- Home
- Technology
- What Being Ripped Off Taught Me About Tech Security
What Being Ripped Off Taught Me About Tech Security
Getting scammed by a sophisticated tech fraud cost me money but taught me priceless lessons about digital security, online fraud detection, and protecting personal data.

What Being Ripped Off Taught Me About Cybersecurity
Learn more about i won't download your app: the web version works fine
Losing $2,400 to a tech support scam changed how I view digital security forever. The experience was humiliating, expensive, and eye-opening. What being ripped off taught me goes beyond just recognizing fraudulent phone calls or suspicious emails.
It fundamentally reshaped my understanding of cybersecurity, personal data protection, and the sophisticated tactics criminals use to exploit technology users. Every painful lesson I learned can help you avoid similar mistakes.
How Did I Fall for a $2,400 Tech Support Scam?
The scam started with a convincing pop-up warning that my computer was infected with malware. The message displayed what appeared to be legitimate Microsoft branding, complete with a toll-free number. Within minutes of calling, I had granted remote access to someone who claimed to be a certified technician.
The scammer showed me fabricated system errors and convinced me to purchase a $2,400 "security package." They used technical jargon, created urgency, and exploited my limited knowledge about system diagnostics. By the time I realized something was wrong, they had already processed my payment through multiple channels.
Why Should You Verify Everything in Cybersecurity?
The first lesson hit hardest: legitimate tech companies never initiate contact through pop-ups or unsolicited calls. Microsoft, Apple, Google, and other major companies will never call you about computer problems they supposedly detected.
This principle extends to every digital interaction. I now verify sender email addresses character by character, checking for subtle misspellings like "micros0ft.com" instead of "microsoft.com." Phone numbers get researched through official company websites, not through caller ID or search results.
Two-factor authentication became non-negotiable across all my accounts. Even if someone steals my password, they cannot access my accounts without the secondary verification code.
For a deep dive on a single ai platform for every role in your business, see our full guide
How Do Scammers Make Their Schemes Look Legitimate?
Scammers invest heavily in appearing authentic. They purchase domains that closely resemble legitimate companies, create professional-looking websites, and use spoofing technology to display fake caller IDs. Some even establish physical call centers that sound like genuine customer support operations.
For a deep dive on ocsf explained: the security data language teams need, see our full guide
The psychological manipulation runs deeper than technology. Scammers create artificial time pressure, claiming your data is being stolen "right now" or your accounts will be locked "within hours." This urgency bypasses rational thinking and triggers panic responses.
They also exploit authority bias by using technical terminology and claiming certifications. My scammer referenced specific Windows error codes and registry entries, making their diagnosis seem credible despite being completely fabricated.
What Happens When You Grant Remote Access to Scammers?
Granting remote access to my computer was the critical mistake. Once connected, the scammer could install keyloggers, steal stored passwords, access financial information, and plant malware for future exploitation.
Remote access tools like TeamViewer, AnyDesk, or LogMeIn are legitimate software, but scammers abuse them. Never grant remote access unless you initiated the support request through official channels and verified the technician's identity independently.
After the incident, I performed a complete system wipe and reinstall. I changed every password using a password manager with randomly generated credentials. My bank accounts required new numbers, and I placed fraud alerts with all three credit bureaus.
How Can You Build a Personal Cybersecurity Framework?
My experience forced me to develop systematic security habits. I now maintain separate email addresses for different purposes: one for financial accounts, one for shopping, and one for social media. This compartmentalization limits damage if one account gets compromised.
Software updates happen immediately, not later. Cybercriminals exploit known vulnerabilities in outdated software, and those "remind me later" buttons create security gaps. Automatic updates now run on all my devices.
I implemented these essential security measures:
- Password manager with unique credentials for every account
- Hardware security keys for critical financial and email accounts
- Regular credit report monitoring through official channels
- Virtual credit card numbers for online purchases
- VPN usage on all public Wi-Fi networks
Why Do Smart People Fall for Tech Support Scams?
