- Home
- Technology
- The One Dollar Counterfeiter: Tech's Strangest Crime Story
The One Dollar Counterfeiter: Tech's Strangest Crime Story
Why would criminals counterfeit one dollar bills? This strange phenomenon reveals fascinating insights about technology, security features, and the irrational side of cybercrime.
Why Would Anyone Counterfeit One Dollar Bills?
Learn more about openai trial exposes $852bn tech rivalry lessons for sports
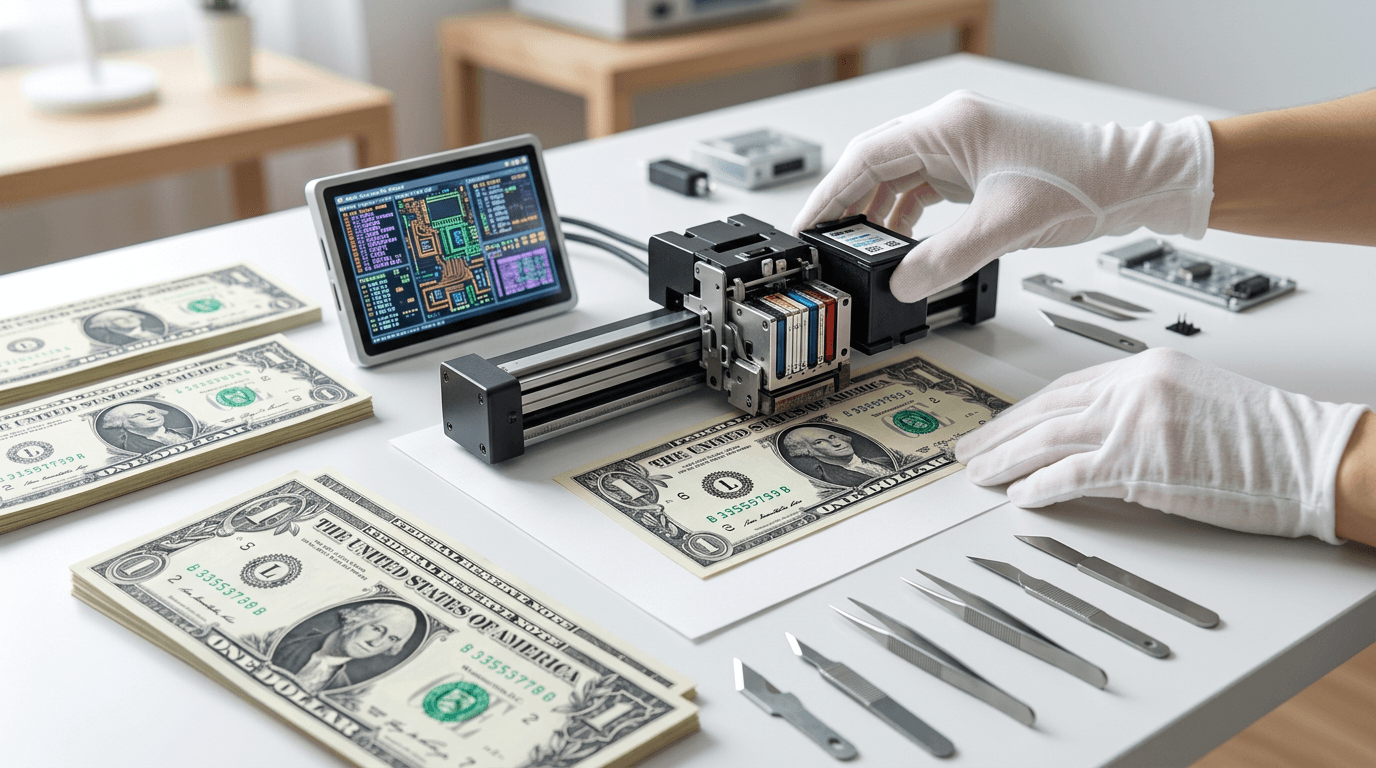
Counterfeiters typically target high-value bills to maximize their criminal profits. But one peculiar case defied all logic when criminals began producing fake one dollar bills. Experts call this the most economically irrational crime in modern history.
