- Home
- Technology
- DOGE Whistleblower: Social Security Data Breach Alert
DOGE Whistleblower: Social Security Data Breach Alert
A whistleblower reveals that a Department of Government Efficiency member took Social Security data to their new employer, raising serious cybersecurity and privacy concerns.
DOGE Member Allegedly Takes Social Security Data to New Employer
Learn more about openai chatgpt updates: interactive learning amid lawsuits
A whistleblower has come forward with alarming allegations that a Department of Government Efficiency (DOGE) member took sensitive Social Security data to their new job. This revelation raises critical questions about data security protocols within federal agencies and the safeguards protecting millions of Americans' personal information. The incident highlights a growing concern in cybersecurity: insider threats and the unauthorized transfer of personally identifiable information (PII).
The timing of this disclosure could not be more significant. As government agencies increasingly digitize citizen data and implement new efficiency measures, the risk of data breaches from within grows exponentially. This case serves as a stark reminder that even well-intentioned modernization efforts can create vulnerabilities if proper security measures are not enforced.
What Happened in the DOGE Data Breach?
The Department of Government Efficiency was established to streamline federal operations and reduce bureaucratic inefficiencies. However, this whistleblower complaint suggests that efficiency improvements may have come at the expense of data security.
According to the allegations, a DOGE team member with access to Social Security Administration data took sensitive information when transitioning to a private sector position. This type of data breach represents one of the most serious cybersecurity violations possible.
Social Security numbers serve as primary identifiers for millions of Americans, linking to financial accounts, medical records, and government benefits. When this data falls into unauthorized hands, the consequences can be devastating for affected individuals.
What Types of Data Were Allegedly Compromised?
While specific details remain under investigation, Social Security data typically includes:
- Full Social Security numbers and associated personal identifiers
- Names, addresses, and dates of birth
- Benefit payment information and financial data
- Employment history and earnings records
- Medical disability information in some cases
The scope of the alleged data transfer remains unclear. Even a small dataset could affect thousands of individuals. Federal agencies maintain massive databases containing decades of citizen information, making any unauthorized access a potential large-scale breach.
For a deep dive on march patch tuesday: protect your digital wellness now, see our full guide
How Did This Security Breach Occur?
Insider threats represent approximately 60% of all data breaches, according to recent cybersecurity research. These incidents occur when employees, contractors, or partners with legitimate access misuse their privileges. In this case, the DOGE member allegedly exploited their authorized access to extract data before leaving their position.
For a deep dive on legal software reimplementation: a developer's guide, see our full guide
Modern data loss prevention (DLP) systems should theoretically prevent such transfers. These tools monitor data movement, flag suspicious activities, and block unauthorized file transfers.
The fact that this alleged breach occurred suggests potential gaps in DOGE's security infrastructure. Inadequate monitoring of employee activities may have allowed the unauthorized data transfer to proceed undetected.
What Are the Legal Consequences of Taking Social Security Data?
Unauthorized access and transfer of federal data violates multiple laws and regulations. The Privacy Act of 1974 specifically protects Social Security information and restricts its disclosure. Violations can result in criminal penalties, including fines and imprisonment.
The Computer Fraud and Abuse Act (CFAA) criminalizes unauthorized access to computer systems and data theft. If the allegations prove true, the individual could face federal charges carrying significant prison sentences. The receiving employer might also face liability if they knowingly accepted stolen government data.
Regulatory bodies including the Office of Inspector General and the Department of Justice typically investigate such cases. These investigations can take months or years, depending on the complexity and scope of the alleged breach.
How Can Organizations Prevent Insider Data Theft?
This incident provides valuable lessons for both government agencies and private sector organizations handling sensitive data. Effective prevention requires a multi-layered approach combining technology, policy, and culture.
What Technical Safeguards Stop Data Theft?
Organizations must deploy robust DLP solutions that monitor data access and movement in real-time. These systems should flag unusual download patterns, large file transfers, and access to sensitive data outside normal work patterns.
Encryption should protect data both at rest and in transit, making stolen information unusable without proper decryption keys. Access controls should follow the principle of least privilege, granting employees only the minimum access necessary for their roles. Regular access reviews ensure that permissions remain appropriate as job responsibilities change.
