- Home
- Technology
- The Age Verification Trap: Data Protection Risks Ahead
The Age Verification Trap: Data Protection Risks Ahead
Discover the paradox of age verification: designed for safety, yet it compromises everyone's data protection. Learn the risks and solutions in this comprehensive guide.
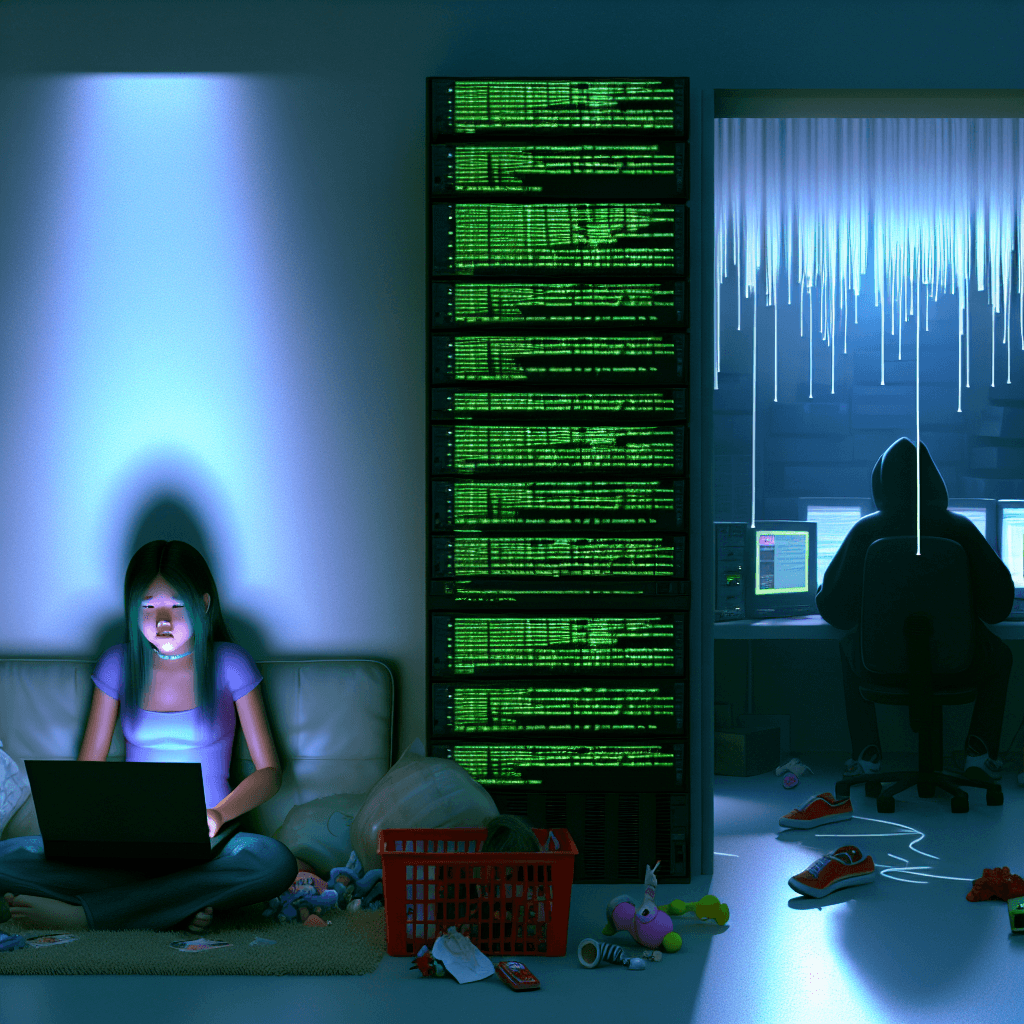
The Age Verification Trap: How Does Verifying Age Undermine Data Protection?
Learn more about binance employees uncover $1.7 billion crypto flow to iran
In today's digital landscape, privacy is crucial. However, age verification processes raise significant concerns. While these systems aim to protect minors from harmful content, they often compromise the data security of all users. This paradox highlights the age verification trap, where methods intended to verify age can lead to serious data protection risks.
Why Is Age Verification Necessary?
Age verification serves several essential functions:
- It protects minors from inappropriate content.
- It ensures compliance with legal regulations, such as the Children’s Online Privacy Protection Act (COPPA).
- It helps maintain a safe online environment for all users.
Despite these benefits, the systems designed to protect individuals can create vulnerabilities. Collecting sensitive personal information for age verification increases the risk of data breaches and misuse.
