- Home
- Technology
- DNSSEC Disruption Affecting .de Domains - Resolved
DNSSEC Disruption Affecting .de Domains - Resolved
The recent DNSSEC disruption affecting Germany's .de domains temporarily impacted millions of websites. Discover what caused the issue, how it was resolved, and key lessons for domain security.
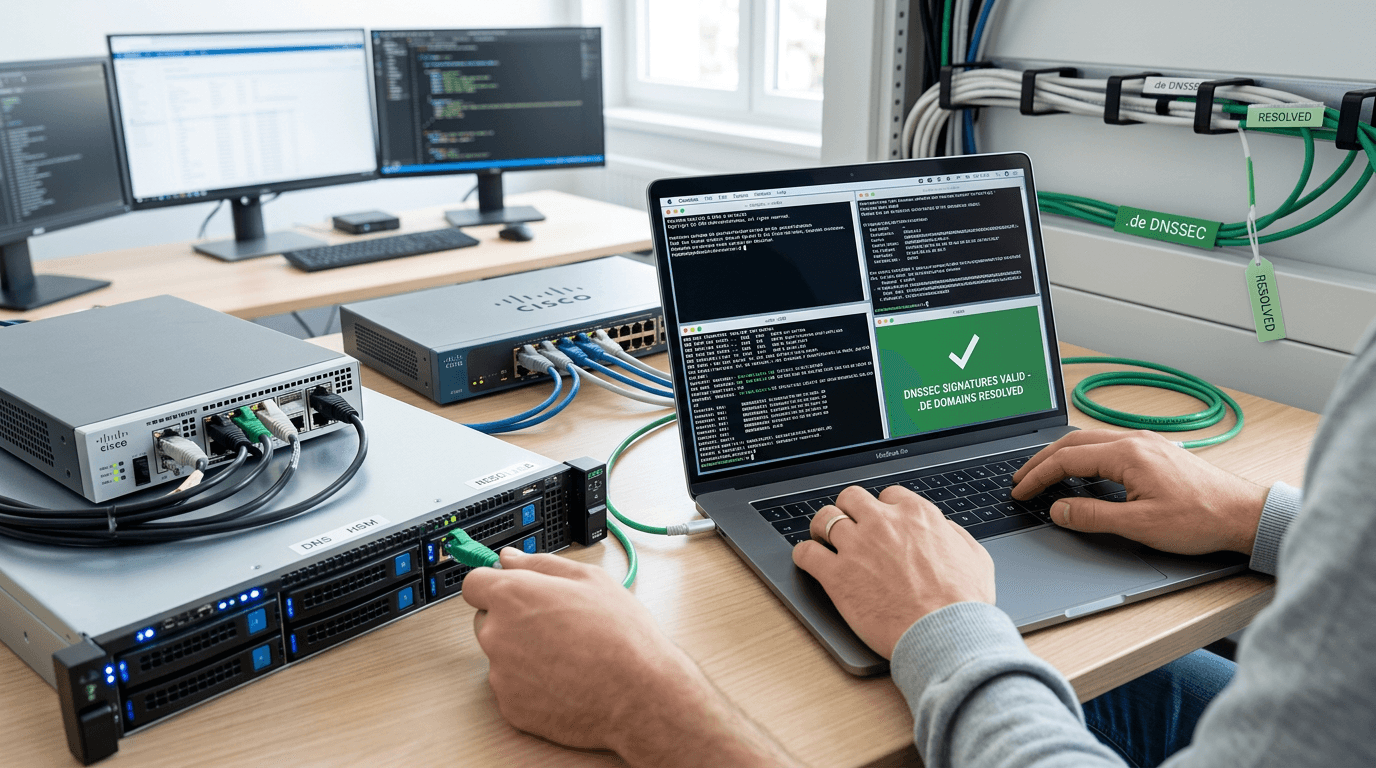
DNSSEC Disruption: What Happened to .de Domains and What It Means for Your Website
Learn more about fors fms turns game boy advance into fm groovebox for $10
Internet infrastructure failures rarely make headlines, but when they do, the impact ripples across millions of users worldwide. The recent DNSSEC disruption affecting .de domains serves as a stark reminder of how critical domain security protocols are to our digital ecosystem. This incident temporarily compromised access to German websites, affecting businesses, government services, and individual users who rely on .de domains daily.
