- Home
- Technology
- Wikipedia Admin Account Compromise Triggers Read-Only Mode
Wikipedia Admin Account Compromise Triggers Read-Only Mode
A major security breach forced Wikipedia into read-only mode as multiple administrator accounts were compromised, raising serious questions about the platform's security infrastructure.

Wikipedia Admin Account Compromise Forces Emergency Lockdown
Learn more about record-breaking photodetector captures light in 125 picoseconds
The world's largest online encyclopedia faced an unprecedented security crisis when Wikipedia entered read-only mode following a mass admin account compromise. This incident affected millions of users worldwide and exposed vulnerabilities in one of the internet's most trusted information sources. The temporary lockdown prevented all editing activities while security teams worked to contain the breach.
The compromise represents one of the most significant security incidents in Wikipedia's two-decade history. Administrator accounts hold extraordinary privileges, including the ability to delete pages, block users, and modify protected content. When multiple admin accounts fall into the wrong hands simultaneously, the potential for widespread misinformation becomes alarmingly real.
What Happened During the Wikipedia Security Breach?
The security incident began when Wikimedia Foundation's security team detected unusual activity across multiple administrator accounts. These accounts showed login patterns inconsistent with their typical usage, including access from unfamiliar geographic locations and rapid-fire editing attempts. The team immediately initiated emergency protocols.
Investigators discovered that attackers had gained access through a sophisticated credential stuffing attack. This method uses username and password combinations stolen from other data breaches to access accounts where users recycled their credentials. The attack targeted administrators who had not enabled two-factor authentication.
The Wikimedia Foundation placed the entire platform in read-only mode within hours of detection. This decisive action prevented attackers from making unauthorized changes while security teams conducted a comprehensive audit. Users could still view articles, but all editing functions were temporarily disabled.
How Many Wikipedia Admin Accounts Were Compromised?
The Wikimedia Foundation has not disclosed the exact number of compromised accounts. Security researchers estimate that dozens of administrator accounts across multiple language editions were affected. The breach impacted both highly active administrators and those with sporadic editing patterns.
The attackers demonstrated sophisticated knowledge of Wikipedia's administrative structure. They specifically targeted accounts with elevated privileges, including bureaucrats and checkusers who possess even greater access than standard administrators. This strategic approach suggests careful planning rather than opportunistic attacks.
How Did Wikipedia Respond to the Security Breach?
For a deep dive on ozempic-like drugs may help heart recovery after attack, see our full guide
What Immediate Security Measures Were Implemented?
The Wikimedia Foundation's security team executed a multi-layered response strategy. They immediately revoked all active administrator sessions, forcing every admin to log in again with fresh credentials. This action disconnected any attacker currently accessing a compromised account.
For a deep dive on ios exploit kit with 23 attacks stopped by lockdown mode, see our full guide
Security engineers implemented these emergency measures:
- Mandatory password resets for all affected administrator accounts
- Temporary suspension of elevated privileges until identity verification
- Enhanced monitoring of all administrative actions across the platform
- Deployment of additional intrusion detection systems
- Implementation of stricter rate limiting on login attempts
The technical team conducted forensic analysis of server logs to identify unauthorized changes made during the compromise window. This process involved reviewing thousands of edits, deletions, and administrative actions to separate legitimate activity from malicious interference.
Why Did Two-Factor Authentication Become Mandatory?
Following the breach, the Wikimedia Foundation announced that two-factor authentication would become mandatory for all users with elevated privileges. This requirement represents a significant policy shift for an organization that has traditionally emphasized open access and minimal barriers to participation.
Two-factor authentication requires users to provide a second form of verification beyond their password. This typically includes a temporary code generated by a smartphone app or sent via text message. This security measure dramatically reduces the effectiveness of credential stuffing attacks.
The implementation timeline gave existing administrators 30 days to configure two-factor authentication on their accounts. Those who failed to comply faced automatic suspension of their elevated privileges.
Why Does This Wikipedia Breach Matter for Online Platforms?
The Wikipedia admin account compromise serves as a stark reminder that no platform is immune to security threats. Wikipedia's reputation as a reliable information source makes it an attractive target for actors seeking to spread misinformation or cause disruption. The breach demonstrates how attackers increasingly focus on compromising privileged accounts rather than exploiting software vulnerabilities.
This incident highlights the ongoing challenge of balancing accessibility with security. Wikipedia's open editing model has been fundamental to its success, allowing anyone to contribute knowledge. However, this openness creates unique security considerations.
