- Home
- Technology
- Trust Erosion in Azure: Former Core Engineer Reveals Key ...
Trust Erosion in Azure: Former Core Engineer Reveals Key ...
An insider's perspective on the strategic and technical decisions that compromised Azure's reliability and eroded customer trust over time.

Understanding the Trust Crisis in Azure
Learn more about 26 signs you're destined to become a millionaire
Microsoft Azure stands as one of the world's largest cloud platforms, serving millions of enterprises globally. Yet beneath its polished marketing lies a troubling pattern of decisions that eroded trust in Azure among both customers and engineers. A former Azure Core engineer recently shared critical insights into the strategic choices that compromised the platform's reliability and reputation.
These revelations matter because they expose systemic issues affecting businesses that depend on cloud infrastructure for their operations. When trust breaks down at the infrastructure level, the consequences ripple through entire organizations.
Why Did Azure Shift from Engineering Excellence to Business Metrics?
Azure's early years prioritized technical excellence and robust architecture. Engineers had autonomy to make decisions based on system reliability and customer needs. This culture produced innovative solutions and a platform that genuinely competed with AWS on technical merit.
The transformation began when business metrics overtook engineering principles. Leadership increasingly measured success through revenue growth and market share rather than system uptime or customer satisfaction. Teams faced pressure to ship features quickly, often at the expense of thorough testing and architectural soundness.
How Do Quarterly Targets Undermine System Reliability?
Quarterly business reviews became the driving force behind technical decisions. Product managers prioritized features that could be demonstrated to executives over critical infrastructure improvements.
This created a dangerous pattern where visible additions took precedence over invisible stability work. Engineers warned about accumulating technical debt, but these concerns rarely reached decision-makers.
The gap between those building the systems and those directing strategy widened significantly. Critical maintenance windows got postponed, monitoring systems remained incomplete, and incident response procedures became inconsistent.
Which Cost-Cutting Measures Compromised Azure Quality?
Azure implemented aggressive cost reduction strategies that directly impacted service quality. The platform reduced redundancy in certain regions to improve profit margins. These decisions saved money on paper but increased vulnerability to cascading failures.
Staffing cuts affected teams responsible for core infrastructure monitoring and incident response. Experienced engineers left the company, taking institutional knowledge with them. New hires received abbreviated training, leading to gaps in understanding complex system interactions.
For a deep dive on spacex $2 trillion ipo: what it means for sports tech, see our full guide
What Is the Hidden Price of Cheaper Hardware?
Hardware procurement shifted toward lower-cost components to meet budget targets. While individual components met minimum specifications, they lacked the reliability margins that enterprise workloads demand.
For a deep dive on microsoft launches 3 ai models to challenge openai & google, see our full guide
Failure rates increased incrementally, creating more work for already stretched operations teams. The former engineer noted that Azure's hardware refresh cycles extended beyond recommended timelines.
Aging infrastructure remained in production longer than advisable, increasing the probability of unexpected outages. These decisions saved capital expenditure but generated operational costs through increased incident frequency.
How Does Azure Handle Transparency and Customer Communication?
Azure's approach to incident communication became increasingly problematic. When outages occurred, initial statements often minimized severity or provided incomplete information. Root cause analysis reports arrived weeks late, if at all.
Customers struggled to understand what actually happened and whether their data remained secure. Internal pressure to protect Azure's reputation led to sanitized public statements. Engineers who understood the technical details rarely participated in customer-facing communications.
What Happened to Post-Incident Reviews?
Post-incident review processes deteriorated over time. Thorough analysis requires dedicated time and resources, both of which became scarce.
Teams rushed through reviews to return to feature development. Critical lessons went unlearned, allowing similar incidents to recur.
The engineer revealed that recommendations from incident reviews often went unimplemented. Fixing root causes required engineering time that conflicted with feature delivery schedules. Leadership consistently chose new capabilities over addressing known vulnerabilities.
Which Metrics Masked Real Problems in Azure?
Azure reported impressive uptime statistics that didn't reflect customer experience. The platform calculated availability using methods that excluded certain types of outages or degraded performance.
