- Home
- Technology
- iOS Exploit Kit With 23 Attacks Stopped by Lockdown Mode
iOS Exploit Kit With 23 Attacks Stopped by Lockdown Mode
A powerful iOS exploit kit called Coruna has been circulating among cybercriminals, but Apple's Lockdown Mode stops it in its tracks. Here's what iPhone users need to know.

The iOS Exploit Kit With 23 Attacks That Lockdown Mode Defeats
Learn more about macbook neo: why videographers and photographers should skip it
Cybersecurity researchers have uncovered one of the most sophisticated iPhone attack frameworks ever documented. Google's Threat Intelligence Group (GTIG) recently published findings about "Coruna," an iOS exploit kit containing 23 separate attacks that target iPhones running iOS versions 13.0 through 17.2.1.
The good news? Apple's Lockdown Mode stops this entire arsenal cold.
The discovery reveals a troubling underground market where surveillance tools change hands between nation-state actors and cybercriminals. What started as a commercial surveillance product ended up weaponized by Russian espionage groups and Chinese financial hackers. For iPhone users, this serves as a stark reminder that sophisticated threats exist, but also that Apple's security features work when you need them most.
What Makes the Coruna Exploit Kit So Dangerous?
Coruna represents a new level of sophistication in mobile exploitation. The kit spans four years of iOS versions, meaning attackers can target nearly any iPhone that hasn't been updated recently. GTIG describes it as one of the most comprehensive iOS exploit toolkits ever documented publicly.
The framework operates with remarkable intelligence. When a victim visits an infected website, Coruna automatically fingerprints the device to determine the exact iPhone model and iOS version. It then selects the most appropriate exploit from its arsenal of 23 attacks, maximizing the chances of successful compromise.
The engineering behind Coruna sets it apart from typical attack tools. Developers packaged the exploits in a custom format they invented themselves, making analysis more difficult. Strong encryption scrambles the attack code, preventing security researchers from easily intercepting and studying it.
The kit even includes detailed documentation written in English, explaining how each component functions.
How Did the Exploit Kit Travel Through Cybercrime Networks?
The journey of Coruna through various threat actors reveals an active marketplace for second-hand exploits. GTIG first spotted the framework in February 2025, deployed by a customer of a commercial surveillance vendor. These vendors typically sell their tools to government agencies and law enforcement.
By summer 2025, the same framework appeared in watering hole attacks conducted by a suspected Russian espionage group. These attackers compromised websites that Ukrainian users were likely to visit, lying in wait for their targets.
The shift from commercial surveillance to nation-state espionage represents a significant escalation.
Late in 2025, a China-based financially motivated actor deployed Coruna across a large network of fake financial and cryptocurrency websites. This third iteration targeted everyday users rather than specific intelligence targets. GTIG could not determine exactly how the exploit kit passed from actor to actor, but the progression suggests a thriving underground market for these tools.
Why Does Lockdown Mode Stop Coruna Completely?
Apple's Lockdown Mode proves its worth against sophisticated threats. When Coruna detects that a target device has Lockdown Mode enabled, it immediately aborts the attack. The exploit kit doesn't even attempt to compromise the device.
For a deep dive on new drug cuts seizures 91% in children with rare epilepsy, see our full guide
Lockdown Mode works by restricting certain iPhone features that attackers commonly exploit. The feature blocks most message attachment types, disables link previews, and prevents complex web technologies that can harbor exploits. These restrictions create an environment where sophisticated exploit kits like Coruna cannot function.
The fact that Coruna's developers programmed it to recognize and avoid Lockdown Mode speaks volumes. They understood that attempting an attack against a hardened device would likely fail and potentially expose their tools to security researchers.
This built-in detection reveals that even the most advanced threat actors respect Apple's security features.
Who Should Enable Lockdown Mode?
Apple designed Lockdown Mode for users who face extraordinary digital threats. The feature provides maximum security at the cost of some convenience.
Consider enabling it if you:
- Work in journalism, activism, or human rights advocacy
- Handle sensitive government or corporate information
- Face potential targeting by nation-state actors
- Manage significant cryptocurrency holdings
- Have experienced previous sophisticated attacks
For most iPhone users, standard iOS security features provide adequate protection. Regular software updates, strong passwords, and two-factor authentication create a solid security foundation. However, Lockdown Mode remains available for anyone who wants extra protection.
What Data Does Coruna Target?
The exploit kit focuses heavily on financial theft. Once Coruna compromises a device, it deploys modules specifically designed to steal cryptocurrency and banking credentials. The payload can hook into 18 different cryptocurrency applications to exfiltrate wallet credentials.
Coruna includes sophisticated data analysis capabilities. It can decode QR codes from images stored on the device, a common method for storing cryptocurrency wallet information.
The malware analyzes text blobs searching for BIP39 word sequences, which represent cryptocurrency seed phrases.