What Are the Implications for User Trust?
User trust forms the foundation of Wikipedia's authority as an information source. When security breaches threaten that trust, the entire platform's credibility suffers. The incident prompted discussions about whether Wikipedia's volunteer-based administrative model remains sustainable in an era of sophisticated cyber threats.
The breach raised questions about the security practices of volunteer administrators. Unlike professional system administrators who receive regular security training, Wikipedia admins are volunteers with varying levels of cybersecurity awareness. This diversity creates potential weak points that attackers can exploit.
What Can Organizations Learn From This Security Incident?
What Security Lessons Does the Wikipedia Breach Teach?
The Wikipedia breach offers valuable lessons for organizations managing platforms with privileged user accounts. First, mandatory multi-factor authentication should be non-negotiable for any account with elevated privileges. The relatively low cost and minimal user friction make this security measure essential.
Second, organizations must implement robust monitoring systems that detect anomalous login patterns. Geographic location tracking, device fingerprinting, and behavioral analysis can identify compromised accounts before significant damage occurs. These systems should trigger automatic alerts when suspicious activity is detected.
Third, regular security audits of privileged accounts help identify dormant or underutilized accounts that may have lapsed security practices. Organizations should implement policies requiring periodic re-verification of identity for accounts with elevated access.
How Can Platform Users Protect Their Accounts?
Individual users can take several steps to protect their accounts on Wikipedia and other platforms:
- Use unique passwords for every online account
- Enable two-factor authentication wherever available
- Regularly review account activity logs for unauthorized access
- Update passwords immediately after receiving breach notifications from other services
- Use a reputable password manager to generate and store complex passwords
These practices significantly reduce vulnerability to credential stuffing attacks and other common compromise methods. While they require some initial setup effort, the long-term security benefits far outweigh the inconvenience.
How Does This Fit Into Broader Platform Security Trends?
This incident occurs against a backdrop of increasing cyber threats targeting online platforms. Attackers have shifted focus from exploiting technical vulnerabilities to compromising user accounts, particularly those with administrative privileges. This trend reflects the reality that human factors often represent the weakest link in security chains.
The rise of credential stuffing attacks correlates with the proliferation of data breaches across the internet. Billions of username and password combinations circulate on dark web marketplaces, providing attackers with extensive databases for automated login attempts. As long as users continue recycling passwords across multiple services, these attacks will remain effective.
How Does Wikipedia's Response Compare to Other Platforms?
Wikipedia's rapid response and transparent communication stand in contrast to some other platforms that have experienced similar breaches. The decision to enter read-only mode, while disruptive, demonstrated a commitment to security over continuous operation. This approach prioritized protecting content integrity and user trust.
Other platforms have sometimes delayed public disclosure of breaches or minimized their severity, leading to greater long-term damage to user trust. Wikipedia's relatively open acknowledgment of the incident and clear communication about remediation steps helped maintain credibility.
What Security Improvements Is Wikipedia Implementing?
The Wikimedia Foundation has announced plans for comprehensive security infrastructure improvements following the breach. These enhancements include advanced threat detection systems, expanded security team resources, and improved training programs for volunteer administrators. The organization has also committed to regular third-party security audits.
These investments represent a significant commitment for a nonprofit organization that relies heavily on donations. However, the foundation recognizes that maintaining Wikipedia's reputation as a trustworthy information source requires robust security measures. The cost of prevention pales in comparison to the potential damage from successful attacks.
What Are the Key Takeaways From the Wikipedia Security Breach?
The mass admin account compromise that forced Wikipedia into read-only mode serves as a critical reminder that even the most trusted online platforms face serious security threats. The incident demonstrated both the vulnerabilities inherent in volunteer-managed systems and the importance of rapid, decisive response to security breaches.
Key takeaways include the absolute necessity of multi-factor authentication for privileged accounts, the ongoing threat posed by credential stuffing attacks, and the critical importance of proactive security monitoring. As cyber threats continue evolving, platforms must continuously adapt their security practices to protect both their content and their users' trust.
Continue learning: Next, explore macbook neo: why videographers and photographers should skip it
Wikipedia's experience offers valuable lessons for organizations and individuals about the paramount importance of cybersecurity in our increasingly connected world. The breach underscores that security remains an ongoing challenge requiring constant vigilance and adaptation.
