- Home
- Technology
- How Kernel Anti-Cheats Work: Deep Dive Into Gaming Security
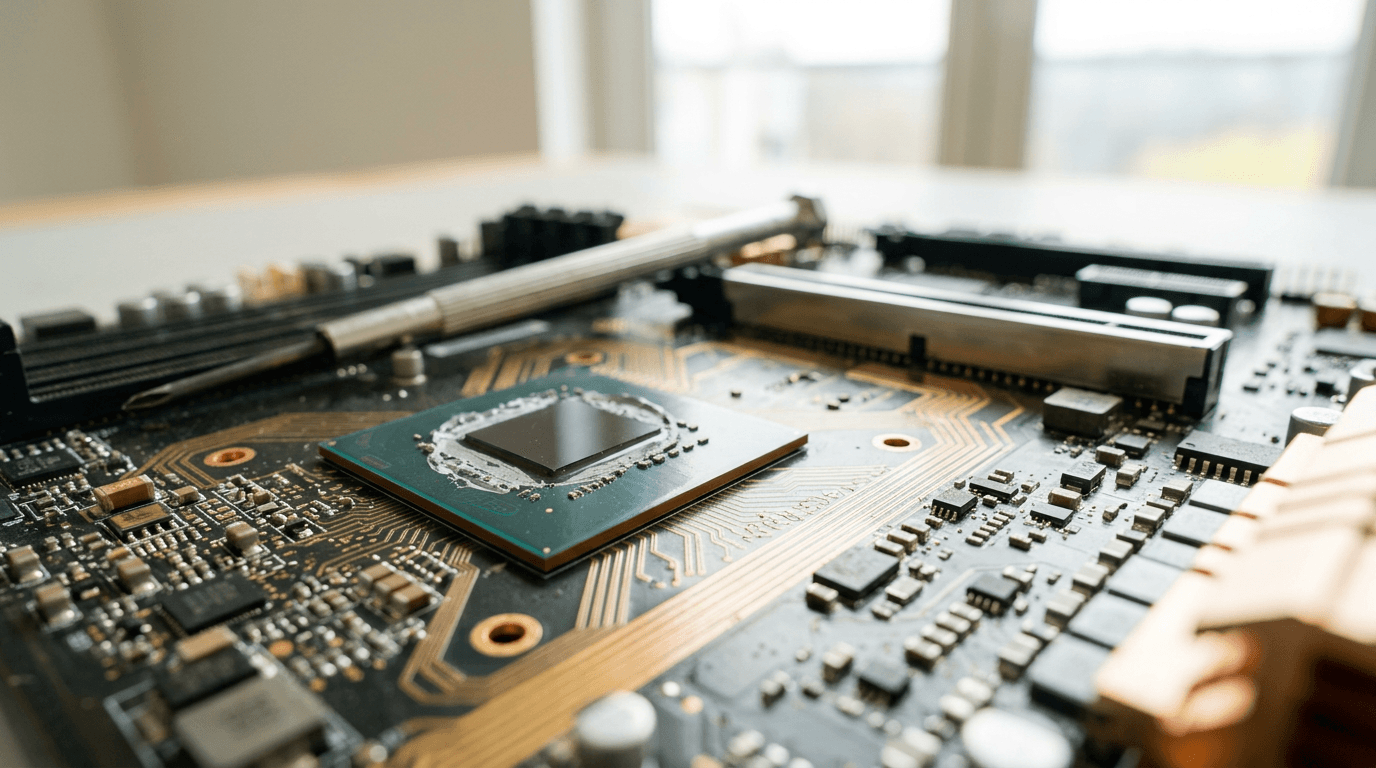
How Kernel Anti-Cheats Work: Deep Dive Into Gaming Security
Kernel anti-cheats operate at the deepest level of your operating system to detect and prevent cheating in online games. Learn how these powerful security tools work and why they spark debate.
Understanding Kernel Anti-Cheats in Modern Gaming
Learn more about two days, two coasts: spacex launches starlink batches
Online gaming faces a persistent threat from cheaters who use sophisticated software to gain unfair advantages. Traditional anti-cheat solutions scan game files and monitor application behavior, but skilled hackers routinely bypass these surface-level protections. Kernel anti-cheats emerged as the gaming industry's response to this escalating arms race, operating at the deepest level of your computer's operating system to detect and prevent cheating before it happens.
