- Home
- Technology
- Edit Store Price Tags Using Flipper Zero: What You Need t...
Edit Store Price Tags Using Flipper Zero: What You Need t...
Flipper Zero has sparked concerns about retail security. This guide explains what the device can actually do with electronic price tags and the serious legal consequences involved.
Can Flipper Zero Edit Store Price Tags? Technical Reality vs Legal Risk
Learn more about angine de poitrine: the chest-crushing mix technique
The Flipper Zero has gained notoriety as a portable multi-tool for hardware hackers and security researchers. Among the many concerns surrounding this device, one question keeps surfacing: can it edit store price tags?
The short answer is technically possible but highly illegal and impractical. This article explores the technical capabilities, security implications, and legal consequences of attempting to manipulate electronic shelf labels (ESLs) with a Flipper Zero.
Retail stores increasingly rely on digital price tags that communicate wirelessly with central systems. These electronic shelf labels streamline pricing updates and inventory management. However, their wireless nature raises legitimate security questions that retailers and security professionals must address.
What Is Flipper Zero?
Flipper Zero is an open-source multi-tool device designed for hardware exploration and security testing. The pocket-sized gadget resembles a retro gaming device but packs serious technical capabilities.
It interacts with various wireless protocols including RFID, NFC, infrared, Bluetooth, and sub-GHz radio frequencies. Security researchers use the device to identify vulnerabilities in access control systems, test IoT device security, and analyze wireless communications.
The device costs around $169 and has become popular among penetration testers and hobbyists alike. Its dolphin-themed interface and playful design mask sophisticated hardware that captures, analyzes, and replays wireless signals. The open-source nature means developers constantly create new firmware and applications, making it powerful for legitimate security research but also raising concerns about misuse.
How Do Electronic Shelf Labels Work?
Electronic shelf labels represent a significant technological upgrade from paper price tags. These digital displays connect to a central management system through wireless protocols.
Most ESL systems use proprietary radio frequencies in the sub-GHz range, typically around 433 MHz or 868 MHz depending on regional regulations. The labels receive pricing updates from a base station that communicates with the store's inventory management system.
When prices change in the database, the system broadcasts updates to relevant tags throughout the store. Each label has a unique identifier that ensures updates reach the correct product.
What Security Features Protect Electronic Price Tags?
Modern ESL systems incorporate several security layers:
For a deep dive on laws of software engineering: timeless principles for devs, see our full guide
- Encrypted communication between base stations and labels
- Authentication protocols that verify legitimate update commands
- Tamper detection that alerts staff to physical interference
- Checksum verification to ensure data integrity
- Limited write access that restricts unauthorized modifications
Major ESL manufacturers include SES-imagotag, Pricer, and Displaydata. These companies continuously update security protocols to address emerging threats.
For a deep dive on prego's dinner recording device: a bold brand pivot, see our full guide
Can Flipper Zero Actually Edit Price Tags?
The technical capability exists, but practical execution faces significant obstacles. Flipper Zero can capture and analyze sub-GHz radio signals that some ESL systems use. The device could theoretically intercept communications between base stations and labels.
However, successfully editing a price tag requires overcoming multiple security layers. First, the attacker must identify the specific protocol the ESL system uses. Different manufacturers implement proprietary communication standards that vary significantly.
Capturing signals provides only raw data that requires extensive reverse engineering to decode. Second, modern ESL systems encrypt their communications. Breaking this encryption without the proper keys ranges from extremely difficult to practically impossible with a Flipper Zero's limited processing power.
Third, authentication mechanisms prevent unauthorized devices from sending valid update commands. Even if someone decodes the protocol and encryption, the system will reject commands lacking proper authentication credentials.
Have Researchers Successfully Hacked Electronic Price Tags?
Security researchers have demonstrated vulnerabilities in older ESL systems under controlled conditions. These proof-of-concept attacks typically target legacy systems lacking modern encryption.
One documented case involved a 2018 research project that successfully manipulated first-generation electronic labels. The researchers worked directly with the manufacturer to patch vulnerabilities before publishing their findings. This responsible disclosure approach improved security for millions of retail installations.
However, these demonstrations occurred in laboratory settings with extensive preparation. They required weeks of analysis, specialized equipment beyond a standard Flipper Zero, and detailed knowledge of the target system. The scenarios bear little resemblance to casual tampering attempts in retail environments.
What Are the Legal Consequences of Price Tag Manipulation?
Attempting to edit store price tags constitutes serious criminal activity across multiple jurisdictions. The legal ramifications extend far beyond simple theft or fraud charges.
