- Home
- Technology
- Meta Alerts iPhone Users: Fake WhatsApp Spyware Threat
Meta Alerts iPhone Users: Fake WhatsApp Spyware Threat
Meta has issued urgent security alerts to approximately 200 users who unknowingly downloaded a malicious version of WhatsApp containing sophisticated spyware.

Meta Warns 200 iPhone Users: Fake WhatsApp Spyware Attack Exposed
Learn more about agentic soc tools at rsac 2026: the behavioral gap
Meta has issued urgent security alerts to approximately 200 iPhone users who fell victim to a sophisticated phishing campaign. These users unknowingly downloaded a fake version of WhatsApp loaded with spyware designed to steal personal data and monitor communications. This incident highlights a growing concern for iOS users who often believe their devices are immune to such threats.
The attack represents a significant breach in mobile security, particularly troubling for iPhone users who rely on Apple's reputation for strong security measures. Understanding how this attack succeeded matters for anyone using messaging apps on their devices.
How Did the Fake WhatsApp Spyware Attack Unfold?
According to Italy's Agenzia Nazionale Stampa Associata (ANSA), the attack targeted users through a carefully orchestrated social engineering campaign. Victims received convincing messages directing them to download what appeared to be a legitimate WhatsApp update or alternative version.
The fake WhatsApp application bypassed Apple's App Store entirely. Attackers exploited enterprise certificate systems and configuration profiles that allow organizations to distribute internal apps to employees. This method circumvents Apple's standard security checks, creating a dangerous loophole that sophisticated threat actors exploit.
Once installed, the malicious app granted attackers extensive access to user data. The spyware monitored messages, accessed contacts, tracked location data, and potentially intercepted calls. This level of access transformed a user's iPhone into a surveillance device without their knowledge.
What Makes This iPhone Spyware Attack Different?
This incident stands out because it specifically targeted iPhone users, a demographic typically less affected by mobile malware. Apple's closed ecosystem usually provides strong protection against unauthorized apps. However, this attack demonstrates that no platform remains completely invulnerable when users manually install malicious software.
The sophistication of the fake WhatsApp version also raises concerns. The app mimicked WhatsApp's interface closely enough to avoid immediate suspicion. Users continued their normal messaging activities while the spyware operated silently in the background.
How Did Meta Respond to the Security Breach?
Meta acted swiftly upon discovering the fake WhatsApp distribution campaign. The company identified approximately 200 affected users and sent direct security alerts through official channels. These notifications informed users about the compromise and provided specific instructions for removing the malicious software.
For a deep dive on judge denies new trial for cop in georgia teen's death, see our full guide
The social media giant also collaborated with cybersecurity researchers to analyze the spyware's capabilities. This investigation revealed the scope of data collection and helped Meta develop countermeasures to prevent similar attacks. The company has not disclosed the geographic distribution of affected users beyond confirming reports from Italian media.
Meta emphasized that the official WhatsApp application available through the App Store remains secure. The company urged all users to verify they downloaded WhatsApp only from official sources and to remain skeptical of any messages requesting alternative installations.
For a deep dive on emdash: wordpress successor solving plugin security issues, see our full guide
Who Was Behind the Fake WhatsApp Attack?
While Meta has not publicly identified the attackers, the sophistication suggests involvement by organized cybercriminal groups or state-sponsored actors. The resources required to create a convincing fake app and distribute it through compromised enterprise certificates indicate advanced capabilities.
Security researchers note that spyware campaigns of this nature often target specific individuals rather than conducting broad attacks. Journalists, activists, business executives, and government officials frequently become targets for surveillance operations using these methods.
How Can iPhone Users Protect Themselves From Fake Apps?
Protecting yourself from fake app attacks requires vigilance and adherence to security best practices. iPhone users should implement several key strategies to minimize their risk of falling victim to similar schemes.
Download Apps Only From Official Sources
Always download WhatsApp and other applications exclusively from Apple's App Store. Never follow links in messages, emails, or websites that prompt you to install apps through alternative methods. The App Store provides Apple's security vetting, which significantly reduces malware risks.
If someone sends you a link to download an app update, ignore it. Check for updates manually within the App Store instead. Legitimate app developers never distribute iOS apps through direct download links or third-party websites.
How Do You Recognize Configuration Profile Warnings?
iOS displays prominent warnings when installing configuration profiles or enterprise certificates. These warnings appear for good reason. Unless you work for an organization that legitimately requires such profiles for work apps, you should never install them.