The kit even scans Apple Notes for typical seed phrases and keywords. It searches for specific terms like "backup phrase," "bank account," and other financial indicators. This comprehensive approach to data theft demonstrates that the developers understood exactly what valuable information iPhone users store on their devices.
What Advanced Attack Techniques Does Coruna Use?
GTIG's analysis revealed that Coruna employs attack techniques never seen publicly before. These novel approaches suggest the developers had deep knowledge of iOS internals and security mechanisms. The exploit chain likely involves multiple stages, each bypassing different security layers.
The watering hole delivery method adds another layer of sophistication. Rather than sending phishing messages or requiring users to download malicious apps, attackers simply wait for targets to visit compromised websites.
This passive approach reduces detection risk and requires minimal victim interaction.
The custom packaging format represents significant development effort. Creating a proprietary exploit delivery system suggests the developers anticipated long-term use and wanted to maximize their investment. This level of engineering typically appears in state-sponsored tools rather than criminal malware.
How Can You Protect Your iPhone from Sophisticated Exploits?
Protecting your device from threats like Coruna requires a multi-layered approach. Start by keeping iOS updated to the latest version. Apple regularly patches vulnerabilities that exploit kits target, making updates your first line of defense.
Avoid clicking links from unknown sources or visiting suspicious websites. Watering hole attacks rely on users visiting compromised sites, so exercising caution with unfamiliar URLs helps prevent exposure.
Use Safari's built-in protections, which warn about potentially dangerous websites.
Consider where you store sensitive information. Cryptocurrency seed phrases and banking credentials should never exist solely on your phone. Use hardware wallets for cryptocurrency and enable all available security features on financial apps.
Two-factor authentication adds critical protection even if attackers compromise your device.
For high-risk users, enable Lockdown Mode through Settings > Privacy & Security > Lockdown Mode. The feature reduces iPhone functionality but provides maximum security against sophisticated attacks. You can disable it anytime if the restrictions prove too limiting.
What Does This Mean for iPhone Security?
The discovery of Coruna demonstrates that iPhone users face real, sophisticated threats. Nation-state actors and cybercriminals invest significant resources into developing iOS exploits. The underground market for these tools ensures they circulate widely, eventually reaching financially motivated criminals.
However, the fact that Lockdown Mode completely stops Coruna validates Apple's security approach. The company provides tools that work against even the most advanced threats.
This protection exists not just in theory but in practice, as demonstrated by Coruna's programmed retreat when it detects the feature.
The four-year span of iOS versions that Coruna targets highlights the importance of updates. Users running older iOS versions face significantly higher risk. Apple typically supports devices with security updates for five to six years, giving users ample opportunity to maintain protection.
How Does the Exploit Supply Chain Work?
The progression of Coruna through different threat actors reveals a troubling trend. Commercial surveillance vendors sell powerful tools that eventually leak into criminal hands. This "supply chain" for exploits means that capabilities developed for legitimate law enforcement can end up used for financial theft.
Zero-day exploits, which target previously unknown vulnerabilities, command high prices in underground markets. When surveillance vendors discover these vulnerabilities, they sometimes keep them secret to maintain their tools' effectiveness.
This practice leaves all users vulnerable until Apple discovers and patches the flaws independently.
The second-hand market for exploits suggests that even patched vulnerabilities retain value. Attackers know many users delay updates, creating opportunities to exploit older flaws. This reality underscores why prompt updates matter so much for security.
What Role Does Security Research Play?
GTIG's documentation of Coruna provides valuable intelligence for the security community. By publishing detailed analysis, Google helps other researchers understand current threats and develop better defenses. This collaborative approach strengthens overall cybersecurity.
The discovery also puts pressure on Apple to patch any remaining vulnerabilities that Coruna exploits. While the kit targets iOS versions through 17.2.1, current iOS versions likely close many of these attack vectors.
Apple's rapid response to disclosed vulnerabilities helps protect users.
Security researchers face challenges when analyzing tools like Coruna. The strong encryption and custom packaging require significant effort to reverse-engineer. Yet this work proves essential for understanding evolving threats and developing effective countermeasures.
Key Takeaways for iPhone Users
The Coruna exploit kit represents a serious threat, but iPhone users have effective defenses available. Apple's Lockdown Mode provides proven protection against even the most sophisticated attack frameworks. Regular updates close vulnerabilities before criminals can exploit them widely.
The underground market for iOS exploits will continue to exist. Nation-state actors, surveillance vendors, and cybercriminals invest heavily in developing these tools.
However, Apple's security features, when properly used, provide strong protection against these threats.
For most users, maintaining updated iOS versions and practicing basic security hygiene offers adequate protection. High-risk individuals should seriously consider enabling Lockdown Mode. The feature works exactly as designed, stopping advanced threats that would compromise unprotected devices.
