- Home
- Technology
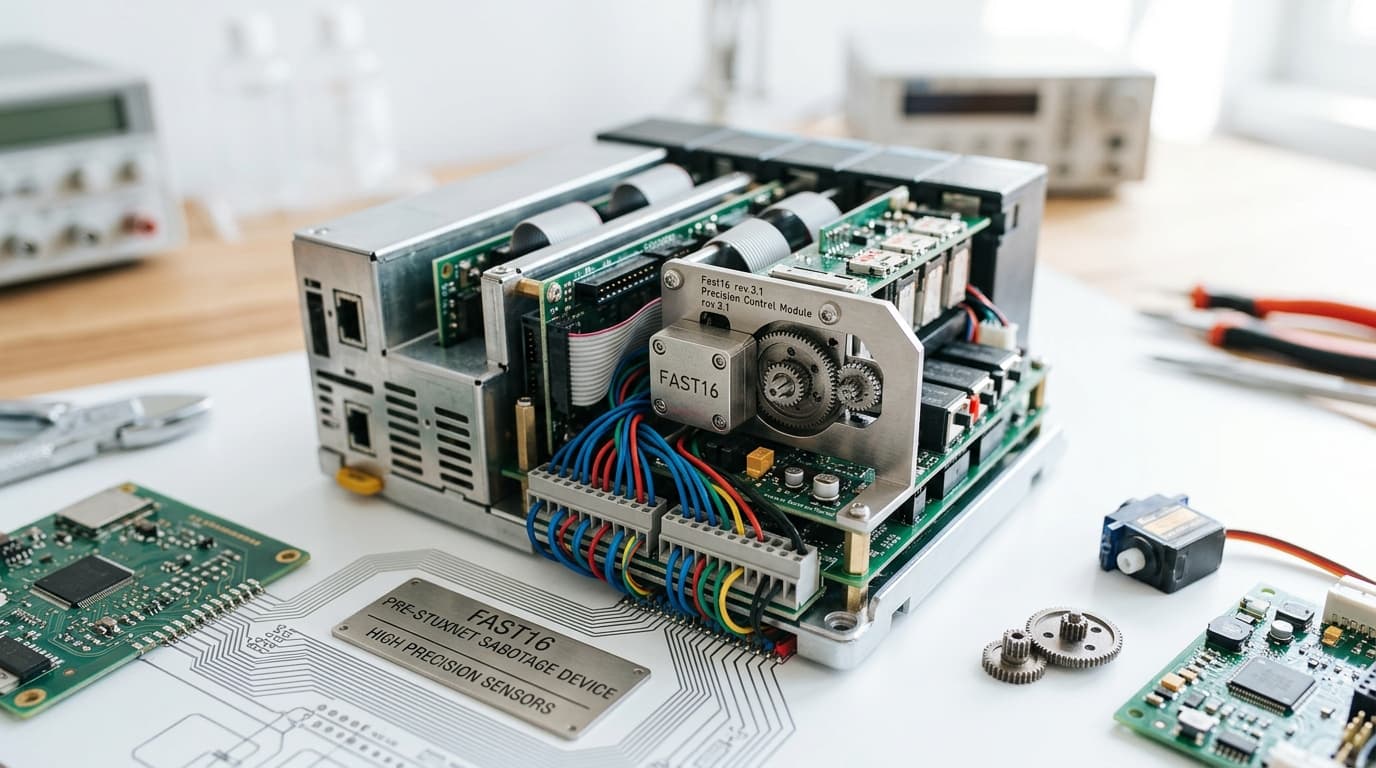
- Fast16: High-Precision Sabotage 5 Years Before Stuxnet
Fast16: High-Precision Sabotage 5 Years Before Stuxnet
Before Stuxnet made headlines, Fast16 silently sabotaged industrial control systems in 2005. This forgotten cyberweapon pioneered precision attacks on critical infrastructure.
The Forgotten Cyberweapon That Changed Everything
Learn more about the fake disease that fooled the internet: bixonimania
Five years before Stuxnet captured global attention as the world's first digital weapon, another sophisticated attack was quietly undermining industrial control systems. Fast16, a precision-engineered malware campaign, targeted critical infrastructure with surgical accuracy in 2005. Yet this groundbreaking cyberattack remains largely unknown outside specialized security circles.
The story of Fast16 reveals how nation-state cyber sabotage evolved long before most organizations recognized the threat. Understanding this early campaign provides crucial context for today's industrial cybersecurity challenges and demonstrates that sophisticated attacks on operational technology are not a recent phenomenon.
