintains familiar WordPress concepts while introducing modern security paradigms.
Developers can extend functionality, but within strict sandboxed environments that prevent malicious code from compromising entire installations. This balance between openness and security positions EmDash as a viable alternative for organizations tired of constant security patches.
Why Are WordPress Plugins So Vulnerable?
WordPress's plugin ecosystem contains over 60,000 plugins, but this abundance creates significant risk. Third-party code runs with extensive permissions, accessing databases, file systems, and user data without meaningful isolation. When a single plugin gets compromised, attackers gain complete system access.
Security researchers identified over 10,000 vulnerabilities in WordPress plugins during the past year alone. Many site owners install plugins without vetting code quality or security practices. The average WordPress site runs 20-30 plugins, multiplying potential attack vectors exponentially.
How Does EmDash Solve Plugin Security Problems?
EmDash implements several architectural innovations that fundamentally change how extensions interact with the core system. These structural changes eliminate entire categories of vulnerabilities.
Sandboxed Extension Environments
For a deep dive on cern levels up with new superconducting karts, see our full guide
Every EmDash extension runs in an isolated sandbox with explicitly granted permissions. Extensions cannot access system resources, databases, or user data without declaring their needs upfront.
The platform uses containerization technology similar to modern application deployment strategies. This approach mirrors mobile app permissions, where users understand exactly what access they grant.
For a deep dive on track artemis 2 with your unistellar smart telescope, see our full guide
An extension requesting file system access triggers user approval workflows. Suspicious permission requests immediately raise red flags before installation completes.
Cryptographic Verification and Code Signing
All EmDash extensions must pass cryptographic verification before installation. Developers sign their code with private keys, creating tamper-proof signatures that the platform validates. Modified or compromised extensions fail verification and refuse to load.
The signing process includes automated security scans that detect common vulnerability patterns. SQL injection risks, cross-site scripting vectors, and insecure file operations trigger immediate rejection.
Only code passing these automated checks reaches the extension marketplace.
What Security Features Does EmDash Include?
Beyond sandboxing and code signing, EmDash incorporates multiple security layers:
- Runtime monitoring detects anomalous extension behavior and automatically disables suspicious code
- Dependency tracking alerts administrators when extension libraries contain known vulnerabilities
- Automatic security updates apply to the core system without breaking extension compatibility
- Zero-trust architecture requires extensions to prove legitimacy with every operation rather than receiving blanket permissions
- Audit logging tracks all extension activities for forensic analysis after security incidents
These features create defense in depth. Compromising an EmDash installation requires bypassing multiple independent security controls, dramatically raising attacker costs.
How Does EmDash Compare to WordPress?
While EmDash draws inspiration from WordPress, significant architectural differences separate them. Understanding these distinctions helps evaluate whether migration makes sense for specific use cases.
Extension API Design
WordPress uses action hooks and filters that give extensions deep system access. EmDash implements a capability-based API where extensions request specific permissions.
This shift requires developers to think differently about extension architecture but results in more secure, maintainable code. The EmDash API includes modern features like asynchronous operations, event streaming, and reactive data flows.
These patterns align with contemporary development practices while maintaining security boundaries.
Performance and Scalability
EmDash's architecture delivers performance improvements alongside security enhancements. Sandboxed extensions enable aggressive caching strategies impossible in WordPress. The platform can cache extension outputs independently, reducing database queries and server load.
Benchmark tests show EmDash handling 3-5 times more concurrent requests than equivalent WordPress installations. The security overhead from sandboxing proves negligible compared to performance gains from modern caching and optimization techniques.
Is EmDash Ready for Production Use?
EmDash currently exists in public beta, with several high-profile organizations testing deployments. The core platform demonstrates stability, but the extension ecosystem remains smaller than WordPress's massive library.
Developers familiar with WordPress can learn EmDash relatively quickly. The team provides migration tools that convert simple WordPress themes and plugins to EmDash extensions. Complex plugins requiring deep WordPress integration need manual rewrites, but the security benefits often justify the investment.
Who Should Consider EmDash?
EmDash makes particular sense for organizations with strict security requirements:
- Financial services companies handling sensitive customer data
- Healthcare providers subject to HIPAA compliance requirements
- Government agencies needing certified secure platforms
- Enterprise businesses tired of WordPress security maintenance overhead
Smaller sites or hobbyist blogs may find WordPress's mature ecosystem more practical despite security concerns. EmDash targets users who prioritize security over extension quantity.
What Does the Future Hold for Secure Content Management?
EmDash represents broader industry trends toward security-first software architecture. As cyber threats grow more sophisticated, platforms must evolve beyond patching vulnerabilities reactively.
Building security into foundational architecture prevents entire vulnerability classes rather than playing endless whack-a-mole. The platform's open-source nature means community contributions will shape its evolution.
Early adopters influence design decisions and extension standards. This collaborative approach mirrors WordPress's community-driven success while learning from its security shortcomings.
How Should You Plan Your Migration?
Organizations considering EmDash should plan phased migrations rather than wholesale replacements. Start with non-critical sites to gain operational experience. Test extension availability for required functionality before committing production workloads.
The EmDash team offers professional migration services for complex deployments. These services include security audits, custom extension development, and staff training.
Investment in proper migration reduces risks and accelerates time-to-value.
Conclusion: Is EmDash the WordPress Successor We Need?
EmDash tackles WordPress's most persistent problem through architectural innovation rather than incremental improvements. Its sandboxed extensions, cryptographic verification, and zero-trust design create fundamentally more secure content management.
While the platform's youth means smaller extension libraries and less community support, organizations prioritizing security find compelling value. The next few years will determine whether EmDash gains mainstream adoption or remains a niche alternative.
Continue learning: Next, explore she built an ai solution at 3 a.m.: a ceo's blueprint
Its technical foundation addresses real problems plaguing WordPress users daily. Success depends on building a vibrant extension ecosystem while maintaining uncompromising security standards. For security-conscious organizations, EmDash deserves serious evaluation as WordPress's spiritual successor.
Related Articles

AI's Role in Unveiling ICE Officers' Identities
AI unmasking ICE officers underscores a shift towards transparent law enforcement, raising questions about privacy and ethics in the digital age.
Sep 2, 2025

Age Verification Laws: Impact on Web Traffic Trends
Discover the paradox of age verification laws: How compliance impacts web traffic and the tech innovations shaping the future of digital content access.
Sep 2, 2025

Merz Tags Putin as Top War Criminal in Modern Era
Merz's assertion that Putin could be this era's gravest war criminal triggers a global debate on cybersecurity, AI, and warfare ethics.
Sep 3, 2025
Comments
Loading comments...