Understanding why I fell for the scam proved as valuable as learning prevention techniques. Scammers exploit cognitive biases that affect everyone, regardless of intelligence or technical knowledge. The availability heuristic made me believe the threat was real because I had recently read about malware attacks.
Confirmation bias played a role when the scammer "proved" the infection by showing me normal system processes with scary-sounding names. I wanted to believe the expert who offered a solution rather than question their legitimacy.
Embarrassment prevents many victims from reporting scams or warning others. I initially felt too ashamed to tell anyone, which allowed the criminals to continue operating. Sharing my story became part of the healing process and helps prevent others from similar experiences.
What Red Flags Should You Never Ignore?
Looking back, numerous warning signs screamed "scam" that I overlooked in my panicked state. The payment method should have triggered immediate suspicion. They insisted on gift cards and wire transfers rather than standard credit card processing.
Legitimate companies provide detailed invoices, official contracts, and established refund policies. My scammer offered none of these, instead pushing for immediate payment before "the hackers steal everything."
The communication patterns revealed another red flag. Professional support maintains ticket numbers, sends confirmation emails from official domains, and allows you to call back at your convenience. Scammers pressure you to stay on the line and resist any attempt to independently verify their claims.
How Can You Protect Your Family from Tech Scams?
My expensive lesson became a teaching opportunity for family and friends. I created a simple checklist they can reference when facing potential scams:
- Hang up on unsolicited tech support calls immediately
- Close pop-up warnings without clicking anything
- Contact companies directly using official website numbers
- Never grant remote access to unsolicited callers
- Refuse payment through gift cards or wire transfers
- Take time to research and verify before acting
Elderly relatives particularly benefited from these conversations. Statistics show people over 60 lose more money to tech support scams than any other age group, with median losses exceeding $1,500 per incident.
Can You Recover Money Lost to Tech Support Scams?
While I would prefer to have learned these lessons without losing money, the experience transformed my approach to digital security. I now view every online interaction through a security lens, questioning legitimacy before trusting appearances.
This heightened awareness extends beyond personal protection. In my professional life, I advocate for better cybersecurity training and implement stronger verification procedures. The scam made me a more cautious, informed technology user.
The financial loss stung, but the knowledge gained proved invaluable. I recovered the money through my bank's fraud protection after filing a police report and providing documentation. The process took months, but persistence paid off.
What Should You Do to Protect Yourself Today?
What being ripped off taught me centers on empowerment through knowledge. Cybercriminals rely on ignorance, fear, and trust to succeed. Understanding their tactics removes their power.
Every technology user faces potential threats, but awareness and preparation dramatically reduce risk. The lessons learned from my mistake cost money but provided education worth far more than the financial loss.
Your digital security depends on constant vigilance, healthy skepticism, and systematic protection measures. Learn from my expensive mistake and implement these safeguards before facing your own crisis. The best defense against tech scams combines technical security measures with psychological awareness of manipulation tactics.
Continue learning: Next, explore best amp for metal in 2026: ultimate budget buying guide
Stay suspicious, verify everything, and never let urgency override careful verification. These principles, learned through painful experience, now guide every digital interaction I make.