What Made Fast16 a Pioneering Cyberattack?
Fast16 represented a fundamental shift in how adversaries approached industrial systems. Unlike traditional malware that spread indiscriminately, this attack demonstrated precise targeting of specific industrial processes. The malware modified control parameters in ways that caused physical damage while avoiding immediate detection.
The attack focused on manipulating process control values within industrial automation systems. Operators watched their systems apparently function normally while underlying control logic slowly degraded equipment performance. This stealth approach allowed the sabotage to persist for extended periods before discovery.
Researchers later identified Fast16's ability to alter programmable logic controller (PLC) configurations without triggering standard alarms. The malware understood industrial protocols well enough to make changes that appeared legitimate to monitoring systems. This level of sophistication required deep knowledge of both cybersecurity and industrial engineering.
How Did Fast16's Technical Architecture Work?
Fast16 exploited vulnerabilities in legacy industrial control systems that lacked modern security protections. The malware traveled through air-gapped networks using removable media, a technique Stuxnet would later perfect. Once inside target networks, it mapped control systems and identified specific equipment worth sabotaging.
The attack code included several innovative features:
- Custom protocol parsers for industrial communication standards
- Logic bombs triggered by specific operational conditions
- Rootkit capabilities to hide modifications from operators
- Self-preservation mechanisms that prevented system crashes
- Data exfiltration modules to report success back to operators
For a deep dive on i bought friendster for $30k: my revival plan revealed, see our full guide
These capabilities demonstrated adversary investment in understanding industrial environments. The attackers knew that crashing systems would trigger immediate investigation, while subtle degradation could continue undetected for months.
How Did Fast16 Differ From Stuxnet?
For a deep dive on why apple's ceo transition timing matters in 2026, see our full guide
While Stuxnet receives most attention in discussions of industrial cyber sabotage, Fast16 pioneered many similar techniques. Both attacks targeted industrial control systems with precision rather than causing widespread disruption. Both required extensive reconnaissance and understanding of target operations.
However, Fast16 operated on a smaller scale with less sophisticated delivery mechanisms. Stuxnet's use of multiple zero-day exploits and stolen digital certificates represented an escalation in resources and complexity. Fast16 relied more on social engineering and existing vulnerabilities than novel exploits.
The target selection also differed significantly. Fast16 focused on manufacturing and process control facilities across multiple industries. Stuxnet famously targeted Iranian nuclear enrichment centrifuges with laser-focused precision.
Why Did Fast16 Remain Hidden?
Several factors contributed to Fast16's obscurity compared to Stuxnet's notoriety. Affected organizations had strong incentives to keep breaches confidential. Admitting to successful sabotage could damage customer confidence and invite regulatory scrutiny. Many victims likely never publicly acknowledged the attacks.
The security community in 2005 was less equipped to analyze industrial control system malware. Few researchers understood both cybersecurity and operational technology well enough to reverse engineer the attacks. By the time capabilities improved, Fast16 had already faded from active circulation.
The geopolitical context differed dramatically. Stuxnet emerged during heightened tensions over Iran's nuclear program, guaranteeing media attention. Fast16 targeted commercial facilities without clear political narratives, making it less newsworthy despite similar technical sophistication.
What Lessons Does Fast16 Teach Modern ICS Security?
The Fast16 campaign offers critical insights for organizations protecting industrial systems today. It proves that sophisticated adversaries have targeted operational technology for nearly two decades. The threat is not new, even if awareness has increased recently.
Organizations must recognize that air gaps provide limited protection against determined attackers. Both Fast16 and Stuxnet successfully breached isolated networks through removable media and supply chain compromises. Modern ICS security requires defense in depth rather than relying on network segmentation alone.
Detection capabilities remain crucial for identifying subtle sabotage. Fast16's success stemmed partly from its ability to avoid triggering alarms while degrading equipment. Organizations need behavioral monitoring that identifies anomalous control commands even when systems appear to function normally.
What Security Measures Could Have Prevented Fast16?
Several security controls could have detected or prevented Fast16, though many were not widely implemented in 2005. Application whitelisting would have blocked unauthorized code execution on control systems. Configuration management tools could have identified unauthorized changes to PLC logic.
Network monitoring with protocol-aware inspection would have spotted malicious commands disguised as legitimate traffic. Regular integrity checks on control logic could have revealed unauthorized modifications. These measures are now considered ICS security best practices, partly because of lessons learned from attacks like Fast16.
User awareness training also plays a critical role. Many industrial control system breaches begin with social engineering or infected removable media. Educating operators and engineers about cyber threats reduces the likelihood of successful initial compromise.