Related Articles
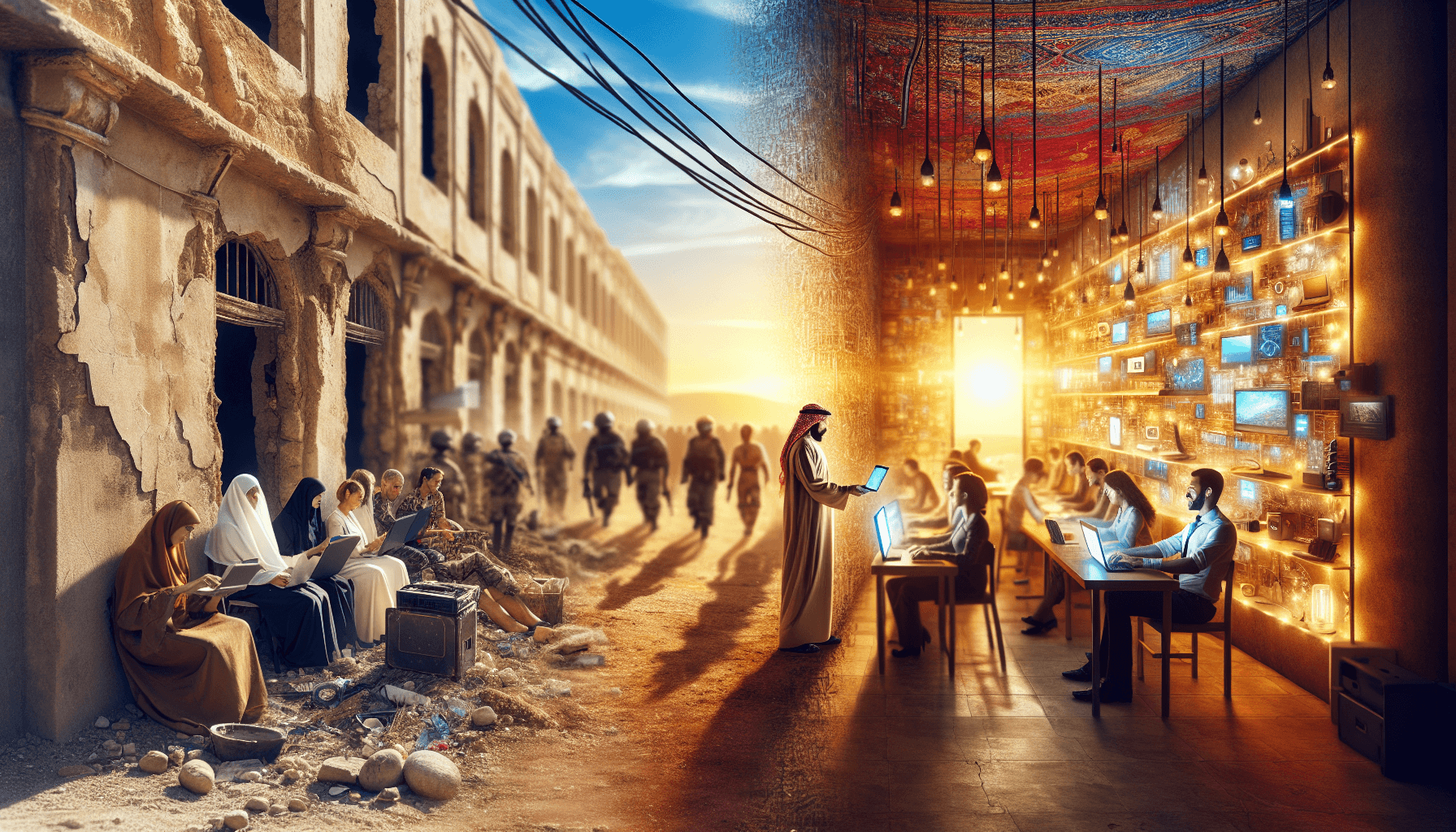
Transforming Gaza: From Conflict Zone to Tech Hub
A leaked plan from the Trump administration reveals a bold strategy to turn Gaza into a thriving high-tech hub. Discover the potential.
Sep 3, 2025
Gaza's Tech Revolution: Trump's Bold High-Tech Vision
A leaked plan from the Trump administration unveils a vision to make Gaza a high-tech hub, focusing on AI, cybersecurity, and digital innovation.
Sep 3, 2025
AI Tools Reveal Identities of ICE Officers Online
AI's emerging role in unmasking ICE officers spotlights the intersection of technology, privacy, and ethics, sparking a crucial societal debate.
Sep 2, 2025