These security systems have become standard in competitive games like Valorant, Apex Legends, and Call of Duty. They spark heated debates about security, privacy, and system performance. Understanding how kernel anti-cheats work helps gamers make informed decisions about which games to play and what software to trust.
What Makes Kernel-Level Access Different From Regular Anti-Cheat?
Your computer's operating system operates in distinct privilege levels, often called "rings." User applications run in Ring 3, the least privileged level with restricted access to system resources. The kernel operates in Ring 0, the most privileged level with complete access to hardware, memory, and system processes.
Kernel anti-cheat software runs in Ring 0 alongside your operating system's core components. This elevated access allows the anti-cheat to monitor everything happening on your computer, including processes that traditional applications cannot see.
Cheats often inject code into game memory or use driver-level exploits to hide from detection. Kernel-level anti-cheats intercept these attempts before they affect gameplay. The power of Ring 0 access comes with significant responsibility—a bug or vulnerability in kernel-level software can crash your entire system or create security holes that malicious actors might exploit.
How Do Kernel Anti-Cheats Detect Cheating?
Memory Scanning and Integrity Checks
Kernel anti-cheats continuously scan game memory for unauthorized modifications. Cheats typically work by reading game memory to reveal enemy positions (wallhacks) or modifying values to enhance player abilities (aimbots). The anti-cheat creates checksums of legitimate game files and compares them against running processes.
When the system detects discrepancies, it flags the player for further investigation or immediate ban. Modern anti-cheats use sophisticated pattern recognition to identify known cheat signatures while also detecting anomalous behavior that suggests new, unknown cheats.
For a deep dive on han: a korean programming language written in rust, see our full guide
Driver and Process Monitoring
The anti-cheat monitors all drivers and processes running on your system, looking for suspicious behavior. It maintains a blacklist of known cheat software and analyzes how programs interact with the game.
For a deep dive on audio shitposting: meme culture in music production, see our full guide
Legitimate software follows predictable patterns. Cheats often exhibit telltale signs like unusual memory access or attempts to hide their presence. Kernel-level access allows the anti-cheat to detect driver-based cheats that operate at the same privilege level, identifying and blocking them before they load.
Behavioral Analysis and Machine Learning
Modern kernel anti-cheats employ machine learning algorithms to identify cheating based on player behavior. The system analyzes factors like:
- Reaction times that exceed human capability
- Crosshair movements that snap perfectly to targets
- Knowledge of enemy positions without line of sight
- Statistical anomalies in accuracy or kill patterns
- Input patterns that suggest automation or scripting
This behavioral approach catches cheaters even when their software successfully evades signature-based detection. The anti-cheat builds profiles of normal human gameplay and flags accounts that deviate significantly from expected patterns.
Why Do Kernel Anti-Cheats Start With Windows?
Most kernel anti-cheats launch when you boot your computer, not when you start the game. This early startup prevents cheats from loading first and potentially hiding from the anti-cheat. Vanguard, Riot Games' kernel anti-cheat for Valorant, pioneered this approach and sparked controversy over its always-running nature.
Early startup provides several security advantages. The anti-cheat establishes a trusted baseline of your system before any potentially malicious software loads. It verifies the integrity of critical system files and drivers, ensuring no tampering occurred before the game launches.
This approach raises legitimate concerns about system resources and privacy. An always-running kernel driver consumes memory and CPU cycles even when you're not gaming. Users worry about what data these systems collect and how companies protect that information.
The Security vs. Privacy Debate
What Can Kernel Anti-Cheats Access on Your Computer?
Kernel-level access theoretically allows anti-cheat software to read any file, monitor any process, and access any data on your computer. Game developers emphasize that their anti-cheats only collect information relevant to cheat detection, such as running processes, loaded drivers, and game-related memory.
Reputable companies implement strict data collection policies and undergo security audits. They encrypt collected data and limit access to authorized personnel. The potential for abuse exists, and users must trust developers to act responsibly with their elevated system privileges.
What Security Concerns Have Been Documented?
Security researchers have identified vulnerabilities in kernel anti-cheats that could compromise system security. In 2021, researchers discovered that Genshin Impact's kernel driver remained on systems after uninstallation and contained exploitable vulnerabilities. Attackers could leverage this driver to gain kernel-level access for malicious purposes.
