- Home
- Technology
- US Special Forces Soldier Arrested After $400K Maduro Raid
US Special Forces Soldier Arrested After $400K Maduro Raid
When digital surveillance meets covert operations, even elite soldiers leave traces. A US special forces member's arrest reveals how technology exposed a $400K payday from a botched coup.

US Special Forces Soldier Arrested After Allegedly Winning $400K on Maduro Raid
Learn more about the mandalorian and grogu: can this film restore star wars?
A US special forces soldier allegedly pocketed $400,000 from a failed coup attempt against Venezuelan President Nicolas Maduro. He probably did not anticipate how digital forensics and cybersecurity tools would unravel his involvement. The arrest highlights a critical intersection between modern warfare, financial tracking technology, and the digital footprints that even elite operatives cannot escape.
Advanced surveillance systems, blockchain analysis, and digital banking records have transformed investigations into covert military operations. The technology sector's innovations in financial forensics now make it nearly impossible to hide large money transfers, even for trained special operations personnel.
How Did Digital Forensics Expose the Special Forces Soldier?
Modern financial surveillance systems caught what traditional intelligence might have missed. Banking institutions now employ sophisticated AI-powered algorithms that flag unusual transactions, especially those involving large sums crossing international borders.
The $400,000 payment allegedly received by the soldier triggered multiple digital alarms. Financial institutions use machine learning models trained to detect patterns associated with illicit activities, including payments for mercenary services or unauthorized military operations. Cybersecurity experts note that cryptocurrency transactions, wire transfers, and even cash deposits leave digital signatures that investigators can follow across multiple jurisdictions.
What Financial Forensics Technology Traced the Money?
Investigators likely employed several cutting-edge technologies to trace the money:
For a deep dive on macbook pro m5 chip: advanced features & release date, see our full guide
- Blockchain analysis tools that track cryptocurrency movements across wallets and exchanges
- AI-powered transaction monitoring systems that identify suspicious payment patterns
- Digital banking forensics software that reconstructs financial timelines
- Cross-border payment tracking platforms that monitor international money flows
- Social media intelligence gathering that connects financial activity to physical locations
These tools represent billions of dollars in cybersecurity investment by governments and financial institutions. The technology has become so sophisticated that it can identify connections between seemingly unrelated transactions across multiple countries and currencies.
For a deep dive on why i write (1946): orwell's tech lessons for modern coders, see our full guide
What Role Did Technology Play in the Failed Venezuela Coup?
The botched operation against Maduro in 2020 became known as "Operation Gideon." Several participants were captured, and their smartphones, communications, and digital devices provided investigators with treasure troves of evidence.
Digital communications analysis revealed coordination patterns, payment structures, and participant identities. Even encrypted messaging apps left metadata that helped investigators piece together the operation's timeline and financial arrangements. Cybersecurity researchers have long warned that operational security failures often involve technology misuse.
What Operational Security Failures Led to the Arrest?
Special forces personnel receive extensive training in operational security, yet technology creates vulnerabilities that traditional training may not address. The soldier's alleged acceptance of a large payment violated basic principles of covert operations in the digital age.
Digital banking records create permanent audit trails that investigators can access through legal channels. Even attempts to obscure payments through intermediaries leave traces in modern financial systems. Algorithms can now process millions of transactions in seconds, identifying patterns that human investigators might miss.
How Does This Case Impact Military Cybersecurity?
This arrest sends shockwaves through the private military contractor industry and special operations community. The incident reveals how thoroughly modern technology has penetrated every aspect of covert operations.
Military cybersecurity protocols must evolve to address these new realities. Traditional operational security focused on physical surveillance and human intelligence. Today's threats include digital forensics, AI-powered analysis, and global financial surveillance networks.
The technology sector has created tools that make financial anonymity nearly impossible. Even sophisticated money laundering schemes leave digital breadcrumbs that advanced analytics can follow.
Can Covert Operations Survive in a Digital World?
Surveillance technology advances create unprecedented challenges for covert operations. Biometric databases, facial recognition systems, and ubiquitous digital cameras create environments where anonymity becomes increasingly difficult.
Financial technology companies continue developing more sophisticated tracking systems. These innovations serve legitimate purposes like preventing terrorism financing and money laundering, but they also make unauthorized military activities easier to detect. Blockchain technology, once considered anonymous, now faces extensive analysis tools that can trace transactions across complex networks.
What Legal Questions Does Surveillance Technology Raise?
The case raises important questions about surveillance technology's role in monitoring military personnel. How much financial monitoring is appropriate for service members and veterans? Where does legitimate security screening end and privacy invasion begin?
Digital rights advocates argue that pervasive financial surveillance creates risks for civil liberties. However, national security experts counter that such monitoring prevents unauthorized military actions that could trigger international incidents. The technology exists in a gray area where security needs clash with privacy rights.
How Has Technology Changed Military Justice?
Military justice systems increasingly rely on digital evidence that previous generations never encountered. Prosecutors now present smartphone data, financial records, and social media posts as primary evidence in courts-martial.
This technological shift requires new expertise within military legal systems. Judge advocates must understand blockchain analysis, digital forensics, and cybersecurity concepts to effectively prosecute or defend cases. The soldier's case will likely feature extensive digital evidence that demonstrates how thoroughly technology has transformed military investigations.
What Should the Technology Sector Learn From This Case?
This incident demonstrates both the power and the implications of financial surveillance technology. The same systems that caught an allegedly corrupt soldier also raise questions about privacy, oversight, and technological capability limits.