This bizarre phenomenon reveals fascinating insights about human behavior, security technology, and the economics of digital crime. The one dollar counterfeiter story stands as a testament to how technology can be misused in ways that defy conventional wisdom.
Does Counterfeiting One Dollar Bills Make Economic Sense?
The economics of counterfeiting one dollar bills make absolutely no sense. The cost of paper, ink, printing equipment, and time far exceeds the face value of the counterfeit product. Yet documented cases exist of individuals producing fake singles with remarkable dedication.
Law enforcement officials have encountered several theories. Some counterfeiters used one dollar bills as practice runs before attempting higher denominations. Others suffered from mental health issues that impaired their judgment.
A few cases involved individuals who simply wanted to prove they could beat the system, regardless of profit. The most infamous case involved a counterfeiter who spent thousands of dollars on printing equipment to produce bills worth a fraction of his investment. He distributed them at local stores, getting caught within weeks because merchants rarely scrutinize singles closely enough to notice quality issues.
What Security Features Protect One Dollar Bills?
Even one dollar bills contain sophisticated security features that most people never notice. The U.S. Bureau of Engraving and Printing employs multiple layers of protection.
Special paper composition: Currency uses a cotton-linen blend that feels distinctly different from regular paper.
Security threads: Embedded fibers visible under UV light spell out the denomination.
For a deep dive on why capital one isn't worried about high auto prices, see our full guide
Microprinting: Tiny text invisible to the naked eye appears clear under magnification.
Serial numbers: Unique identifiers tracked through sophisticated database systems.
For a deep dive on three men charged in $1.2m apple gear hijacking, see our full guide
These features make counterfeiting increasingly difficult, even with access to high-quality digital printing technology. Modern scanners and printers often include built-in detection systems that prevent reproducing currency images.
How Has Digital Technology Changed Counterfeiting?
The rise of digital imaging technology initially made counterfeiting more accessible to amateur criminals. High-resolution scanners and color printers became affordable consumer products in the 1990s and early 2000s. This democratization of printing technology led to a spike in counterfeit attempts.
However, technology companies responded by implementing counterfeit deterrence systems. Adobe Photoshop uses the Counterfeit Deterrence System (CDS) that recognizes currency patterns and blocks editing. Most modern printers embed forensic tracking dots invisible to the human eye but traceable by law enforcement.
The Secret Service maintains a sophisticated digital database that tracks counterfeit bills by analyzing printing patterns, paper composition, and other forensic markers. This technology helps identify counterfeiting operations and link seemingly unrelated cases across different geographic regions.
How Do Police Catch One Dollar Counterfeiters?
Modern counterfeiting investigations rely heavily on technology and data analysis. The Secret Service uses advanced forensic techniques to trace fake bills back to their source. Digital forensics experts examine printer artifacts, paper chemical composition, and distribution patterns.
Machine learning algorithms now help identify counterfeit currency faster than human inspection alone. Banks and retail locations use automated currency validators that check multiple security features simultaneously. These systems reject suspicious bills instantly, preventing them from entering circulation.
The one dollar counterfeiter cases typically get solved quickly because the low denomination requires high volume distribution. Passing hundreds of fake singles attracts attention far faster than carefully placing a few counterfeit hundreds.
What Cybersecurity Lessons Apply to Counterfeiting?
The one dollar counterfeiter phenomenon mirrors certain cybersecurity threats where attackers expend enormous resources for minimal gains. Some hackers spend months developing exploits to steal small amounts from numerous accounts rather than targeting high-value systems efficiently.
This behavior reflects several psychological factors. Some criminals enjoy the challenge more than the reward. Others lack the sophistication to execute more profitable schemes.
Many simply fail to calculate the risk-reward ratio properly. Cybersecurity professionals study these irrational threat actors because they can cause disproportionate damage. A determined attacker with poor judgment might compromise systems in unpredictable ways that sophisticated criminals would avoid.