What Caused the DNSSEC Disruption on .de Domains?
The Domain Name System Security Extensions (DNSSEC) disruption that hit .de domains created widespread connectivity issues across Germany's digital landscape. DENIC, the registry operator for .de domains, experienced a technical malfunction in their DNSSEC infrastructure that prevented proper domain name resolution.
This wasn't a cyberattack or malicious breach. Instead, a technical failure in the cryptographic signing process prevented the system from validating domain authenticity. When DNSSEC validation fails, recursive DNS resolvers configured to enforce strict security policies reject the responses, making affected websites appear offline to users.
Why Does DNSSEC Matter for Domain Security?
DNSSEC adds a layer of trust to the Domain Name System by digitally signing DNS data. It verifies you're connecting to the legitimate website, not an imposter created by cybercriminals.
The protocol works through a chain of trust, starting from the root DNS servers down to individual domains. Each level signs the records of the level below it, creating a verifiable path. When this chain breaks, as it did with .de domains, the entire security mechanism fails.
For the 17 million registered .de domains, this disruption meant potential inaccessibility for users whose DNS resolvers enforced DNSSEC validation. Germany's position as Europe's largest economy made this incident particularly significant for e-commerce, banking, and government services.
How Did the .de Domain DNSSEC Issue Unfold?
For a deep dive on apple pays $250m to settle siri delay class action, see our full guide
The disruption began when DENIC's automated DNSSEC signing systems encountered an error during the regular key rotation process. DNS zones require periodic updates to their cryptographic keys to maintain security.
During this routine maintenance, a configuration error caused the generation of invalid DNSSEC signatures. Recursive resolvers that checked these signatures found mismatches and refused to return the DNS records to users.
For a deep dive on expert sleepers ntx-8cv & forever eurorack modules review, see our full guide
What Was the Timeline of the DNSSEC Incident?
The issue manifested quickly but resolution took several hours:
- Initial Detection: Monitoring systems identified increased DNS query failures
- Investigation Phase: DENIC engineers traced the problem to DNSSEC signature validation errors
- Mitigation Efforts: Teams worked to regenerate valid signatures and propagate them globally
- Full Resolution: All .de domains returned to normal operation after signature propagation completed
The incident affected users differently based on their DNS resolver configuration. Users relying on public DNS services with strict DNSSEC validation experienced complete access failures. Those using resolvers with lenient validation or no DNSSEC checking remained largely unaffected.
How Did DENIC Resolve the Technical Issues?
DENIC's response demonstrated the importance of having robust incident response procedures for critical internet infrastructure. The registry immediately identified the root cause and implemented corrective measures.
The technical team regenerated the zone signing keys and key signing keys for the .de top-level domain. They then re-signed all DNS records with valid cryptographic signatures. This process required careful coordination to ensure the new signatures propagated through the global DNS hierarchy.
Why Did DNS Propagation Take Time?
DNS operates on a distributed caching system where resolvers store records temporarily to improve performance. The Time To Live (TTL) values determine how long resolvers cache information before requesting fresh data.
Even after DENIC fixed the signatures, users continued experiencing issues until their local resolvers refreshed their cached records. This propagation delay is normal but frustrating during incidents requiring immediate resolution.
DENIC worked with major DNS resolver operators to expedite cache clearing for .de domain records. This coordination helped reduce the overall impact duration significantly.
What Should Domain Owners Learn from This Incident?
This incident highlights several critical considerations for anyone managing domains or network infrastructure. Understanding these lessons helps prepare for similar situations and minimize their impact on your operations.
