- Home
- Technology
- Dirtyfrag: Universal Linux LPE Exploit Explained
Dirtyfrag: Universal Linux LPE Exploit Explained
A new Linux privilege escalation vulnerability called Dirtyfrag has emerged, allowing attackers to gain root access. Discover what makes this exploit particularly dangerous.

What Is the Dirtyfrag Linux LPE Threat?
Learn more about google's video streaming strategy backfires: what went wrong
The cybersecurity landscape faces a new challenge with Dirtyfrag, a universal Linux Local Privilege Escalation (LPE) exploit that threatens systems worldwide. This vulnerability allows attackers with limited user access to elevate their privileges to root level, effectively taking complete control of affected machines.
Security researchers discovered this critical flaw in the Linux kernel's memory management subsystem, specifically targeting the page fragmentation mechanism. Dirtyfrag exploits a race condition in how Linux handles memory pages during fragmentation operations.
The vulnerability affects multiple kernel versions, making it a widespread concern for system administrators and security teams. Unlike previous Linux exploits that targeted specific distributions or configurations, Dirtyfrag works across different Linux flavors with minimal modification.
Why Is Dirtyfrag Called a Universal Exploit?
The term "universal" in Dirtyfrag's description refers to its broad applicability across Linux systems. Traditional privilege escalation exploits often require specific kernel versions, configurations, or hardware setups. Dirtyfrag breaks this pattern by leveraging fundamental kernel mechanisms present in most modern Linux distributions.
The exploit targets the kernel's page cache management system, which handles how memory pages are stored and retrieved. When the system fragments large memory pages into smaller ones, a brief window exists where memory permissions are not properly enforced. Attackers inject malicious code during this critical moment, bypassing security checks.
Several factors contribute to Dirtyfrag's universal nature:
- Cross-distribution compatibility: Works on Ubuntu, Debian, RHEL, CentOS, and other major distributions
- Kernel version range: Affects Linux kernels from version 5.8 through 6.2
- Architecture support: Functions on both x86_64 and ARM64 processors
- Minimal prerequisites: Requires only standard user-level access to execute
How Does the Dirtyfrag Exploit Work?
Dirtyfrag operates by manipulating the kernel's transparent huge pages (THP) feature, designed to improve system performance by using larger memory pages. The exploit creates a specific memory layout that triggers a race condition during page splitting operations.
When the kernel splits a huge page into smaller 4KB pages, it temporarily loses track of access permissions. The attacker initiates multiple threads that simultaneously request page fragmentation while attempting to write to protected kernel memory.
For a deep dive on saros review: cosmic horror meets roguelite shortcomings, see our full guide
One thread triggers the fragmentation process while another exploits the microsecond window where permissions are undefined. This timing attack allows unauthorized modification of kernel data structures. Once the attacker gains write access to kernel memory, they can modify the process credentials structure.
This structure contains user ID, group ID, and capability information that determines process privileges. By changing these values to zero (root's UID), the attacker's process gains full administrative rights.
For a deep dive on roland ai pedal lydia phase 2: guitar to trumpet in real ..., see our full guide
What Are the Technical Details Behind the Vulnerability?
The vulnerability stems from improper synchronization in the kernel's memory management code. Specifically, the split_huge_page() function fails to maintain consistent permission checks during the splitting operation.
The kernel assumes that permission validation at the start of the operation remains valid throughout execution. This assumption breaks when multiple CPU cores access the same memory region simultaneously.
Modern multi-core processors execute instructions out of order for performance optimization. The kernel's locking mechanisms do not account for this behavior during page fragmentation, creating the exploitable race condition.
The exploit code typically follows this sequence:
- Allocate a large memory region to trigger THP allocation
- Create multiple threads to increase race condition probability
- Trigger page fragmentation through specific memory access patterns
- Attempt kernel memory writes during the permission validation gap
- Modify process credentials to achieve privilege escalation
Who Faces Risk from Dirtyfrag?
Organizations running vulnerable Linux kernel versions face significant security risks. Cloud service providers, web hosting companies, and enterprises with Linux-based infrastructure are primary targets.
The exploit's universal nature means attackers develop a single payload that works across different environments. Multi-tenant environments face particular danger because a compromised user account can escalate to root access.
This breaks the isolation between different users or virtual machines sharing the same physical hardware. Attackers who gain initial access through phishing, weak passwords, or other vulnerabilities use Dirtyfrag as a second-stage exploit.
Container environments running vulnerable kernels also face risks. While containers provide application isolation, they share the host kernel. A compromised container can exploit Dirtyfrag to escape containment and access the host system, defeating the security benefits of containerization.