In the United States, manipulating price tags falls under the Computer Fraud and Abuse Act (CFAA). This federal law prohibits unauthorized access to computer systems, which includes electronic price tag networks.
Violations carry penalties including:
- Up to 10 years imprisonment for first-time offenses
- Fines reaching $250,000 or more
- Restitution payments to affected retailers
- Permanent criminal record affecting future employment
State laws add additional charges for fraud, theft, and unauthorized computer access. Many jurisdictions classify these crimes as felonies rather than misdemeanors. The severity increases if the manipulation affects multiple items or results in significant financial loss.
What Civil Liability Do Price Tag Hackers Face?
Civil liability compounds the legal risks. Retailers can pursue civil lawsuits seeking damages far exceeding the value of manipulated prices.
These suits may claim:
- Direct financial losses from incorrect pricing
- Costs of security audits and system upgrades
- Reputational damage and loss of customer trust
- Investigation expenses and legal fees
The combination of criminal prosecution and civil liability creates overwhelming legal consequences. A few dollars saved through price manipulation can result in hundreds of thousands in penalties and years behind bars.
How Do Retailers Detect Price Tag Tampering?
Retailers implement multiple layers of security to detect and prevent price tag tampering. Modern systems include sophisticated monitoring that identifies suspicious activity in real-time.
Anomalous pricing triggers automatic alerts when tags display values outside expected ranges. If a premium item suddenly shows a drastically reduced price, the system flags it for immediate review. Store personnel receive notifications to verify the pricing discrepancy.
Radio frequency monitoring detects unauthorized wireless transmissions near ESL systems. Retailers deploy sensors that identify unusual signal patterns or unauthorized devices attempting to communicate with price tags. These systems can pinpoint the location of suspicious activity within the store.
Video surveillance provides additional protection through AI-powered analytics. Modern cameras identify individuals spending excessive time near price tags or exhibiting suspicious behavior.
What Happens When Someone Gets Caught Tampering?
Detection typically happens before any transaction completes. When a customer attempts to purchase an item with a manipulated price, several safeguards activate.
Point-of-sale systems cross-reference scanned prices against the central database. Discrepancies halt the transaction and alert management. Security personnel review surveillance footage to identify the responsible party.
Most stores maintain strict policies requiring police involvement for suspected tampering. Law enforcement treats these incidents seriously due to the technical sophistication involved. Prosecutors often pursue maximum penalties to deter others from similar attempts.
What Ethical Standards Apply to Security Research?
Legitimate security research serves valuable purposes when conducted responsibly. Identifying vulnerabilities in retail systems helps manufacturers improve protection and safeguard consumers.
However, ethical research requires strict adherence to legal and professional standards. Responsible disclosure protocols mandate informing manufacturers of vulnerabilities before public release. Researchers provide detailed technical information allowing companies to develop patches.
A reasonable timeframe, typically 90 days, allows implementation before disclosure. Authorization remains paramount for any security testing. Researchers must obtain explicit written permission from system owners before conducting assessments.
Professional organizations like the Electronic Frontier Foundation and CERT Coordination Center provide frameworks for responsible security research. These guidelines help researchers navigate legal complexities while contributing to improved security.
How Does ESL Security Fit Into Broader IoT Concerns?
Electronic shelf labels represent just one component of expanding IoT infrastructure in retail environments. The same security concerns apply to countless connected devices throughout stores and beyond.
Manufacturers balance convenience with security when designing connected devices. Strong encryption and authentication add costs and complexity. Some companies prioritize ease of deployment over robust security, creating vulnerabilities that persist for years.
The retail sector has responded to security concerns by implementing industry standards and best practices. Organizations like the Retail Industry Leaders Association publish security guidelines for connected systems. Compliance with these standards has become a competitive differentiator.
Future ESL systems will likely incorporate advanced security features including blockchain-based authentication and quantum-resistant encryption. These technologies will make unauthorized manipulation virtually impossible while maintaining operational efficiency.
The Bottom Line on Flipper Zero and Price Tags
While Flipper Zero possesses technical capabilities that could theoretically interact with electronic shelf labels, successfully editing store price tags remains highly impractical and illegal. Modern ESL systems incorporate robust security measures including encryption, authentication, and real-time monitoring.
The legal consequences of attempting price manipulation include federal felony charges, substantial fines, and imprisonment. Security researchers exploring these systems must follow responsible disclosure practices and obtain proper authorization.
The retail industry continues advancing ESL security to address emerging threats while maintaining operational efficiency. For anyone considering using a Flipper Zero or similar device to manipulate retail systems, the message is clear: the minimal potential gain pales compared to the severe legal, financial, and personal consequences.
