- Home
- Technology
- Bugs Rust Won't Catch: Beyond Memory Safety Guarantees
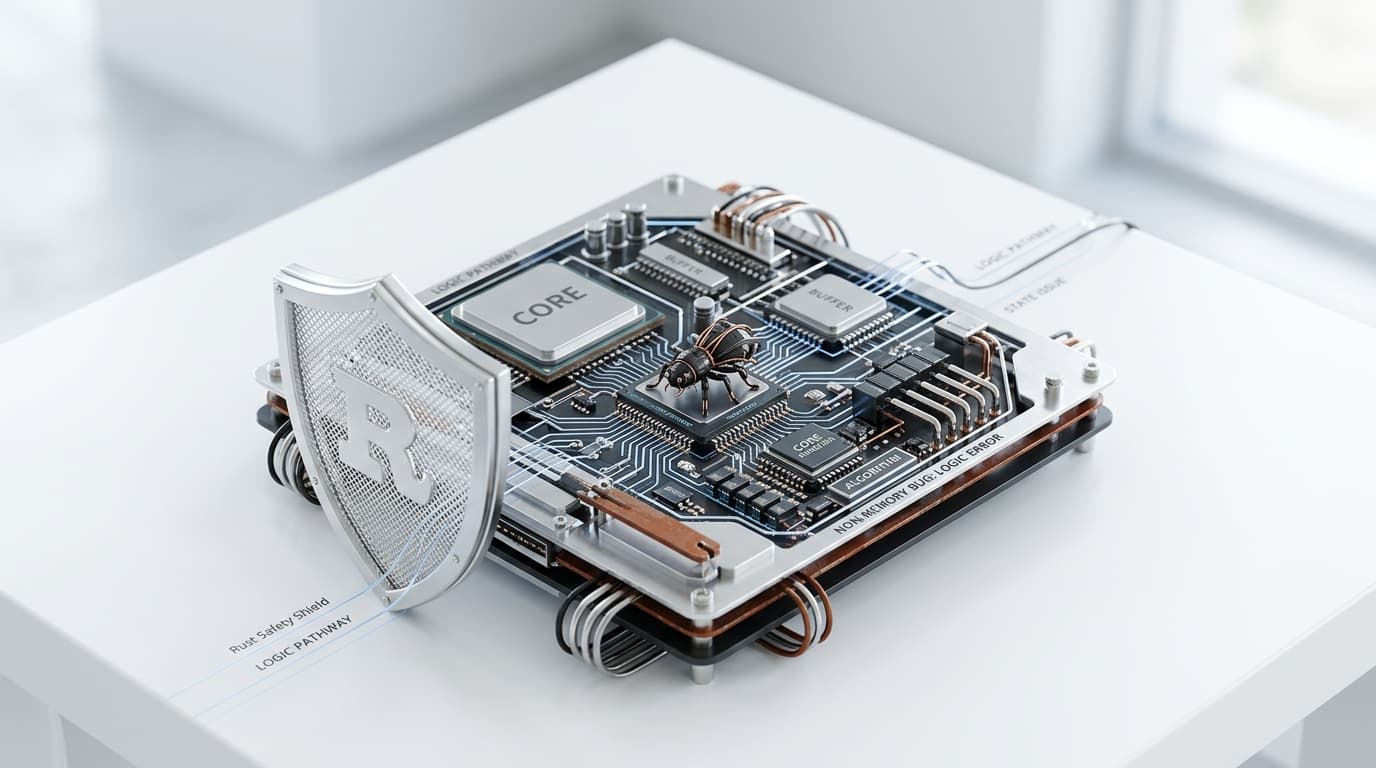
Bugs Rust Won't Catch: Beyond Memory Safety Guarantees
Rust prevents memory bugs brilliantly, but logic errors, deadlocks, integer overflow, and unsafe code vulnerabilities still slip through. Learn what the compiler misses.
What Bugs Can Rust Not Catch? Understanding the Limits of Compile-Time Safety
Learn more about court reverses pause on epic games ruling vs apple
Rust has earned its reputation as a systems programming language that eliminates entire classes of bugs through strict compiler checks. Developers praise its ability to catch memory safety issues, data races, and null pointer dereferences at compile time. Yet despite these powerful guarantees, Rust cannot protect you from every programming error.
Understanding which bugs Rust won't catch helps you write more robust code and avoid a false sense of security.
Can Rust Catch Logic Errors and Business Logic Bugs?
Rust's compiler excels at enforcing memory safety, but it cannot understand your program's intended behavior. Logic errors remain your responsibility as a developer.
When you implement an algorithm incorrectly, Rust compiles the code without complaint. If you write a sorting function that produces incorrect results or a calculation that uses the wrong formula, the compiler sees only syntactically valid code. These semantic errors require human review, testing, and domain expertise to identify.
Business logic bugs pose similar challenges. Your e-commerce checkout might charge customers twice, or your authentication system might grant unauthorized access. Rust ensures your code runs safely, but it cannot verify that your code implements the correct business rules.
What Logic Errors Slip Through Rust's Compiler?
Several logic errors commonly appear in Rust codebases despite the compiler's vigilance:
- Off-by-one errors in loop iterations or array indexing logic
- Incorrect conditional statements that reverse intended behavior
- Mathematical operations using wrong operators or order of operations
- State machine implementations that allow invalid state transitions
- Algorithm implementations that produce correct types but wrong values
How Does Rust Handle Integer Overflow?
For a deep dive on why apple ultra rumors make perfect sense right now, see our full guide
Rust's handling of integer overflow differs between debug and release builds, creating potential pitfalls. In debug mode, integer overflow causes a panic. In release mode, overflow wraps around by default.
This behavior means your code might work perfectly during development but fail silently in production. A counter that exceeds its maximum value wraps to zero, potentially causing subtle bugs in calculations or comparisons.
For a deep dive on lifehacker deals live blog: best tech sales in one place, see our full guide
You can use checked arithmetic methods like "checked_add()" or "saturating_mul()" to handle overflow explicitly. However, Rust does not force you to use these methods. The compiler accepts standard arithmetic operators without warning about potential overflow scenarios.
Does Rust Protect Against Floating-Point Precision Errors?
Floating-point arithmetic introduces additional complexity that Rust cannot guard against. Comparing floats for equality often fails due to rounding errors. Accumulated precision loss in repeated calculations produces unexpected results.
Rust provides the same IEEE 754 floating-point semantics as other languages, including special values like NaN and infinity. Your code must handle these edge cases explicitly.
Can Rust Prevent Deadlocks and Liveness Issues?
Rust prevents data races through its ownership system and the Send/Sync traits. This guarantee eliminates undefined behavior from concurrent access, but it does not prevent all concurrency bugs.
Deadlocks occur when two or more threads wait indefinitely for resources held by each other. Rust's type system cannot detect these circular dependencies at compile time. You can easily create a deadlock by acquiring multiple locks in different orders across threads.
Livelocks present another challenge where threads remain active but make no progress. Priority inversion, where low-priority threads block high-priority ones, also falls outside Rust's safety guarantees.
What About Resource Starvation and Performance Bugs?
Rust does not protect against resource starvation where some threads never get access to shared resources. A poorly designed scheduler or lock acquisition strategy leaves threads waiting indefinitely.
