iPhone Exploit Kit Leak: Business Security Implications
A leaked iPhone exploit kit threatens millions of business devices worldwide. Discover what executives must do now to protect corporate data and maintain security compliance.

iPhone Exploit Kit Leak Exposes Millions to Security Threats
Learn more about reddit ceo plans to hire recent grads over ai cuts
A sophisticated exploit kit capable of compromising millions of iPhones has been publicly leaked, creating an unprecedented security crisis for businesses worldwide. The leaked DarkSword exploit toolkit provides attackers with ready-made code to penetrate iOS devices, transforming what was once a closely guarded hacking tool into a widely available weapon. For organizations relying on iPhones for business operations, this leak represents a critical turning point in mobile security strategy.
The timing couldn't be worse. Apple has issued urgent warnings to iPhone users following mass hacking campaigns that exploited vulnerabilities before patches became available. Companies now face a race against time to update their device fleets while managing the operational disruption that comes with emergency security protocols.
What Makes This iPhone Exploit Kit So Dangerous?
The leaked exploit kit differs fundamentally from typical security threats. Rather than targeting a single vulnerability, this toolkit provides a comprehensive framework for penetrating iOS security layers. Researchers have confirmed the spyware's capability to infiltrate millions of devices without requiring sophisticated technical knowledge from attackers.
The business implications extend beyond immediate data breaches. This leak democratizes advanced hacking capabilities, placing them in the hands of cybercriminals who previously lacked the resources or expertise to develop such tools. Small and medium-sized enterprises face particular risk, as they often lack the robust security infrastructure of larger corporations.
How Does the DarkSword Exploit Operate?
The DarkSword exploit chain leverages multiple iOS vulnerabilities simultaneously. Security researchers analyzing the leaked code discovered it targets core iOS functions that manage memory allocation and process permissions. By exploiting these fundamental systems, attackers gain unprecedented access to device data, communications, and credentials.
Key attack vectors include:
For a deep dive on hollywood teams don't stick together to learn from failure, see our full guide
- Zero-click exploits that require no user interaction to compromise devices
- Persistence mechanisms allowing continued access even after device restarts
- Data exfiltration tools designed to silently extract sensitive business information
- Communication interception capabilities targeting encrypted messaging apps
- Credential harvesting modules that capture authentication tokens and passwords
What Is the Business Impact Beyond Individual Device Security?
For a deep dive on stick to your business plan: avoid growth-driven mistakes, see our full guide
The exploit kit leak creates cascading risks throughout organizational ecosystems. When an executive's iPhone becomes compromised, attackers potentially gain access to corporate email, cloud storage, internal communications, and authentication systems. The average business iPhone contains access credentials to dozens of critical systems.
Financial services firms face particularly acute risks. Mobile banking apps, investment platforms, and payment systems all become vulnerable when the underlying device security fails. A single compromised device in a trading desk or accounting department could expose sensitive financial data or enable fraudulent transactions.
How Does This Affect Supply Chain Security?
Beyond direct device compromise, the leak affects business relationships and vendor trust. Companies that rely on iPhone security as part of their compliance framework must now reassess their entire security posture. Client data protection agreements, regulatory compliance requirements, and cyber insurance policies all hinge on maintaining robust mobile security.
Manufacturers and retailers using iPhones for inventory management, point-of-sale systems, or supply chain coordination face operational disruption. The exploit could enable competitors or malicious actors to access proprietary business intelligence, pricing strategies, or supplier relationships.
What Must Business Leaders Do Immediately?
Executive action determines whether organizations emerge from this crisis with minimal damage or suffer significant breaches. The window for preventive action narrows daily as more attackers gain access to the leaked toolkit and develop customized attack campaigns.
What Is the Immediate Response Protocol?
IT departments should implement emergency update procedures across all corporate iOS devices. Apple has released patches addressing the exploited vulnerabilities, but deployment requires coordinated effort. Organizations should:
- Audit all iOS devices connected to corporate networks or accessing business data
- Force immediate updates to the latest iOS version through mobile device management systems
- Implement network segmentation to limit potential breach spread from compromised devices
- Enable advanced threat detection on email gateways and network perimeters
- Review access permissions for business-critical systems accessible via mobile devices
Companies should assume some devices in their fleet may already be compromised. Forensic analysis of high-value targets like executive devices, finance team phones, and R&D department iPhones should begin immediately.