What Policies Protect Sensitive Data?
Comprehensive data governance policies must clearly define:
- What constitutes sensitive data and how it should be handled
- Acceptable use policies for accessing and transferring information
- Consequences for policy violations
- Procedures for reporting suspected data breaches
- Exit protocols for departing employees
Employees should receive regular training on these policies and sign acknowledgments confirming their understanding. This creates both awareness and accountability.
What Should You Do If Your Social Security Data Was Compromised?
If you suspect your Social Security information may have been compromised in this or any data breach, take immediate protective action. Contact the three major credit bureaus to place fraud alerts on your credit reports. Consider freezing your credit to prevent unauthorized account openings.
Monitor your Social Security statement regularly for unauthorized earnings reports or benefit claims. The Social Security Administration provides free online access to your earnings history and benefit estimates. Unexplained changes could indicate identity theft.
File a report with the Federal Trade Commission through IdentityTheft.gov. This creates an official record and provides a recovery plan tailored to your situation.
If you notice fraudulent activity, file a police report and keep copies for your records. Documentation strengthens your case and helps protect your rights.
Why Do Government Data Breaches Keep Happening?
This alleged breach occurs against a backdrop of increasing cybersecurity challenges facing federal agencies. Government systems face constant attacks from foreign adversaries, criminal organizations, and insider threats.
Legacy systems, budget constraints, and complex bureaucracies often hamper security improvements. The transition to cloud-based systems and modern infrastructure creates both opportunities and risks. While cloud platforms offer enhanced security features, migration processes can create temporary vulnerabilities.
What Changes Might This Incident Prompt?
Whistleblower revelations often catalyze policy reforms and security enhancements. This case may prompt Congress to strengthen oversight of government data handling practices.
Agencies might implement stricter exit procedures for departing employees, including comprehensive data audits and device inspections. Increased investment in security monitoring tools and personnel seems likely.
Automated systems can detect anomalous behavior patterns that human oversight might miss. However, technology alone cannot solve insider threat problems without cultural commitment to security.
How Do Whistleblowers Protect Data Security?
Whistleblowers play a critical role in exposing security failures and protecting public interests. Federal law provides protections for individuals who report government wrongdoing through proper channels. These protections prevent retaliation and encourage transparency.
In this case, the whistleblower's decision to come forward may have prevented further data misuse and prompted necessary security improvements. Their actions demonstrate the importance of creating safe reporting mechanisms within organizations.
Effective whistleblower programs require clear reporting channels, confidentiality protections, and demonstrated commitment to investigating complaints. Organizations that retaliate against whistleblowers not only violate legal protections but also discourage future reporting of critical issues.
Key Takeaways From the DOGE Data Breach Allegations
This whistleblower complaint highlights the persistent challenge of insider threats in data security. Even organizations focused on efficiency and modernization must prioritize robust security controls and monitoring.
The alleged unauthorized transfer of Social Security data demonstrates how individual actions can compromise the privacy of potentially thousands of citizens. Government agencies must strengthen exit procedures, enhance monitoring capabilities, and foster security-conscious cultures.
Technical solutions provide important safeguards, but human vigilance and accountability remain essential. Citizens should remain vigilant about protecting their personal information and take proactive steps when breaches occur.
Continue learning: Next, explore debian decides: how ai-generated code shapes linux future
The investigation into these allegations will likely continue for months, potentially resulting in criminal charges and policy reforms. This case serves as a powerful reminder that data security requires constant attention, investment, and commitment at every organizational level.
