- Home
- Technology
- Quantum Computing Timelines: A Cryptography Engineer's View
Quantum Computing Timelines: A Cryptography Engineer's View
Quantum computers threaten current encryption methods. A cryptography engineer examines realistic timelines for quantum threats and what organizations must do now to prepare.
Understanding Quantum Computing Timelines from a Cryptography Engineer's Perspective
Learn more about what being ripped off taught me about tech security
Headlines scream about quantum computers breaking all encryption within years. As a cryptography engineer who monitors quantum developments daily, I see a more nuanced reality. The quantum threat is real, but the timeline requires careful analysis beyond sensational claims.
Quantum computing timelines directly impact how we design and implement cryptographic systems today. Organizations investing millions in security infrastructure need accurate forecasts, not hype. The gap between quantum computing capabilities and cryptographically relevant quantum computers (CRQCs) remains significant.
What Makes a Quantum Computer Cryptographically Relevant?
Not all quantum computers pose threats to encryption. A CRQC needs specific capabilities that current systems lack entirely. The machine must run Shor's algorithm efficiently enough to factor large numbers or solve discrete logarithm problems faster than classical computers.
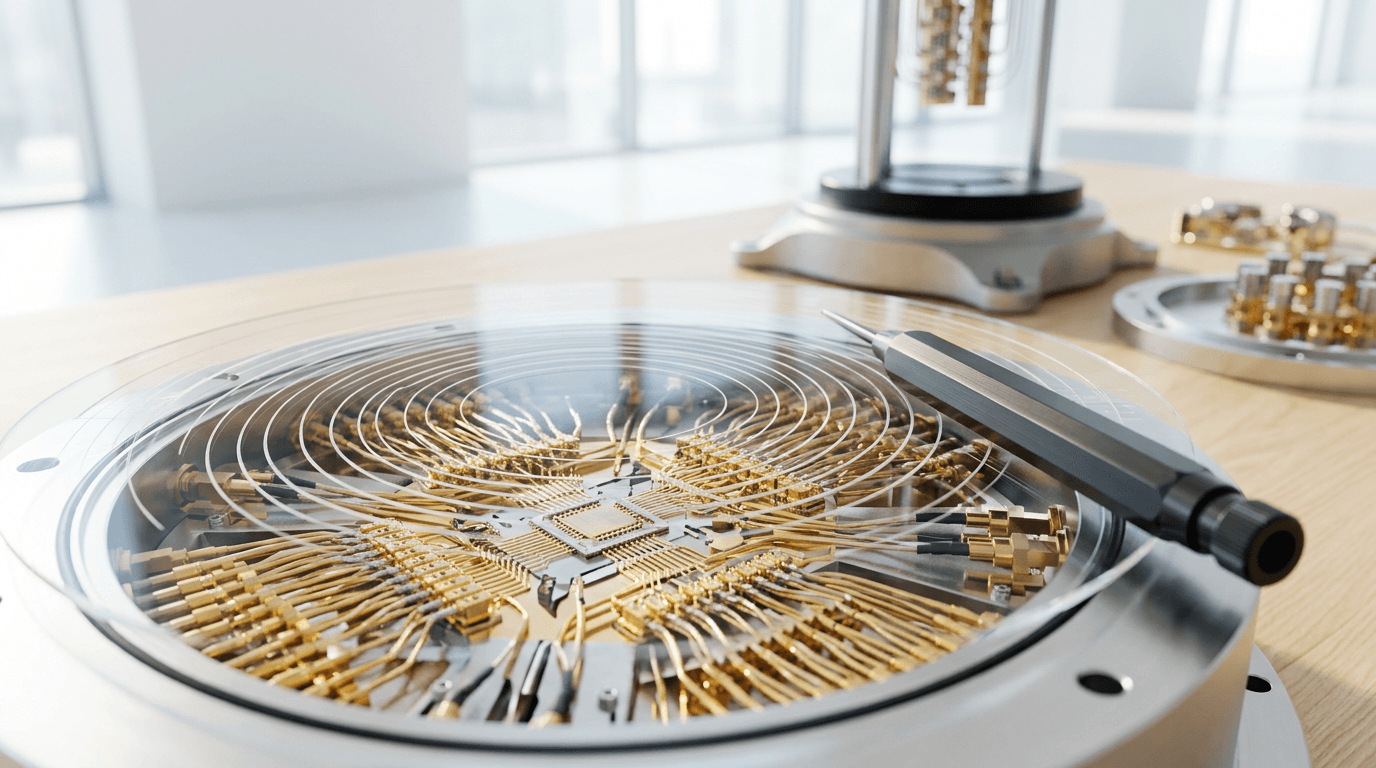
Current quantum computers have fewer than 1,000 stable qubits. Breaking RSA-2048 encryption requires approximately 20 million qubits with extremely low error rates. This represents a gap of four orders of magnitude in qubit count alone.