Continue learning: Next, explore alibaba's qwen ai team exodus: what it means for business
The discovery of Coruna reminds us that mobile security requires ongoing attention. Threats evolve constantly, but so do defenses. By staying informed and using available security features, iPhone users can protect themselves against even the most sophisticated attacks.
Related Articles
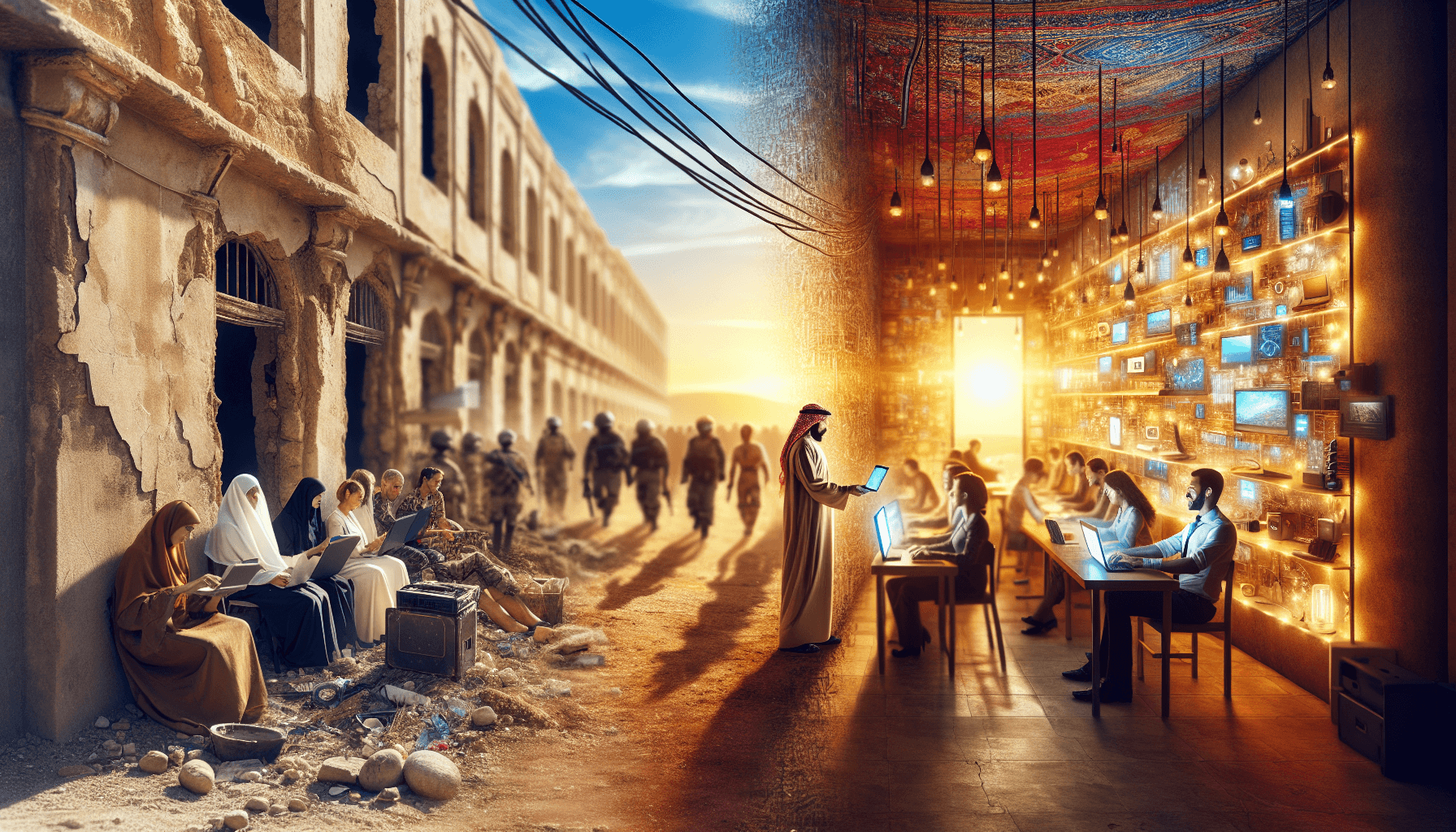
Transforming Gaza: From Conflict Zone to Tech Hub
A leaked plan from the Trump administration reveals a bold strategy to turn Gaza into a thriving high-tech hub. Discover the potential.
Sep 3, 2025
Gaza's Tech Revolution: Trump's Bold High-Tech Vision
A leaked plan from the Trump administration unveils a vision to make Gaza a high-tech hub, focusing on AI, cybersecurity, and digital innovation.
Sep 3, 2025
AI Tools Reveal Identities of ICE Officers Online
AI's emerging role in unmasking ICE officers spotlights the intersection of technology, privacy, and ethics, sparking a crucial societal debate.
Sep 2, 2025