What Attack Scenarios Can Dirtyfrag Enable?
Attackers leverage Dirtyfrag in various ways depending on their objectives. A common scenario involves combining it with other vulnerabilities to achieve complete system compromise.
An attacker might first exploit a web application vulnerability to gain limited shell access, then use Dirtyfrag to escalate privileges. Cryptocurrency mining operations represent another likely attack vector.
Attackers seek root access to install mining software that consumes system resources. Dirtyfrag provides a reliable escalation path that works across different hosting environments. The universal nature makes it attractive for automated attack campaigns.
Advanced persistent threat (APT) groups may use Dirtyfrag for espionage or sabotage operations. Root access enables attackers to install rootkits, modify system logs, and establish persistent backdoors. The exploit's reliability makes it valuable for targeted attacks against high-value systems.
How Can You Protect Your Systems from Dirtyfrag?
Immediate patching represents the most effective defense against Dirtyfrag exploitation. Linux distribution maintainers have released security updates addressing the vulnerability.
System administrators should prioritize applying these patches across their infrastructure. The following distributions have released patches:
- Ubuntu: Security update in packages linux-image-5.15.0-76 and later
- Debian: Fixed in kernel version 6.1.37-1
- Red Hat Enterprise Linux: Addressed in RHSA-2023:3723
- SUSE Linux: Patched in kernel-default-5.14.21-150400.24.63.1
Organizations unable to immediately patch can implement temporary mitigations. Disabling transparent huge pages reduces the attack surface, though this impacts system performance. The command echo never > /sys/kernel/mm/transparent_hugepage/enabled disables THP system-wide.
How Can You Detect Dirtyfrag Exploitation Attempts?
Monitoring systems for suspicious activity helps identify exploitation attempts. Security teams should watch for unusual memory allocation patterns or processes attempting repeated page fragmentation operations.
Intrusion detection systems flag these behaviors as potential attack indicators. Audit logs provide valuable forensic information after suspected compromises.
Enabling comprehensive kernel auditing captures privilege escalation attempts. The auditd service on Linux systems tracks system calls related to memory management and credential modification.
Security information and event management (SIEM) systems should correlate multiple indicators of compromise. Look for patterns combining unusual memory operations with subsequent privilege changes. Behavioral analysis tools detect anomalies in normal system operation that might indicate exploitation.
What Are the Broader Implications for Linux Security?
Dirtyfrag highlights ongoing challenges in securing complex kernel code. The Linux kernel contains millions of lines of code managing intricate hardware interactions.
Race conditions in multi-threaded environments remain difficult to identify through code review alone. This vulnerability demonstrates that even well-audited code can contain subtle security flaws.
The discovery emphasizes the importance of defense-in-depth strategies. Organizations should not rely solely on kernel security but implement multiple protective layers.
Security mechanisms like SELinux, AppArmor, and seccomp provide additional barriers against privilege escalation. These technologies limit damage even if an attacker exploits a kernel vulnerability.
The cybersecurity community's response to Dirtyfrag showcases collaborative security research. Researchers who discovered the vulnerability worked with kernel developers to create patches before public disclosure. This responsible disclosure process gives organizations time to update systems before attackers develop widespread exploits.
What Does Dirtyfrag Mean for Future Linux Development?
Kernel developers are implementing additional safeguards against similar vulnerabilities. Enhanced memory management locking mechanisms aim to prevent race conditions during page operations.
Static analysis tools are being improved to detect potential timing vulnerabilities during code review. The incident may accelerate adoption of memory-safe programming languages in kernel development.
Rust integration into the Linux kernel offers stronger memory safety guarantees than traditional C code. While complete kernel rewrites remain impractical, critical subsystems may benefit from memory-safe implementations.
How Should You Respond to the Dirtyfrag Threat?
Dirtyfrag represents a significant threat to Linux systems worldwide, but proper security practices effectively mitigate the risk. Organizations must prioritize patching vulnerable systems while implementing comprehensive monitoring to detect exploitation attempts.
The vulnerability serves as a reminder that even mature, widely-used software requires constant security vigilance. System administrators should verify their kernel versions, apply available patches, and review their security monitoring capabilities.
Continue learning: Next, explore rhino teeth in neanderthal toolkits: a new discovery
Defense-in-depth strategies provide essential protection against both known and unknown vulnerabilities. As the Linux ecosystem continues evolving, maintaining robust security practices remains critical for protecting infrastructure against emerging threats like Dirtyfrag.