Error correction adds another layer of complexity. Physical qubits must create logical qubits stable enough for extended calculations. Current error rates sit around 0.1% to 1%, but cryptographic attacks need rates below 0.001%. Each logical qubit might require 1,000 physical qubits for adequate error correction.
How Long Until Quantum Computers Break Current Encryption?
Most cryptography engineers plan around a 15-20 year timeline for CRQCs. This estimate comes from analyzing current progress rates and fundamental physics challenges. IBM's quantum roadmap targets 100,000 qubits by 2033, still far short of cryptographic relevance.
The National Institute of Standards and Technology (NIST) uses similar assumptions. Their post-quantum cryptography standardization process assumes adversaries might "store now, decrypt later." This threat model acknowledges that encrypted data captured today could be vulnerable in 15-20 years.
Several factors support this conservative timeline. Qubit coherence times must improve by 100-1000x. Error correction overhead remains computationally expensive. Scaling quantum systems introduces new engineering challenges. Manufacturing consistency across millions of qubits presents unsolved problems.
For a deep dive on i won't download your app: the web version works fine, see our full guide
Could Quantum Breakthroughs Accelerate the Timeline?
Some researchers believe breakthroughs could accelerate timelines to 10-15 years. Recent advances in topological qubits and error correction codes show promise. Companies like Google and IonQ report steady improvements in quantum volume and circuit depth.
For a deep dive on a single ai platform for every role in your business, see our full guide
The optimistic view assumes several technological leaps converge simultaneously. New qubit architectures might offer inherently lower error rates. Algorithmic improvements could reduce qubit requirements for Shor's algorithm.
However, this scenario requires everything going right. As an engineer, I plan for optimistic scenarios while expecting realistic ones. The difference between 10 and 20 years matters enormously for migration planning.
Why Does "Store Now, Decrypt Later" Change Everything?
The most immediate quantum threat is not breaking current communications. Adversaries can capture encrypted data today and store it indefinitely. When CRQCs arrive, they decrypt historical data that seemed secure when transmitted.
This threat affects different data types unequally. Medical records, state secrets, and financial data retain value for decades. Chat messages and news articles lose relevance quickly.
The harvest now, decrypt later attack means we need quantum-resistant encryption deployed years before CRQCs arrive. A 15-year CRQC timeline requires migration starting now for sensitive long-term data. This urgency drives current post-quantum cryptography adoption efforts.
Preparing for the Quantum Transition
How Do Post-Quantum Algorithms Compare to Current Encryption?
NIST finalized its first post-quantum cryptography standards in 2024. These algorithms resist both classical and quantum attacks using mathematical problems quantum computers cannot solve efficiently. The standardized algorithms include CRYSTALS-Kyber for encryption and CRYSTALS-Dilithium for digital signatures.
Post-quantum algorithms introduce trade-offs compared to current systems. Key sizes increase significantly, from 2,048 bits for RSA to 1,568 bytes for Kyber-768. Signature sizes also grow, impacting network bandwidth and storage. Computational performance often matches or exceeds classical algorithms.
Implementation requires careful engineering. Side-channel attacks, random number generation, and constant-time operations remain critical. The algorithms are new, meaning fewer cryptographers have audited implementations thoroughly.
What Should Organizations Do Today About Quantum Threats?
Cryptographic agility becomes essential in a quantum-uncertain world. Systems must support algorithm updates without complete redesigns. This flexibility allows organizations to adapt as quantum threats evolve and new algorithms emerge.
Organizations should take these practical steps now:
- Inventory cryptographic systems and data sensitivity levels
- Identify systems protecting long-term sensitive data
- Test post-quantum algorithm implementations in non-production environments
- Develop migration roadmaps with realistic timelines
- Train security teams on post-quantum cryptography principles
Hybrid approaches offer interim protection. Systems can use both classical and post-quantum algorithms simultaneously. Data remains secure if either algorithm resists attacks.