Performance bugs represent another category Rust cannot catch. Your code might use inefficient algorithms, excessive memory allocations, or unnecessary synchronization. The compiler ensures safety but not efficiency.
Why Are Panics and Unwrap Calls Dangerous?
The "unwrap()" and "expect()" methods provide convenient ways to extract values from Option and Result types. However, calling these methods on None or Err variants causes your program to panic.
Rust's compiler does not warn you about potential panics from unwrap calls. You might unwrap a value that seems guaranteed to exist but fails under edge cases you did not consider.
Proper error handling requires matching on Option and Result types or using the question mark operator. Many developers unwrap too liberally during initial development, creating fragile code that fails unexpectedly.
What Risks Does Unsafe Code Introduce?
The "unsafe" keyword allows you to bypass Rust's safety checks when necessary. Inside unsafe blocks, you can dereference raw pointers, call unsafe functions, and access mutable static variables.
Rust trusts you to maintain safety invariants within unsafe code. The compiler cannot verify that your unsafe operations preserve memory safety or prevent data races. Bugs in unsafe code cause the same undefined behavior that Rust normally prevents.
Many Rust programs use unsafe code for performance optimization or FFI with C libraries. Each unsafe block represents a potential source of memory corruption, use-after-free bugs, or other safety violations.
How Does FFI Affect Rust's Safety Guarantees?
Calling functions in C libraries through FFI introduces additional risks. Rust cannot verify the safety of external code. A C function might have buffer overflows, null pointer dereferences, or thread safety issues.
Even safe Rust code that calls unsafe external functions inherits those vulnerabilities. You must trust that external dependencies maintain their own safety guarantees.
How Can You Protect Against Bugs Rust Cannot Catch?
Accepting that Rust cannot catch every bug helps you develop better defensive programming practices. Comprehensive testing remains essential despite Rust's compile-time guarantees.
Write unit tests that cover edge cases and boundary conditions. Use property-based testing tools like "proptest" to verify invariants across random inputs. Integration tests help catch logic errors that unit tests might miss.
Code review catches many bugs that compilers cannot detect. Another developer might spot logic errors, identify potential deadlocks, or notice missing error handling.
Static analysis tools and linters provide additional safety checks. Clippy warns about common mistakes and suggests idiomatic patterns. Tools like Miri detect some undefined behavior in unsafe code through interpretation.
How Does API Design Prevent Bugs?
Careful API design prevents entire classes of bugs. Use types to encode invariants and make invalid states unrepresentable. Leverage Rust's type system to guide users toward correct usage.
Document preconditions, postconditions, and invariants clearly. Write defensive code that validates inputs and handles errors gracefully. Consider using formal methods or model checking for critical components.
The Bottom Line on Rust's Limitations
Rust's memory safety guarantees represent a significant advancement in programming language design, eliminating entire categories of bugs that plague C and C++ programs. However, Rust remains a tool that requires skilled developers to use effectively.
Logic errors, arithmetic overflow, deadlocks, panics, and unsafe code vulnerabilities all escape the compiler's scrutiny. Understanding these limitations helps you write more robust Rust code by combining the language's safety features with thorough testing, careful design, and defensive programming practices.
Continue learning: Next, explore airpods pro alternatives: cheaper but good enough?
No compiler can replace human judgment and expertise in building reliable software.
Related Articles

AI Tools Reveal Identities of ICE Officers Online
AI's emerging role in unmasking ICE officers spotlights the intersection of technology, privacy, and ethics, sparking a crucial societal debate.
Sep 2, 2025

AI's Role in Unveiling ICE Officers' Identities
AI unmasking ICE officers underscores a shift towards transparent law enforcement, raising questions about privacy and ethics in the digital age.
Sep 2, 2025

AI Unveils ICE Officers: A Tech Perspective
AI's role in unmasking ICE officers highlights debates on privacy, ethics, and the balance between transparency and security in law enforcement.
Sep 2, 2025
Comments
Loading comments...