How Does Age Verification Compromise Data Protection?
Age verification typically requires users to submit personal information, including:
- Full name
- Date of birth
- Government-issued identification
📚 For a deep dive on beneath the atlantic: the hidden 500 km canyon revealed, see our full guide
If mishandled, this information can lead to various data protection issues:
- Increased Risk of Data Breaches: Centralizing sensitive data makes platforms attractive targets for cybercriminals.
- Potential for Identity Theft: If verification systems fail, personal data can be exploited.
- Invasive Data Collection Practices: Users often provide more information than necessary, raising privacy concerns.
- Lack of Transparency: Many age verification systems do not disclose how data will be used, creating trust issues.
- False Sense of Security: Age verification does not guarantee that minors will be prevented from accessing inappropriate content.
What Technologies Are Used for Age Verification?
Various technologies are employed for age verification, each with its advantages and disadvantages. Common methods include:
- Document Verification: Users upload ID documents. While accurate, this method carries the risk of data breaches.
- Biometric Verification: Systems analyze facial recognition or fingerprints. This enhances security but raises privacy concerns.
- Third-Party Age Verification Services: Platforms outsource age verification to specialized companies, which can reduce liability but may not ensure data protection.
Are There Safer Alternatives to Traditional Age Verification?
Innovative solutions are emerging to address the age verification trap without compromising data protection. Alternatives include:
- Decentralized Identity Solutions: These allow users to verify their age without sharing personal data with third parties.
- Blockchain Technology: By using blockchain, platforms can verify age while keeping user data encrypted and secure.
- User-Managed Credentials: Users can control their data and share only what is necessary for verification.
What Are the Legal Implications of Age Verification?
Regulations surrounding age verification are evolving, with many jurisdictions demanding stricter compliance. Key points to consider include:
- GDPR Compliance: The European Union's General Data Protection Regulation requires that any data collection method prioritize user privacy.
- COPPA Guidelines: In the U.S., platforms must ensure they do not collect data from children under 13 without parental consent.
- Increased Scrutiny: Governments are closely monitoring how companies handle user data, especially in age verification contexts.
How Can Users Protect Their Data During Age Verification?
Users can take proactive steps to safeguard their personal information when facing age verification requirements:
- Use Virtual Private Networks (VPNs): VPNs can mask users' identities and protect data during online interactions.
- Limit Information Sharing: Only provide the minimum required information for age verification.
- Read Privacy Policies: Understand how personal data will be used and stored before engaging with platforms.
Frequently Asked Questions
1. What is age verification?
Age verification is a process used to confirm a user's age to prevent access to age-restricted content.
2. Why is age verification a data protection risk?
It often involves collecting sensitive personal data, increasing the risk of data breaches and misuse.
3. What are the alternatives to traditional age verification?
Decentralized identity solutions and blockchain technology are emerging as safer alternatives.
4. How can I protect my data when verifying age online?
Consider using VPNs, limiting the information shared, and reviewing privacy policies.
5. Are there legal implications for failing to verify age properly?
Yes, companies could face legal actions if they do not comply with regulations like COPPA and GDPR.
Conclusion
The age verification trap presents a complex dilemma in the digital age. While safeguarding minors is crucial, the methods employed often compromise everyone's data protection. By adopting innovative technologies and prioritizing user privacy, we can mitigate these risks. As the conversation around age verification continues, both users and platforms must remain vigilant in protecting personal data.
Understanding the implications of age verification helps inform better practices that enhance safety without sacrificing privacy. As technology evolves, so too must our approaches to age verification, ensuring they align with modern data protection standards.
Continue Learning
Continue learning: Next, explore ladybird browser embraces rust for enhanced performance
Next, explore how the Ladybird browser embraces Rust for enhanced performance
Related Articles
Transforming Gaza: From Conflict Zone to Tech Hub
A leaked plan from the Trump administration reveals a bold strategy to turn Gaza into a thriving high-tech hub. Discover the potential.
Sep 3, 2025
AI Tools Reveal Identities of ICE Officers Online
AI's emerging role in unmasking ICE officers spotlights the intersection of technology, privacy, and ethics, sparking a crucial societal debate.
Sep 2, 2025
Gaza's Tech Revolution: Trump's Bold High-Tech Vision
A leaked plan from the Trump administration unveils a vision to make Gaza a high-tech hub, focusing on AI, cybersecurity, and digital innovation.
Sep 3, 2025