The installation process requires multiple confirmation steps specifically because it grants significant system access. If you accidentally begin installing a suspicious profile, cancel immediately and delete any downloaded files.
Key Security Practices to Follow:
- Enable two-factor authentication on your Apple ID and all messaging apps
- Regularly review installed apps and remove unfamiliar ones
- Check Settings > General > VPN & Device Management for suspicious profiles
- Keep iOS updated to the latest version for security patches
- Remain skeptical of urgent messages requesting immediate action
- Verify sender identity before clicking links or downloading files
What Should You Do If You Downloaded the Fake WhatsApp?
If you received a security alert from Meta or suspect you installed a fake WhatsApp version, take immediate action to secure your device and data. Time matters when dealing with spyware infections.
First, delete the suspicious application immediately. Then navigate to Settings > General > VPN & Device Management and remove any unfamiliar configuration profiles. These profiles often persist even after deleting the associated app, maintaining the attacker's access to your device.
Next, change passwords for all important accounts, especially email, banking, and social media. The spyware may have captured your existing credentials. Enable two-factor authentication wherever possible to add an extra security layer.
Should You Reset Your iPhone After a Spyware Attack?
For maximum security, consider performing a complete factory reset of your iPhone after backing up essential data. This approach ensures complete removal of any persistent malware or configuration changes. Restore your data only from backups created before you installed the suspicious app.
Before restoring, verify that your backup does not contain the malicious app or profiles. Check your backup contents and exclude any suspicious items from the restoration process.
What Are the Broader Implications for Mobile Security?
This incident reveals important truths about mobile security in 2024. Even Apple's tightly controlled ecosystem cannot protect users who bypass security measures through social engineering. The human element remains the weakest link in cybersecurity.
The fake WhatsApp attack also demonstrates how attackers increasingly target mobile devices. Smartphones store increasingly valuable personal and professional data as they become primary computing devices for many users. This makes them attractive targets for sophisticated threat actors.
What Does This Mean for Apple's Security Approach?
Apple faces pressure to close the enterprise certificate loophole that enabled this attack. While legitimate businesses need ways to distribute internal apps, the current system allows too much potential for abuse. Apple may need to implement additional verification steps or monitoring for enterprise certificate usage.
The company has historically been reactive rather than proactive in addressing security vulnerabilities. However, as attacks like this gain media attention, Apple may accelerate efforts to strengthen iOS security mechanisms without compromising legitimate enterprise functionality.
What Lessons Can We Learn From the Fake WhatsApp Incident?
This security breach offers valuable lessons for all smartphone users, regardless of platform. The most important takeaway? Security requires constant vigilance. No device or operating system provides automatic protection against all threats.
Users must develop healthy skepticism about unexpected messages, download requests, and installation prompts. When something seems unusual or creates urgency, slow down and verify authenticity through official channels.
Organizations also bear responsibility for educating employees about mobile security threats. Many users lack awareness about configuration profiles, enterprise certificates, and the risks they pose when misused. Regular security training can prevent successful social engineering attacks.
What Does the Future Hold for Mobile Messaging Security?
Messaging apps will continue facing security challenges as they become more central to personal and professional communication. End-to-end encryption protects message contents, but it cannot prevent users from installing malicious versions of apps or granting excessive permissions.
The industry needs better mechanisms for verifying app authenticity beyond app store distribution. Digital signatures, certificate pinning, and other technical measures can help, but user education remains paramount. People must understand the risks and recognize warning signs of potential attacks.
Protecting Your iPhone From Spyware Attacks
The fake WhatsApp spyware incident serves as a wake-up call for iPhone users who may have grown complacent about mobile security. Meta's prompt notification of affected users demonstrates responsible disclosure, but prevention beats remediation.
Download apps only from official sources. Scrutinize installation requests carefully. Maintain healthy skepticism about unexpected messages. These practices significantly reduce your vulnerability to similar attacks.
Continue learning: Next, explore claude ai wrote freebsd kernel rce exploit (cve-2026-4747)
This incident proves that strong security requires both robust technical measures and informed, vigilant users who understand the threats they face. Your iPhone's security depends not just on Apple's protections, but on your own awareness and actions.