What Does This Teach About Technology and Crime?
The one dollar counterfeiter cases offer valuable lessons for understanding technology-enabled crime. First, access to technology does not guarantee its effective use. Criminals need both technical skills and strategic thinking to succeed.
Second, security measures work best in layers. Currency protection combines physical features, chemical markers, and digital tracking. This multi-layered approach makes counterfeiting prohibitively difficult for most would-be criminals.
Third, human behavior often defies rational economic models. Technology enables crime, but psychology drives criminal decision-making in ways that algorithms cannot always predict.
What Modern Technology Prevents Counterfeiting?
Currency security continues evolving as printing technology advances. The Bureau of Engraving and Printing constantly develops new features to stay ahead of counterfeiters.
3D security ribbons: Woven directly into paper with moving images.
Color-changing ink: Shifts between colors when viewed at different angles.
Raised printing: Creates texture detectable by touch.
Watermarks: Visible when held up to light, impossible to reproduce with standard printers.
These features make even attempting to counterfeit low-denomination bills a technically challenging endeavor. The one dollar bill receives fewer updates than higher denominations, but it still contains enough security features to deter most amateur counterfeiters.
Why Don't Stores Check Every Dollar Bill?
Retail businesses face a cost-benefit analysis when checking currency authenticity. Spending 30 seconds verifying a one dollar bill costs more in labor than the potential loss. This creates a vulnerability that some counterfeiters attempt to exploit.
However, automated detection systems at banks catch counterfeit bills when businesses make deposits. The fake currency gets traced back through transaction records, leading investigators to the source.
This delayed detection actually helps law enforcement build stronger cases by documenting distribution patterns. The Secret Service estimates that less than 0.01% of currency in circulation is counterfeit, thanks to sophisticated security features and aggressive enforcement. The one dollar counterfeiter represents such an anomaly that cases often become training examples for new agents.
What Security Lessons Apply Beyond Currency?
The one dollar counterfeiter story provides insights applicable to broader technology security challenges. Organizations should implement security measures proportional to asset value while maintaining baseline protections everywhere. Even low-value targets need adequate security because attackers do not always behave rationally.
Security systems should assume some attackers will ignore economic logic. Defense strategies must account for determined adversaries willing to lose money to achieve their goals. This means implementing detection systems that catch high-volume, low-value attacks as effectively as they catch targeted, high-value breaches.
The human element remains crucial. Technology enables both crime and prevention, but human judgment determines how effectively these tools get deployed. Training people to recognize suspicious behavior complements automated detection systems.
What Does the One Dollar Counterfeiter Teach Us?
The one dollar counterfeiter represents a fascinating intersection of technology, economics, and psychology. These cases demonstrate that access to sophisticated printing technology does not guarantee profitable criminal enterprise. They also highlight how multi-layered security features protect even low-value currency from exploitation.
For technology professionals, these stories offer valuable lessons about security design, threat modeling, and the importance of considering irrational actors. The most effective security systems protect against both sophisticated attackers and determined amateurs who ignore economic logic.
Continue learning: Next, explore asus rog strix oled xg34wcdms & xg129c: market analysis
Human behavior often defies prediction. Technology continues advancing, but understanding the human element remains essential for both committing crimes and preventing them. The one dollar counterfeiter reminds us that security must account for logic and illogic alike.
Related Articles
Transforming Gaza: From Conflict Zone to Tech Hub
A leaked plan from the Trump administration reveals a bold strategy to turn Gaza into a thriving high-tech hub. Discover the potential.
Sep 3, 2025

Gaza's Tech Revolution: Trump's Bold High-Tech Vision
A leaked plan from the Trump administration unveils a vision to make Gaza a high-tech hub, focusing on AI, cybersecurity, and digital innovation.
Sep 3, 2025
AI Tools Reveal Identities of ICE Officers Online
AI's emerging role in unmasking ICE officers spotlights the intersection of technology, privacy, and ethics, sparking a crucial societal debate.
Sep 2, 2025
