DJI Pays $30K for Robovac Hack: Security Lessons
When a security researcher accidentally exposed 7,000 robot vacuums, DJI turned a potential crisis into a $30,000 reward. Here's what businesses can learn from this cybersecurity incident.
DJI Pays $30K for Robovac Hack: What Can Businesses Learn?
Learn more about plasma bigscreen: kde's 10-foot interface revolution
A security researcher stumbled upon a massive vulnerability that exposed 7,000 Romo robot vacuums. Instead of facing legal threats, he received a $30,000 reward from DJI. This incident highlights a critical shift in how companies approach cybersecurity vulnerabilities.
The accidental hack reveals both the fragility of Internet of Things (IoT) security and the growing importance of bug bounty programs in modern business strategy. For companies managing fleets of connected devices or customer data, this case study demonstrates why proactive security measures matter.
How Did One Researcher Accidentally Expose Thousands of Devices?
The security researcher was not attempting a sophisticated attack when he uncovered the vulnerability in DJI's Romo robot vacuum system. Through routine security testing, he discovered a flaw that granted access to approximately 7,000 devices worldwide.
This discovery happened during legitimate security research. The researcher immediately recognized the severity of the issue and followed responsible disclosure protocols. He contacted DJI rather than exploiting the vulnerability or publishing the findings publicly.
This approach protected both consumers and DJI's reputation. The company gained valuable time to patch the vulnerability before malicious actors could exploit it. This prevented potential data breaches or device manipulation that could have damaged customer trust and resulted in costly litigation.
Why Did DJI Reward the Hacker Instead of Suing?
DJI's response demonstrates the strategic value of well-structured bug bounty programs. The company rewarded the researcher with $30,000 through their established vulnerability disclosure program instead of pursuing legal action.
Bug bounty programs offer several business advantages:
For a deep dive on ai jobs at risk: anthropic study reveals vulnerable careers, see our full guide
- Cost-effective security testing: Paying researchers $30,000 costs significantly less than dealing with a full-scale data breach, which averages $4.45 million according to IBM's 2023 Cost of a Data Breach Report
- Reputation management: Transparent handling of security issues builds customer trust and demonstrates corporate responsibility
- Competitive intelligence: Understanding vulnerabilities before competitors or hackers do provides strategic advantages
- Legal protection: Formal programs create clear guidelines that reduce litigation risks and encourage responsible disclosure
The $30,000 payout reflects industry standards for critical vulnerabilities. Companies like Google, Microsoft, and Apple regularly pay five to six figures for significant security discoveries. They recognize that prevention costs less than remediation.
For a deep dive on apple homepad launch delayed: what we know about release, see our full guide
What Does This Robovac Hack Reveal About IoT Security?
The Romo robovac incident exposes broader concerns about IoT device security that affect businesses across industries. As companies deploy more connected devices, from manufacturing sensors to smart office equipment, each device represents a potential entry point for cybercriminals.
Smart devices often ship with default passwords, unencrypted communications, or outdated firmware. These vulnerabilities multiply across device fleets, creating what security experts call an "attack surface." This surface grows with every connected device added to a network.
Businesses face particular risks when IoT devices connect to corporate networks. A compromised robot vacuum might seem trivial, but it can serve as a gateway to more sensitive systems. Hackers frequently exploit the weakest link in a network, and consumer-grade IoT devices rarely receive the same security scrutiny as enterprise systems.
How Should Companies Handle Security Vulnerability Reports?
DJI's positive response to the accidental hack stems from having clear responsible disclosure policies in place. These policies outline how security researchers should report vulnerabilities and what they can expect in return.
Effective disclosure policies should include specific timelines for reporting, investigation, and remediation. Researchers need to know how long they must wait before publicly disclosing findings. Companies need reasonable time to develop and deploy patches.
The best programs offer legal safe harbor, protecting researchers from prosecution when they follow established guidelines. This protection encourages more researchers to report vulnerabilities privately. It prevents them from selling information to malicious actors or publishing exploits publicly.
What Makes a Bug Bounty Program Successful?