What Are the Key Takeaways for Domain Security?
- Monitor DNSSEC validation status: Implement monitoring tools that alert you to DNSSEC validation failures
- Maintain multiple DNS resolver options: Don't rely on a single DNS provider for your organization
- Test DNSSEC configurations regularly: Periodic testing catches configuration errors before they cause outages
- Document incident response procedures: Clear procedures accelerate resolution during critical incidents
- Communicate with users proactively: Transparency during outages builds trust and reduces support burden
Domain owners should verify their DNSSEC implementation with validation tools regularly. Services like DNSViz and Verisign's DNSSEC Analyzer provide detailed reports on your domain's security chain.
Should You Disable DNSSEC After This Disruption?
Some administrators considered disabling DNSSEC following this incident, but that's the wrong lesson to draw. DNSSEC remains crucial for preventing DNS spoofing and cache poisoning attacks.
The disruption resulted from a technical error, not a fundamental flaw in DNSSEC itself. Abandoning the protocol would expose domains to serious security vulnerabilities that cybercriminals actively exploit.
Focus on implementing DNSSEC correctly and maintaining proper operational procedures. Work with your domain registrar to ensure they have robust DNSSEC management systems and incident response capabilities.
How Does This Fit Into Broader DNS Security Concerns?
This incident occurred against a backdrop of increasing DNS-based attacks and infrastructure vulnerabilities. Cybercriminals regularly attempt to manipulate DNS records to redirect users to malicious websites or intercept sensitive communications.
DNSSEC adoption has grown steadily, with approximately 40% of top-level domains now implementing the protocol. However, adoption at the individual domain level remains lower, creating security gaps that attackers exploit.
Germany's .de domain represents one of the most DNSSEC-mature country-code TLDs. DENIC has championed DNS security for years, making this incident particularly noteworthy. Their quick resolution demonstrated the value of experienced operators managing critical infrastructure.
What Does the Future Hold for DNS Security Protocols?
The DNS community continues developing improvements to make security protocols more resilient and easier to implement. Initiatives like DNS over HTTPS (DoH) and DNS over TLS (DoT) add encryption to DNS queries, complementing DNSSEC's authentication capabilities.
These technologies work together to create a more secure internet infrastructure. DNSSEC verifies you're connecting to the correct server, while DoH and DoT encrypt your DNS queries to prevent eavesdropping.
Organizations should consider implementing comprehensive DNS security strategies that incorporate multiple protective layers. This defense-in-depth approach provides resilience even when individual components experience issues.
What Can We Learn from the .de DNSSEC Disruption?
The DNSSEC disruption affecting .de domains serves as an important case study in internet infrastructure management. DENIC's rapid response and transparent communication minimized the incident's overall impact and demonstrated best practices for handling critical infrastructure failures.
For domain owners and IT professionals, this event reinforces the importance of proper DNSSEC implementation, monitoring, and incident response planning. While the disruption caused temporary inconvenience, it doesn't diminish DNSSEC's value in protecting against DNS-based attacks.
Continue learning: Next, explore maintainer month: celebrating open source contributors
As our digital infrastructure grows increasingly complex, incidents like this will occasionally occur. The key lies in learning from them, improving our systems, and maintaining the security protocols that keep the internet trustworthy for billions of users worldwide.
Related Articles
Transforming Gaza: From Conflict Zone to Tech Hub
A leaked plan from the Trump administration reveals a bold strategy to turn Gaza into a thriving high-tech hub. Discover the potential.
Sep 3, 2025
AI Tools Reveal Identities of ICE Officers Online
AI's emerging role in unmasking ICE officers spotlights the intersection of technology, privacy, and ethics, sparking a crucial societal debate.
Sep 2, 2025
AI's Role in Unveiling ICE Officers' Identities
AI unmasking ICE officers underscores a shift towards transparent law enforcement, raising questions about privacy and ethics in the digital age.
Sep 2, 2025