What Long-term Security Architecture Changes Are Needed?
This incident demands fundamental rethinking of mobile security strategies. The traditional perimeter-based security model fails when the devices themselves become attack vectors. Organizations must adopt zero-trust architectures that verify every access attempt regardless of device or network location.
Business continuity plans require updates to address scenarios where mobile device compromise leads to broader network breaches. Incident response teams need training specific to mobile-originated attacks and the unique forensic challenges they present.
What Are the Market and Industry Implications?
The exploit leak reshapes competitive dynamics in enterprise mobility. Companies heavily invested in iOS-based workflows face strategic questions about platform diversification. While no platform offers perfect security, concentrating all mobile operations on a single ecosystem creates systemic risk.
Cybersecurity vendors are experiencing surge demand for mobile threat detection and response capabilities. The market for mobile security solutions is projected to accelerate as organizations seek protection beyond manufacturer-provided security features. This creates opportunities for security-focused startups and established players with mobile expertise.
What About Insurance and Liability Considerations?
Cyber insurance policies face stress testing as claims related to mobile device breaches increase. Insurers are scrutinizing policy language around mobile security requirements and may impose stricter device management standards as coverage conditions. Businesses should review their policies to understand coverage limitations for mobile-originated breaches.
Legal liability questions emerge when compromised business phones expose client data or enable fraud. Organizations must document their response efforts and demonstrate reasonable security measures to defend against negligence claims.
Why Does This Leak Change the Security Landscape?
Public availability of sophisticated exploit code fundamentally alters the threat environment. Previously, such tools remained confined to nation-state actors and well-funded criminal organizations. The leak eliminates barriers to entry for less sophisticated attackers while enabling existing threat actors to scale their operations.
The business world must adapt to a reality where mobile devices face persistent, advanced threats. Security budgets require reallocation toward mobile-specific protections. Staff training programs need updates to address mobile security awareness. Vendor selection criteria should include mobile security capabilities as primary evaluation factors.
What Does This Mean for Technology Trust?
This incident raises uncomfortable questions about technology dependency in business operations. Organizations have embraced mobile-first strategies based on assumptions about platform security. When those assumptions prove flawed, entire business models face scrutiny.
The leak also highlights tensions between security through obscurity and transparent vulnerability disclosure. While Apple works to patch vulnerabilities, the public nature of this leak removes any remaining security through obscurity and forces rapid, comprehensive response.
How Should Organizations Navigate the New Mobile Security Reality?
The iPhone exploit kit leak represents a watershed moment for business technology security. Organizations can no longer treat mobile devices as trusted endpoints requiring minimal security oversight. The combination of sophisticated attack tools, public availability, and widespread iPhone adoption creates perfect conditions for sustained attack campaigns.
Business leaders must act decisively to update devices, strengthen security architectures, and reassess mobile security strategies. The companies that respond quickly and comprehensively will minimize their exposure. Those that delay or treat this as a routine security update face significant breach risks.
Continue learning: Next, explore apple announces swift student challenge winners march 26
Security is not a one-time achievement but an ongoing process requiring constant vigilance, rapid adaptation, and strategic investment. In an era where mobile devices serve as keys to corporate kingdoms, protecting those keys becomes a core business imperative rather than an IT afterthought.
Related Articles

Acer's New Chromebook: A Game-Changer for Businesses?
Acer's Chromebook Plus Spin 514 combines AI and potent computing, offering businesses a glimpse into the future of work.
Sep 5, 2025

Sony's Paywall Strategy: Xperia Feature Sparks Debate
Sony's recent strategy to lock a key Xperia feature behind a subscription has sparked a debate on innovation versus monetization.