Related Articles
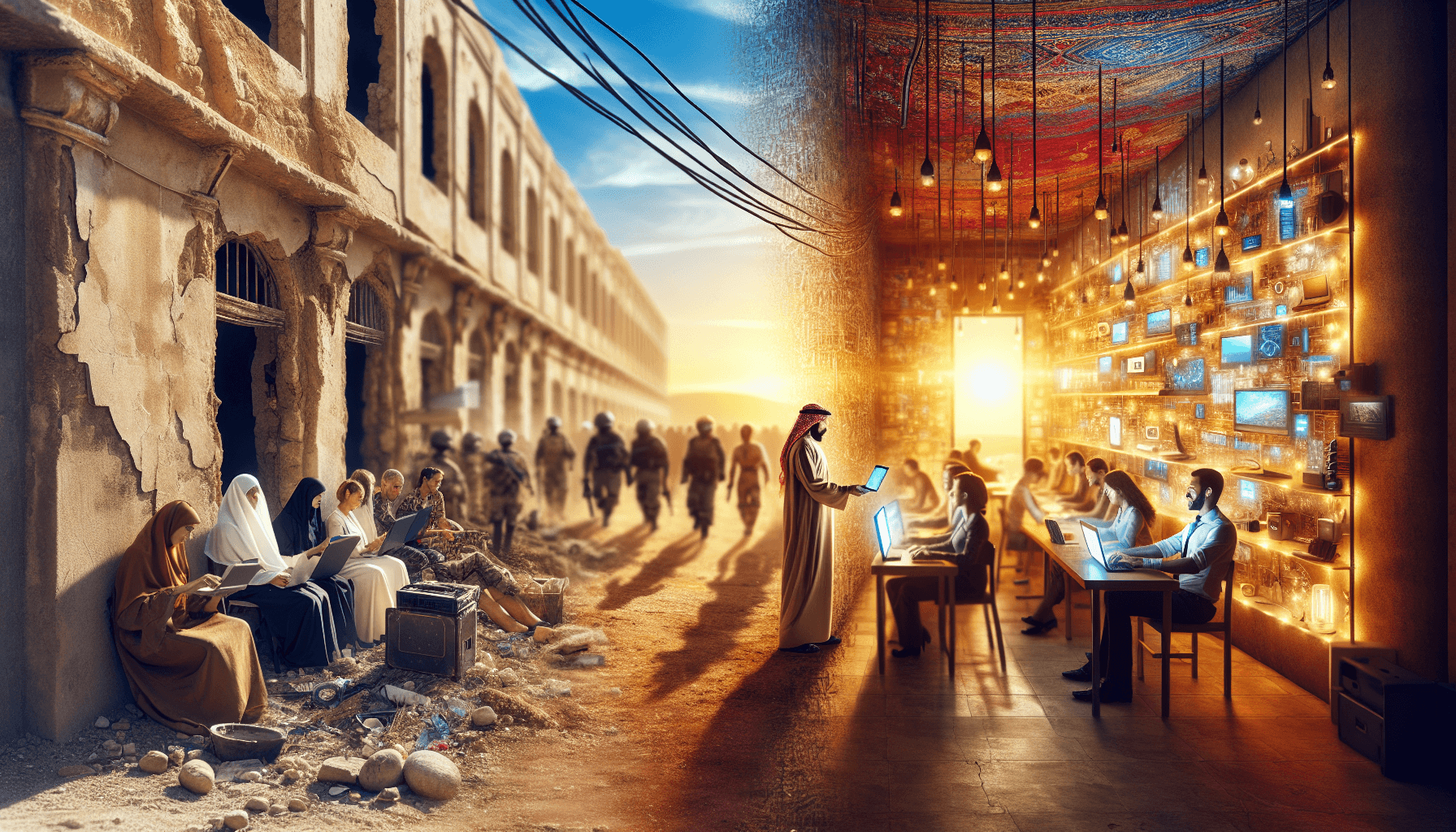
Transforming Gaza: From Conflict Zone to Tech Hub
A leaked plan from the Trump administration reveals a bold strategy to turn Gaza into a thriving high-tech hub. Discover the potential.
Sep 3, 2025
AI Tools Reveal Identities of ICE Officers Online
AI's emerging role in unmasking ICE officers spotlights the intersection of technology, privacy, and ethics, sparking a crucial societal debate.
Sep 2, 2025
AI's Role in Unveiling ICE Officers' Identities
AI unmasking ICE officers underscores a shift towards transparent law enforcement, raising questions about privacy and ethics in the digital age.
Sep 2, 2025