Customers experienced problems that never appeared in official SLA reports. This disconnect between reported metrics and actual reliability damaged trust significantly.
Enterprises made decisions based on published availability numbers, only to discover that real-world performance fell short. The gap between marketing claims and operational reality became impossible to ignore.
Why Don't Traditional SLAs Tell the Whole Story?
Service Level Agreements focus on binary availability, measuring whether services respond to requests. They ignore performance degradation, increased latency, or partial functionality loss.
Azure's SLAs technically remained intact during incidents where services were severely impaired but not completely offline. Customers needed visibility into actual performance characteristics, not just up/down status.
The former engineer emphasized that internal monitoring showed problems that external metrics concealed. This information asymmetry prevented customers from making informed decisions about their infrastructure.
What Security Decisions Raised Red Flags?
Security practices came under pressure from the same business-first mentality. Vulnerability remediation timelines stretched longer as teams prioritized feature work. Some security improvements required architectural changes that conflicted with backward compatibility commitments.
The engineer described situations where known vulnerabilities remained unpatched for extended periods. Risk assessments got overruled by business considerations.
Security teams lacked the authority to halt feature releases that introduced new attack surfaces. This pattern created significant exposure for customers trusting Azure with sensitive workloads.
What Is the Compliance Theater Problem?
Azure pursued compliance certifications aggressively for marketing purposes. However, maintaining those certifications became a checkbox exercise rather than a genuine security commitment.
Audits focused on documentation and processes rather than actual security posture. Internal security assessments sometimes revealed gaps that compliance audits missed.
The pressure to maintain certifications led to situations where teams addressed audit findings without fixing underlying security weaknesses. This created a false sense of security for customers relying on those certifications.
What Does This Mean for Enterprise Customers?
Enterprises trusting Azure with critical workloads need to understand these dynamics. The platform remains functional and serves many organizations successfully. However, blind trust in any cloud provider creates unnecessary risk.
Customers should implement independent monitoring, maintain multi-cloud strategies where feasible, and thoroughly test disaster recovery procedures. Understanding that business pressures affect all cloud providers helps organizations make realistic risk assessments.
What Are Key Actions for Risk Mitigation?
Deploy comprehensive monitoring that tracks actual performance, not just availability. Your monitoring should capture latency, error rates, and degraded functionality.
Maintain detailed runbooks for handling cloud provider outages. Regularly test failover procedures and backup restoration processes to ensure they work when needed.
Diversify critical workloads across multiple availability zones or regions. Review SLAs carefully and understand what they actually guarantee versus what they exclude.
What Lessons Does Azure Offer the Broader Cloud Industry?
Azure's trust erosion offers important lessons for the entire cloud computing sector. When business metrics dominate engineering culture, reliability suffers.
Short-term thinking creates long-term technical debt that becomes increasingly difficult to address. The industry needs better frameworks for measuring and reporting actual service quality.
Customers deserve transparent communication about incidents and honest assessments of risk. Cloud providers must balance growth objectives with the fundamental responsibility to maintain reliable infrastructure.
How Can Azure Rebuild Trust Through Cultural Change?
The decisions that eroded trust in Azure stemmed from prioritizing business metrics over engineering excellence. Cost-cutting measures, inadequate transparency, misleading metrics, and security compromises created a pattern that undermined customer confidence.
These issues affect not just Azure but reflect broader industry challenges. Rebuilding trust requires cultural transformation that empowers engineers to prioritize reliability and security.
Continue learning: Next, explore ai drives college students to switch majors: new poll
Cloud providers must recognize that sustainable growth depends on customer trust, which only comes through consistent delivery of reliable services. For customers, this situation reinforces the importance of skepticism, independent verification, and comprehensive risk management strategies when depending on any cloud platform.