How Has Industrial Cyber Sabotage Evolved Since Fast16?
Fast16 marked an important milestone in the evolution of cyber warfare targeting critical infrastructure. It demonstrated that adversaries could develop specialized capabilities for attacking industrial processes years before Stuxnet made such attacks famous. The campaign showed that operational technology was vulnerable and valuable enough to warrant sophisticated attack development.
Since 2005, industrial cyber threats have grown in both number and sophistication. Attacks like TRITON, Industroyer, and numerous ransomware campaigns have targeted critical infrastructure worldwide. Each incident builds on lessons learned from predecessors like Fast16, incorporating new techniques while refining proven approaches.
The fundamental challenge remains unchanged. Industrial control systems were designed for reliability and safety, not security. Legacy equipment often runs for decades without updates, creating persistent vulnerabilities.
Why Is Attribution Difficult in Industrial Cyberattacks?
Identifying the actors behind Fast16 remains difficult even years after the campaign. Industrial sabotage attacks often lack clear attribution indicators, especially when attackers prioritize operational security. Fast16 left few forensic traces that could definitively link it to specific threat actors or nation-states.
This attribution challenge complicates response and deterrence efforts. Without knowing who conducted the attack, victims cannot pursue appropriate countermeasures or diplomatic responses. The ambiguity also encourages more actors to develop similar capabilities, knowing they can maintain plausible deniability.
Why Does Fast16 Matter Today?
Understanding Fast16 provides crucial historical context for current industrial cybersecurity challenges. The attack demonstrates that sophisticated threats to operational technology emerged earlier than many security professionals realize. Organizations that assume industrial cyber sabotage is a recent phenomenon may underestimate their risk exposure.
The techniques pioneered in Fast16 continue appearing in modern attacks. Adversaries still exploit air-gapped networks, manipulate control logic, and use stealth to avoid detection. Security teams defending industrial systems benefit from studying how these approaches evolved over nearly two decades.
Fast16 also highlights the importance of information sharing within the security community. The attack remained obscure partly because affected organizations kept breaches confidential. Greater transparency about industrial control system incidents helps the entire community improve defenses and understand emerging threats.
How Can You Protect Industrial Systems in the Post-Fast16 Era?
Modern industrial cybersecurity requires learning from historical attacks like Fast16 while addressing current threats. Organizations should implement comprehensive security programs that address both IT and OT environments. This includes network segmentation, access controls, monitoring, and incident response capabilities tailored to industrial operations.
Regular security assessments help identify vulnerabilities before adversaries exploit them. Penetration testing specifically designed for industrial control systems can reveal weaknesses that traditional IT security audits might miss. These assessments should include both technical testing and operational security reviews.
Collaboration between security teams and operations personnel is essential. Fast16 succeeded partly because attackers understood industrial processes better than many defenders. Bridging the gap between cybersecurity expertise and operational knowledge strengthens overall security posture.
Conclusion: The Hidden History of Industrial Cyber Warfare
Fast16 represents a crucial but overlooked chapter in the history of industrial cyber sabotage. Five years before Stuxnet made headlines, this sophisticated campaign demonstrated that adversaries could precisely target and manipulate critical infrastructure. The attack pioneered techniques that remain relevant in today's threat landscape.
The lessons from Fast16 remain vital for organizations protecting industrial systems. Sophisticated threats to operational technology have existed for nearly two decades, requiring sustained investment in specialized security capabilities. Understanding this history helps security teams appreciate the evolution of industrial cyber threats and prepare for future challenges.
Continue learning: Next, explore the ai playbook that built an $80m 1-person business
As industrial systems become increasingly connected and digitized, the techniques pioneered in Fast16 will likely appear in new forms. Organizations that learn from this forgotten cyberweapon can better defend against the next generation of industrial sabotage campaigns.
Related Articles

Transforming Gaza: From Conflict Zone to Tech Hub
A leaked plan from the Trump administration reveals a bold strategy to turn Gaza into a thriving high-tech hub. Discover the potential.
Sep 3, 2025

Gaza's Tech Revolution: Trump's Bold High-Tech Vision
A leaked plan from the Trump administration unveils a vision to make Gaza a high-tech hub, focusing on AI, cybersecurity, and digital innovation.
Sep 3, 2025

AI Tools Reveal Identities of ICE Officers Online
AI's emerging role in unmasking ICE officers spotlights the intersection of technology, privacy, and ethics, sparking a crucial societal debate.
Sep 2, 2025
Comments
Loading comments...