Technology companies developing financial forensics tools must consider how their innovations affect individual privacy and international relations. Cybersecurity professionals should note how this case illustrates the impossibility of true financial anonymity in modern systems. Even elite special forces personnel with operational security training leave digital trails that sophisticated analysis can follow.
The Future of Financial Forensics and Military Operations
The arrest of a US special forces soldier after allegedly receiving $400,000 from the failed Maduro raid reveals how completely digital technology has transformed covert operations and financial crimes investigation. Advanced AI algorithms, blockchain analysis tools, and global financial surveillance networks make hiding large money transfers nearly impossible, even for trained operatives.
Continue learning: Next, explore apple's lightning advancement could transform mac pro
Technology has eliminated many traditional methods of financial anonymity. As surveillance systems grow more sophisticated, both legitimate security operations and unauthorized activities face unprecedented scrutiny. The intersection of cybersecurity, financial forensics, and military operations will continue shaping how nations conduct and investigate covert actions in an increasingly transparent digital world.
Related Articles
AI's Role in Unveiling ICE Officers' Identities
AI unmasking ICE officers underscores a shift towards transparent law enforcement, raising questions about privacy and ethics in the digital age.
Sep 2, 2025
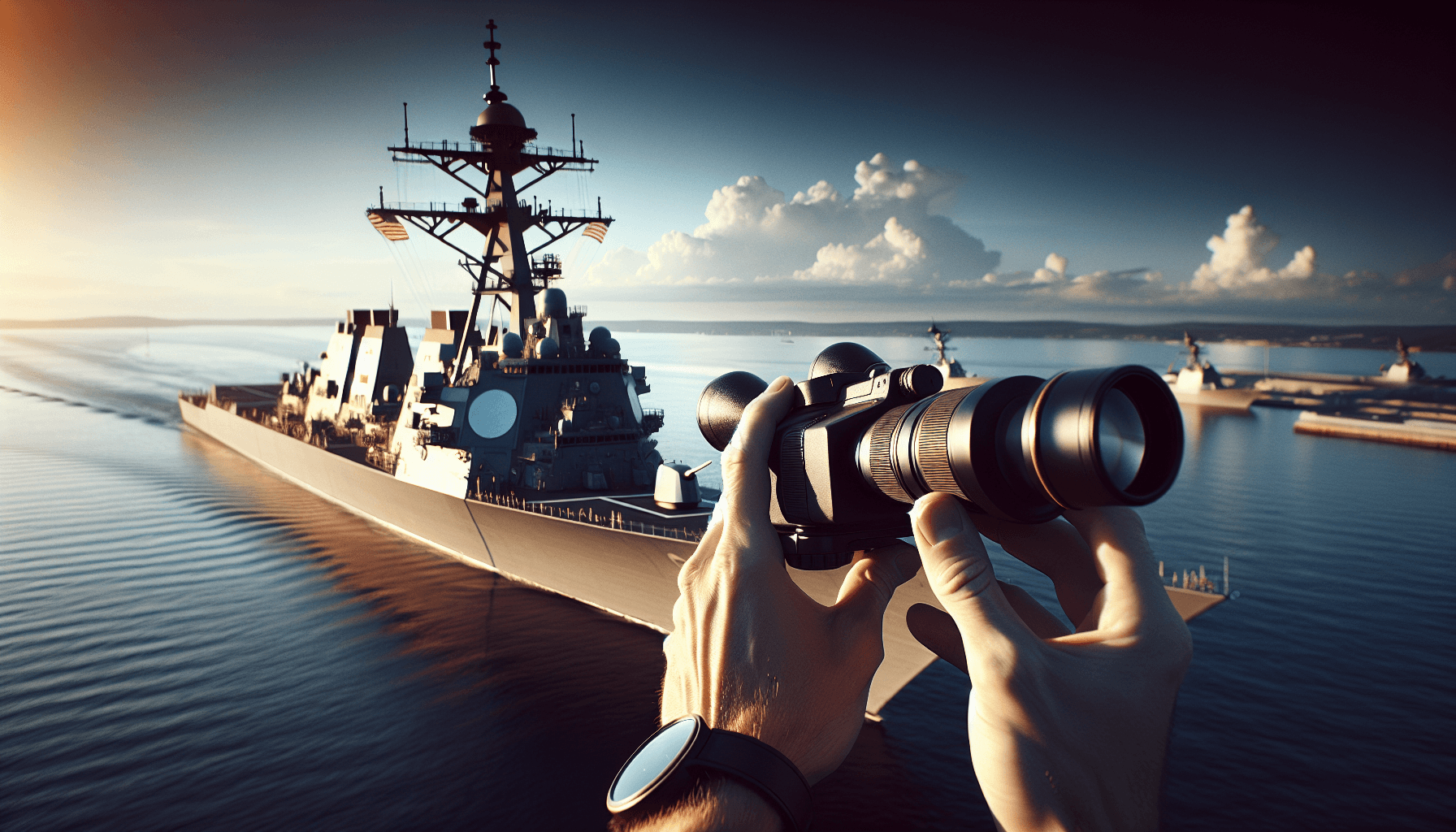
Maduro's Alarm Over US Naval Deployment Near Venezuela
Maduro labels US naval deployment near Venezuela as a "bloody threat," spotlighting the role of tech and cybersecurity in modern geopolitics.
Sep 2, 2025
Transforming Gaza: From Conflict Zone to Tech Hub
A leaked plan from the Trump administration reveals a bold strategy to turn Gaza into a thriving high-tech hub. Discover the potential.
Sep 3, 2025