Related Articles
AI Tools Reveal Identities of ICE Officers Online
AI's emerging role in unmasking ICE officers spotlights the intersection of technology, privacy, and ethics, sparking a crucial societal debate.
Sep 2, 2025
AI's Role in Unveiling ICE Officers' Identities
AI unmasking ICE officers underscores a shift towards transparent law enforcement, raising questions about privacy and ethics in the digital age.
Sep 2, 2025
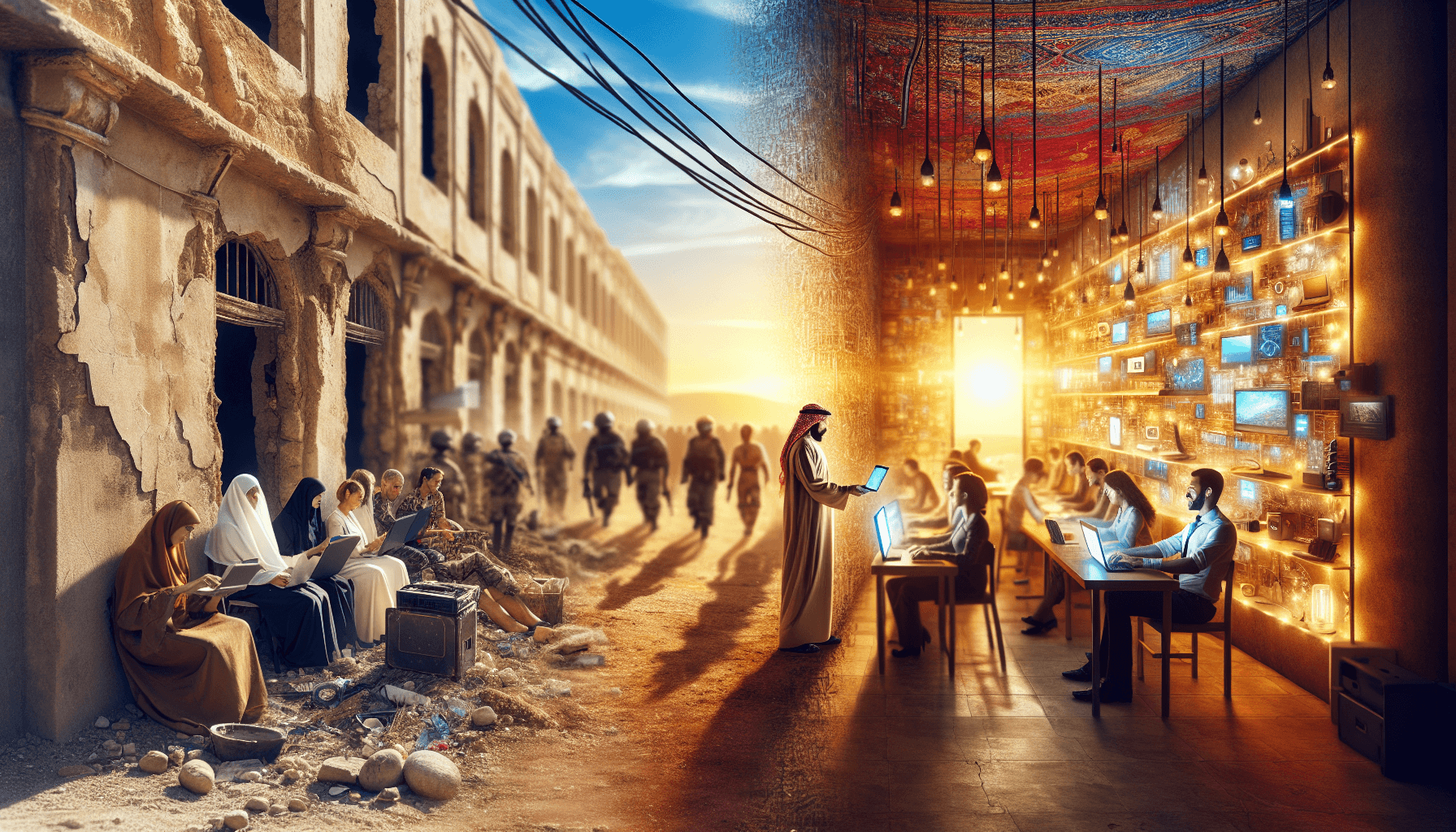
Transforming Gaza: From Conflict Zone to Tech Hub
A leaked plan from the Trump administration reveals a bold strategy to turn Gaza into a thriving high-tech hub. Discover the potential.
Sep 3, 2025