Related Articles
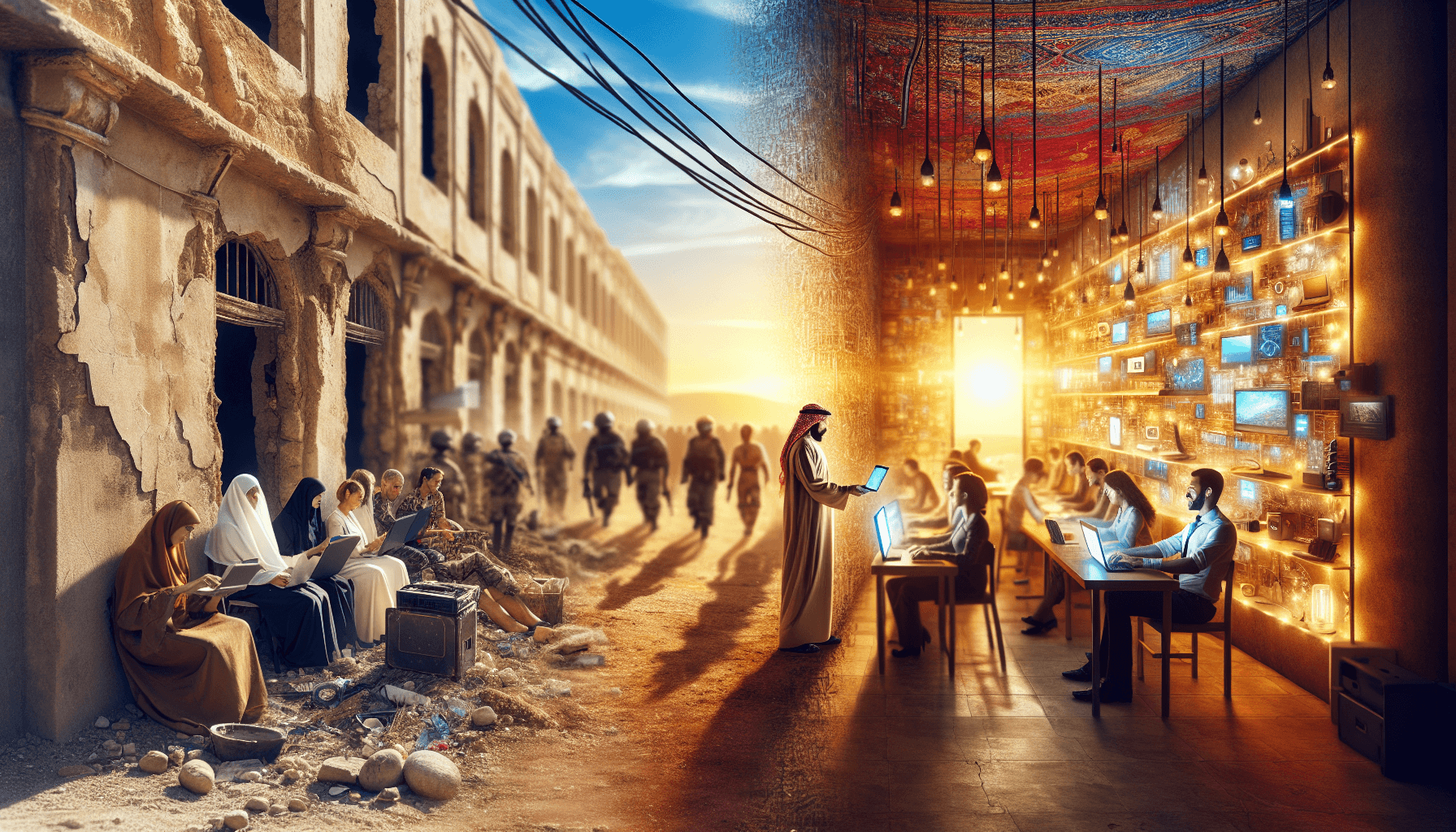
Transforming Gaza: From Conflict Zone to Tech Hub
A leaked plan from the Trump administration reveals a bold strategy to turn Gaza into a thriving high-tech hub. Discover the potential.
Sep 3, 2025
AI Tools Reveal Identities of ICE Officers Online
AI's emerging role in unmasking ICE officers spotlights the intersection of technology, privacy, and ethics, sparking a crucial societal debate.
Sep 2, 2025
AI's Role in Unveiling ICE Officers' Identities
AI unmasking ICE officers underscores a shift towards transparent law enforcement, raising questions about privacy and ethics in the digital age.
Sep 2, 2025