Sep 4, 2025
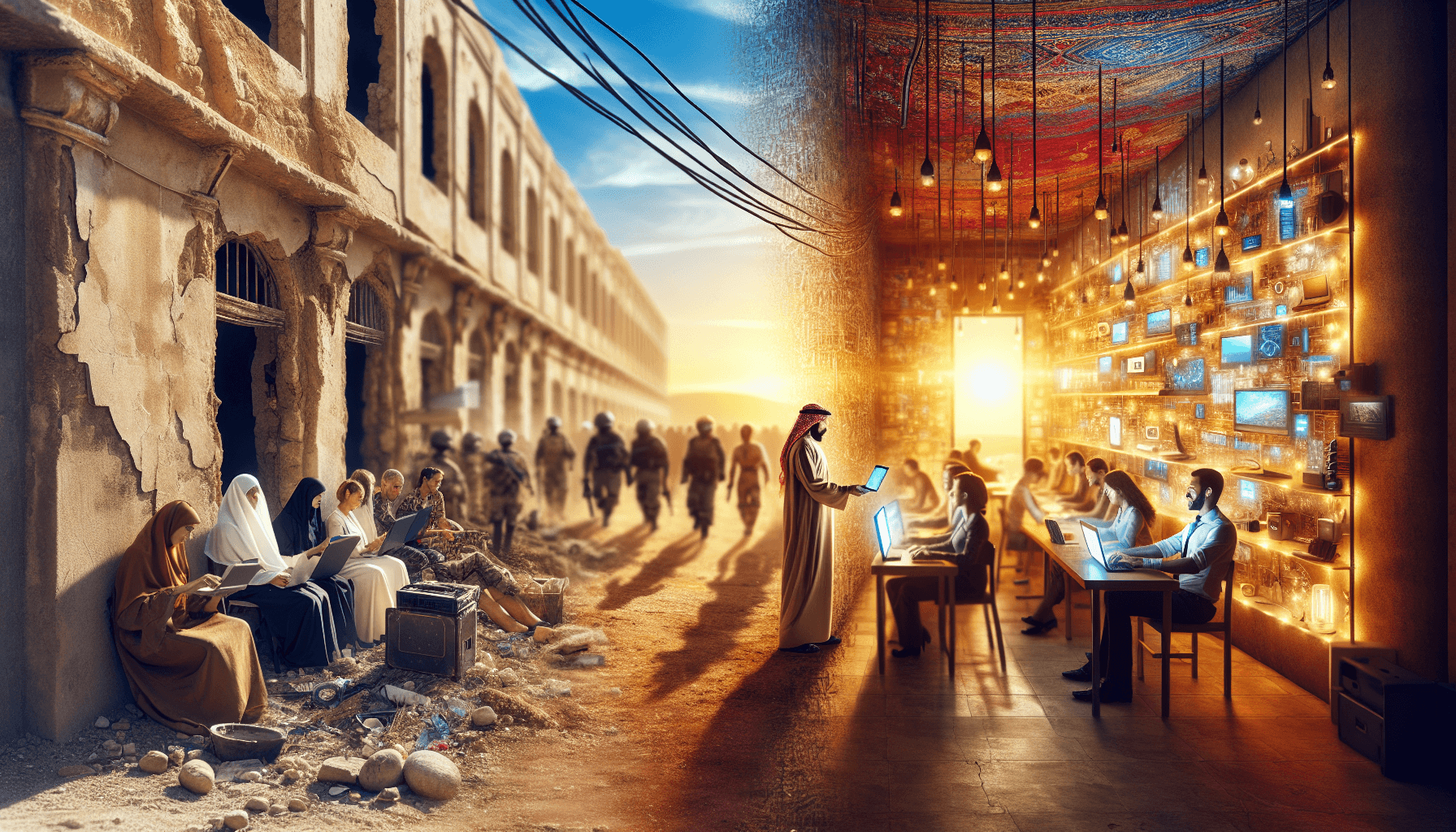
Transforming Gaza: From Conflict Zone to Tech Hub
A leaked plan from the Trump administration reveals a bold strategy to turn Gaza into a thriving high-tech hub. Discover the potential.
Sep 3, 2025