Related Articles
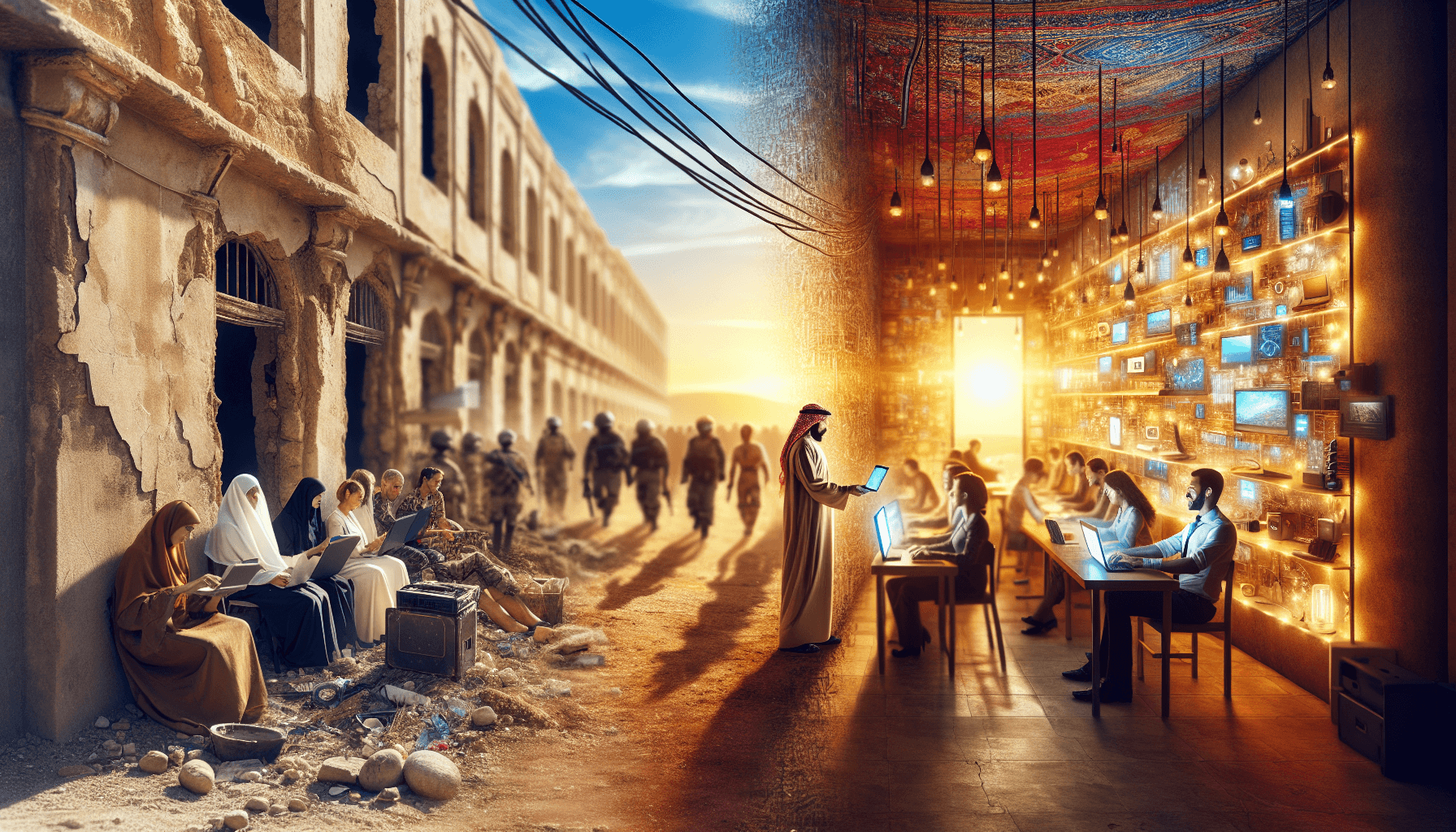
Transforming Gaza: From Conflict Zone to Tech Hub
A leaked plan from the Trump administration reveals a bold strategy to turn Gaza into a thriving high-tech hub. Discover the potential.
Sep 3, 2025
AI Tools Reveal Identities of ICE Officers Online
AI's emerging role in unmasking ICE officers spotlights the intersection of technology, privacy, and ethics, sparking a crucial societal debate.
Sep 2, 2025
AI's Role in Unveiling ICE Officers' Identities
AI unmasking ICE officers underscores a shift towards transparent law enforcement, raising questions about privacy and ethics in the digital age.
Sep 2, 2025