Can Quantum Key Distribution Protect Against Quantum Computers?
Quantum key distribution (QKD) uses quantum mechanics to detect eavesdropping on key exchanges. Some vendors promote QKD as the ultimate quantum-safe solution. QKD has significant limitations that prevent widespread adoption.
QKD requires dedicated fiber optic connections or line-of-sight free-space links. This constraint makes it impractical for internet-scale deployment. Distance limitations, equipment costs, and authentication requirements add further challenges.
As a cryptography engineer, I view QKD as a niche solution for specific high-security applications. Post-quantum cryptography offers more practical protection for most use cases. The NIST standards provide quantum resistance without QKD's infrastructure requirements.
The Broader Implications for Security
How Will Quantum Computing Affect Blockchain and Cryptocurrency?
Blockchain systems face unique quantum vulnerabilities. Bitcoin and Ethereum use elliptic curve cryptography for signatures and addresses. Quantum computers could forge signatures or derive private keys from public keys exposed in transactions.
The timeline for blockchain quantum threats matches general cryptographic timelines. However, blockchain's decentralized nature complicates upgrades. Consensus mechanisms must coordinate algorithm changes across thousands of nodes.
Reused addresses present the highest risk. When users spend from an address, they expose their public key. Quantum attackers could potentially derive the private key before the transaction confirms. Best practices already recommend using each address once, which provides some quantum resistance.
What Happens to Symmetric Encryption Like AES?
Grover's algorithm threatens symmetric encryption differently than Shor's algorithm threatens asymmetric systems. Grover's algorithm provides quadratic speedup for searching unstructured databases. This effectively halves symmetric key security levels.
AES-128 provides only 64-bit quantum security under Grover's algorithm. However, AES-256 still offers 128-bit quantum security, sufficient for most applications. Simply doubling key lengths maintains adequate security against quantum attacks.
Hash functions face similar considerations. SHA-256 provides 128-bit quantum collision resistance. SHA-384 and SHA-512 offer even stronger quantum security.
How Do We Separate Quantum Hype from Reality?
Quantum computing developments require balanced assessment. Each announcement of "quantum supremacy" or new qubit records gets scrutinized against cryptographic relevance. Most achievements, while scientifically impressive, remain far from threatening encryption.
The quantum computing industry has incentives to emphasize near-term capabilities. Investors want returns, governments want strategic advantages, and researchers want funding. These pressures can inflate timeline predictions in both directions.
Cryptography engineers focus on measurable metrics: qubit counts, error rates, coherence times, and gate fidelities. These technical specifications determine actual cryptographic risk far better than press releases. Conservative planning based on physics and engineering realities serves organizations better than reactive panic.
Conclusion: Taking Action on Quantum Cryptography Threats
Quantum computing timelines for cryptographic threats likely span 15-20 years, with optimistic scenarios reaching 10-15 years. This window demands action now, particularly for organizations protecting long-term sensitive data. The "store now, decrypt later" threat makes current encryption choices critical for future security.
Post-quantum cryptography standards provide practical protection without waiting for quantum key distribution infrastructure. Organizations should begin inventorying cryptographic systems, testing post-quantum algorithms, and developing migration roadmaps. Cryptographic agility ensures systems can adapt as quantum capabilities evolve.
Continue learning: Next, explore ocsf explained: the security data language teams need
The quantum threat is real but manageable with proper planning. By understanding realistic timelines and taking measured steps today, organizations can protect their data through the quantum transition and beyond.
Related Articles
Transforming Gaza: From Conflict Zone to Tech Hub
A leaked plan from the Trump administration reveals a bold strategy to turn Gaza into a thriving high-tech hub. Discover the potential.
Sep 3, 2025
Gaza's Tech Revolution: Trump's Bold High-Tech Vision
A leaked plan from the Trump administration unveils a vision to make Gaza a high-tech hub, focusing on AI, cybersecurity, and digital innovation.
Sep 3, 2025
AI Tools Reveal Identities of ICE Officers Online
AI's emerging role in unmasking ICE officers spotlights the intersection of technology, privacy, and ethics, sparking a crucial societal debate.
Sep 2, 2025