These incidents highlight the risks of kernel-level software. A compromised anti-cheat becomes a potential attack vector that bypasses normal security measures. Game developers must maintain rigorous security standards and respond quickly to discovered vulnerabilities.
What Is the Performance Impact of Kernel Anti-Cheats?
Kernel anti-cheats affect system performance differently depending on implementation quality. Well-optimized solutions like Easy Anti-Cheat and BattlEye add minimal overhead, consuming 1-3% of CPU resources during gameplay. Poorly implemented systems cause stuttering, frame drops, or increased boot times.
Compatibility issues arise when kernel anti-cheats conflict with other low-level software. Virtual machines, hardware monitoring tools, RGB lighting controllers, and certain productivity applications may trigger false positives or fail to work alongside kernel anti-cheats. Users often must choose between playing protected games and using legitimate software.
How Do Cheaters Attempt to Bypass Kernel Protection?
Hardware-Based Cheats
Sophisticated cheaters moved to hardware-based solutions that operate outside the computer's software environment. DMA (Direct Memory Access) devices read game memory through PCIe slots, bypassing software-based detection entirely. These devices cost hundreds or thousands of dollars but remain undetectable by current anti-cheat technology.
Game developers combat hardware cheats through behavioral analysis and server-side validation. If a player demonstrates impossible knowledge or abilities, the system flags them regardless of how they achieved the advantage.
Exploiting Vulnerabilities
Cheat developers constantly search for vulnerabilities in anti-cheat implementations. They exploit timing windows during system startup, use signed but vulnerable drivers to gain kernel access, or find ways to inject code that mimics legitimate system processes. This cat-and-mouse game drives continuous updates and improvements to anti-cheat technology.
What Does the Future Hold for Anti-Cheat Technology?
The gaming industry explores alternatives and enhancements to kernel-level protection. Server-side validation reduces reliance on client-side anti-cheats by verifying actions on game servers. AI-powered behavioral analysis improves detection accuracy while reducing false positives.
Some developers experiment with trusted execution environments that isolate game code from potential tampering. Cloud gaming presents an interesting solution where games run on remote servers, eliminating client-side cheating opportunities entirely. However, latency concerns and infrastructure costs limit widespread adoption of this approach.
Should You Be Concerned About Kernel Anti-Cheats?
The decision to install games with kernel-level anti-cheats depends on your personal risk tolerance and trust in game developers. Major publishers like Riot Games, Activision, and Epic Games have strong incentives to protect user data and maintain secure systems. Their reputations and businesses depend on user trust.
Consider these factors when evaluating kernel anti-cheats:
- The developer's track record for security and transparency
- Whether the anti-cheat runs only during gameplay or constantly
- Your comfort level with granting kernel-level access
- The importance of the game versus potential risks
You can always uninstall games and their associated anti-cheats if concerns arise. Most kernel drivers remove themselves during the uninstallation process, though verifying complete removal provides peace of mind.
Balancing Security and User Rights
Kernel anti-cheats represent the current frontier in the ongoing battle against gaming cheats. They provide powerful detection capabilities by operating at the deepest system level, catching sophisticated cheats that evade traditional solutions.
This protection comes at the cost of granting significant system access to third-party software. The technology continues evolving as developers balance effective cheat prevention with user privacy and system security. Understanding how these systems work empowers gamers to make informed decisions about which games to play and what level of access they're comfortable granting.
Continue learning: Next, explore windows 11 user directory naming: a business game-changer
budget:token_usage Input: 2156 tokens Output: 1737 tokens Total: 3893 tokens </budget:token_usage>
Related Articles

Transforming Gaza: From Conflict Zone to Tech Hub
A leaked plan from the Trump administration reveals a bold strategy to turn Gaza into a thriving high-tech hub. Discover the potential.
Sep 3, 2025

Gaza's Tech Revolution: Trump's Bold High-Tech Vision
A leaked plan from the Trump administration unveils a vision to make Gaza a high-tech hub, focusing on AI, cybersecurity, and digital innovation.
Sep 3, 2025

AI Tools Reveal Identities of ICE Officers Online
AI's emerging role in unmasking ICE officers spotlights the intersection of technology, privacy, and ethics, sparking a crucial societal debate.
Sep 2, 2025
Comments
Loading comments...