Continue learning: Next, explore anthropic allows openclaw-style claude cli usage again
The technology exists for legitimate security research and education, not criminal activity.
Related Articles
AI Tools Reveal Identities of ICE Officers Online
AI's emerging role in unmasking ICE officers spotlights the intersection of technology, privacy, and ethics, sparking a crucial societal debate.
Sep 2, 2025
AI's Role in Unveiling ICE Officers' Identities
AI unmasking ICE officers underscores a shift towards transparent law enforcement, raising questions about privacy and ethics in the digital age.
Sep 2, 2025
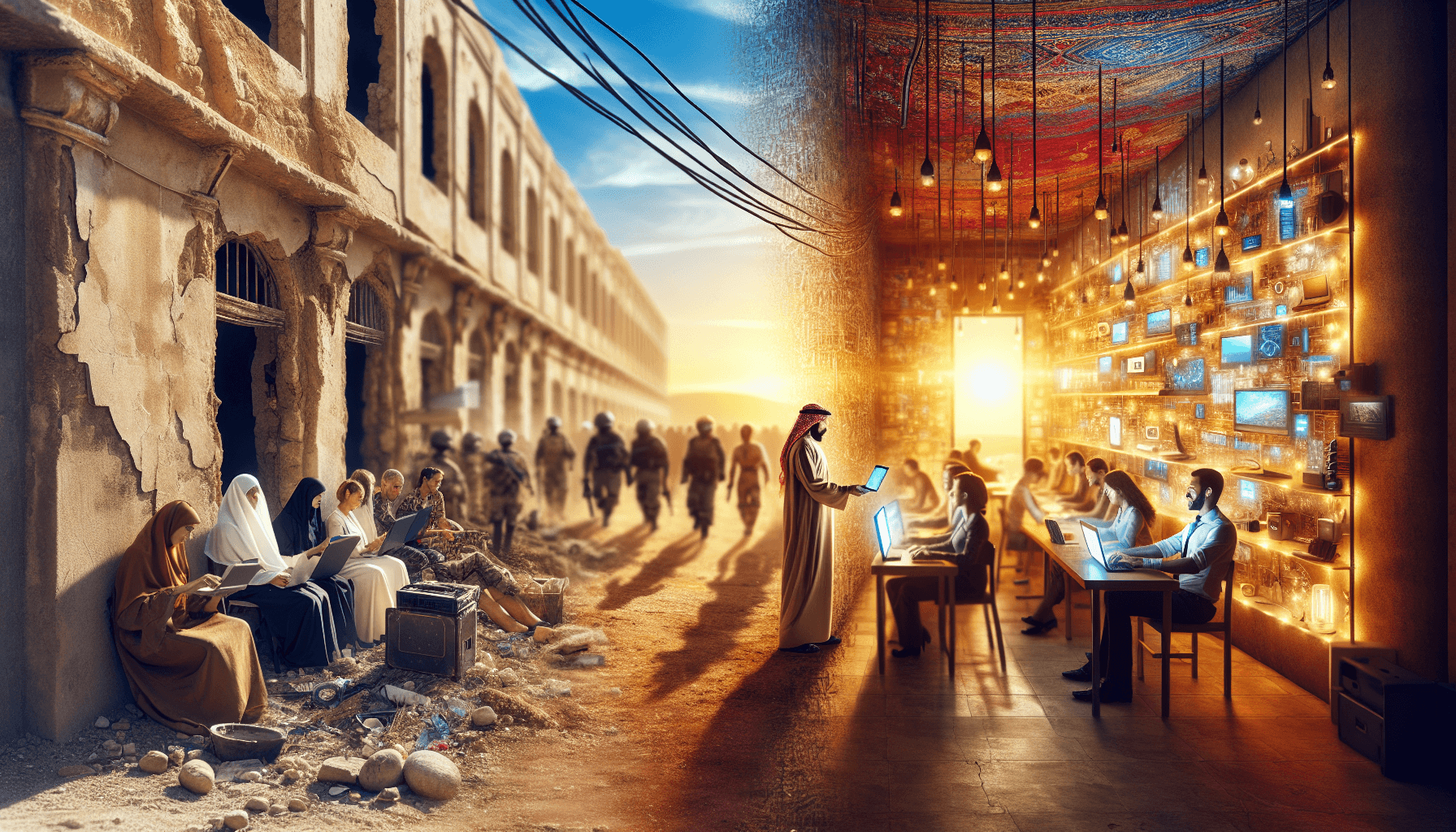
Transforming Gaza: From Conflict Zone to Tech Hub
A leaked plan from the Trump administration reveals a bold strategy to turn Gaza into a thriving high-tech hub. Discover the potential.
Sep 3, 2025