Related Articles
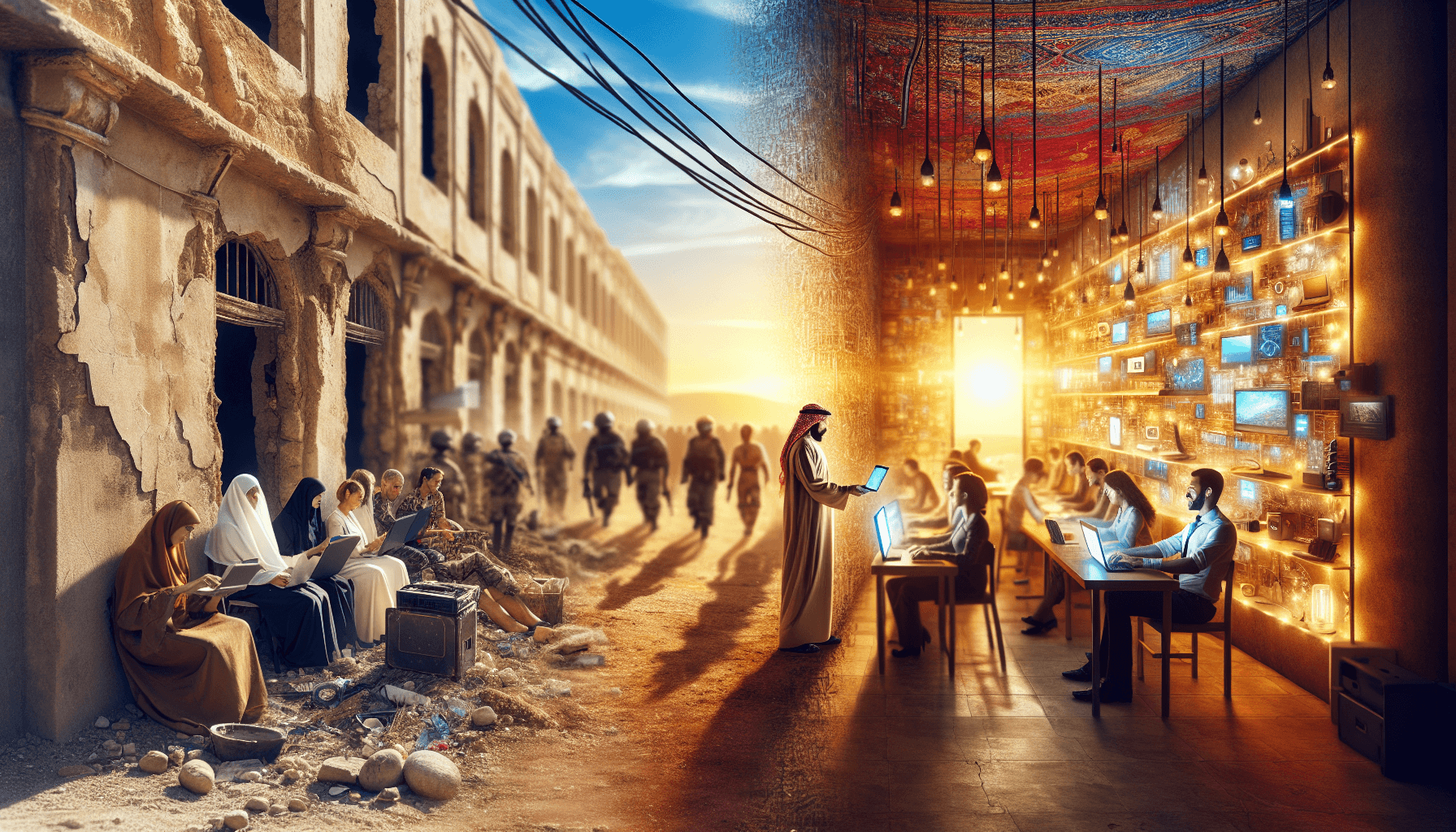
Transforming Gaza: From Conflict Zone to Tech Hub
A leaked plan from the Trump administration reveals a bold strategy to turn Gaza into a thriving high-tech hub. Discover the potential.
Sep 3, 2025
AI Tools Reveal Identities of ICE Officers Online
AI's emerging role in unmasking ICE officers spotlights the intersection of technology, privacy, and ethics, sparking a crucial societal debate.
Sep 2, 2025
AI's Role in Unveiling ICE Officers' Identities
AI unmasking ICE officers underscores a shift towards transparent law enforcement, raising questions about privacy and ethics in the digital age.
Sep 2, 2025