Businesses considering bug bounty programs should establish clear frameworks before launching. The program scope must define which systems researchers can test and which methods are acceptable.
Reward structures should align with vulnerability severity. Critical flaws that could expose customer data or enable device takeovers warrant higher payments than minor issues. DJI's $30,000 payment for 7,000 exposed devices reflects appropriate valuation of a serious vulnerability.
Response time matters significantly. Companies should acknowledge reports within 24-48 hours and provide regular updates throughout the investigation. Slow responses frustrate researchers and may prompt premature public disclosure.
Does Investing in Security Research Actually Save Money?
Investing in bug bounty programs and security research delivers measurable returns. The $30,000 DJI paid represents a fraction of potential breach costs, including regulatory fines, customer compensation, and business disruption.
Regulatory environments increasingly penalize inadequate security measures. GDPR fines can reach 4% of global annual revenue, while California's CCPA imposes penalties up to $7,500 per violation. Proactive vulnerability discovery helps companies avoid these costly penalties.
Customer retention also depends on security reputation. Studies show 65% of consumers lose trust in companies after data breaches. Additionally, 27% stop doing business with affected companies entirely. The cost of customer acquisition far exceeds retention expenses, making security investment a customer relationship management strategy.
What Should Business Leaders Learn From This Incident?
The DJI robovac incident offers actionable insights for businesses of all sizes. First, treat security researchers as partners rather than adversaries. The collaborative approach yields better outcomes than hostile responses that drive researchers underground.
Second, implement security measures during product development, not as afterthoughts. Building security into IoT devices costs less than retrofitting protection after deployment. This "security by design" philosophy prevents vulnerabilities from reaching customers.
Third, maintain transparency with customers about security incidents. DJI's willingness to acknowledge and address the vulnerability demonstrates corporate responsibility. This approach strengthens rather than damages brand reputation.
How Can Companies Build a Security-First Culture?
Companies must foster internal cultures that prioritize security across all departments. Marketing teams should understand that security features represent competitive advantages. Product developers need resources and training to implement robust protections.
Executive leadership should allocate adequate budgets for security initiatives. These include bug bounty programs, penetration testing, and employee training. These investments protect not just data and devices, but also company valuation and market position.
Regular security audits help identify vulnerabilities before external researchers do. Third-party assessments provide objective evaluations that internal teams might miss. Familiarity bias or resource constraints often prevent internal teams from spotting critical issues.
What Does the Future Hold for IoT Security?
IoT adoption continues to accelerate, and security challenges will intensify. Industry analysts project 75 billion connected devices by 2025, each requiring protection against evolving threats. Businesses that establish strong security foundations now will gain competitive advantages as regulatory requirements tighten.
Artificial intelligence and machine learning will play increasing roles in vulnerability detection and threat response. Automated systems can identify unusual device behavior patterns that indicate compromise. This enables faster incident response.
Industry collaboration will become essential. Companies sharing threat intelligence and best practices can collectively raise security standards. This benefits entire sectors. DJI's transparent handling of the robovac vulnerability contributes to this collaborative approach.
How Can Your Business Turn Security Challenges Into Advantages?
DJI's $30,000 payment to the researcher who accidentally hacked 7,000 Romo robot vacuums demonstrates how companies can transform potential crises into opportunities. By maintaining robust bug bounty programs and responsible disclosure policies, businesses protect their assets while building trust with security researchers and customers.
The incident underscores critical lessons for modern businesses. Invest in proactive security measures. Treat researchers as partners. Maintain transparency throughout the disclosure process. These practices cost less than breach remediation while delivering superior protection and reputation management.
Continue learning: Next, explore hardening firefox with anthropic's red team techniques
For entrepreneurs and business leaders, the message is clear. Security investment is not optional in an increasingly connected world. Companies that prioritize vulnerability discovery and responsible disclosure will outperform competitors who treat security as an afterthought. They gain customer trust and market share in the process.
Related Articles
Acer's New Chromebook: A Game-Changer for Businesses?
Acer's Chromebook Plus Spin 514 combines AI and potent computing, offering businesses a glimpse into the future of work.
Sep 5, 2025
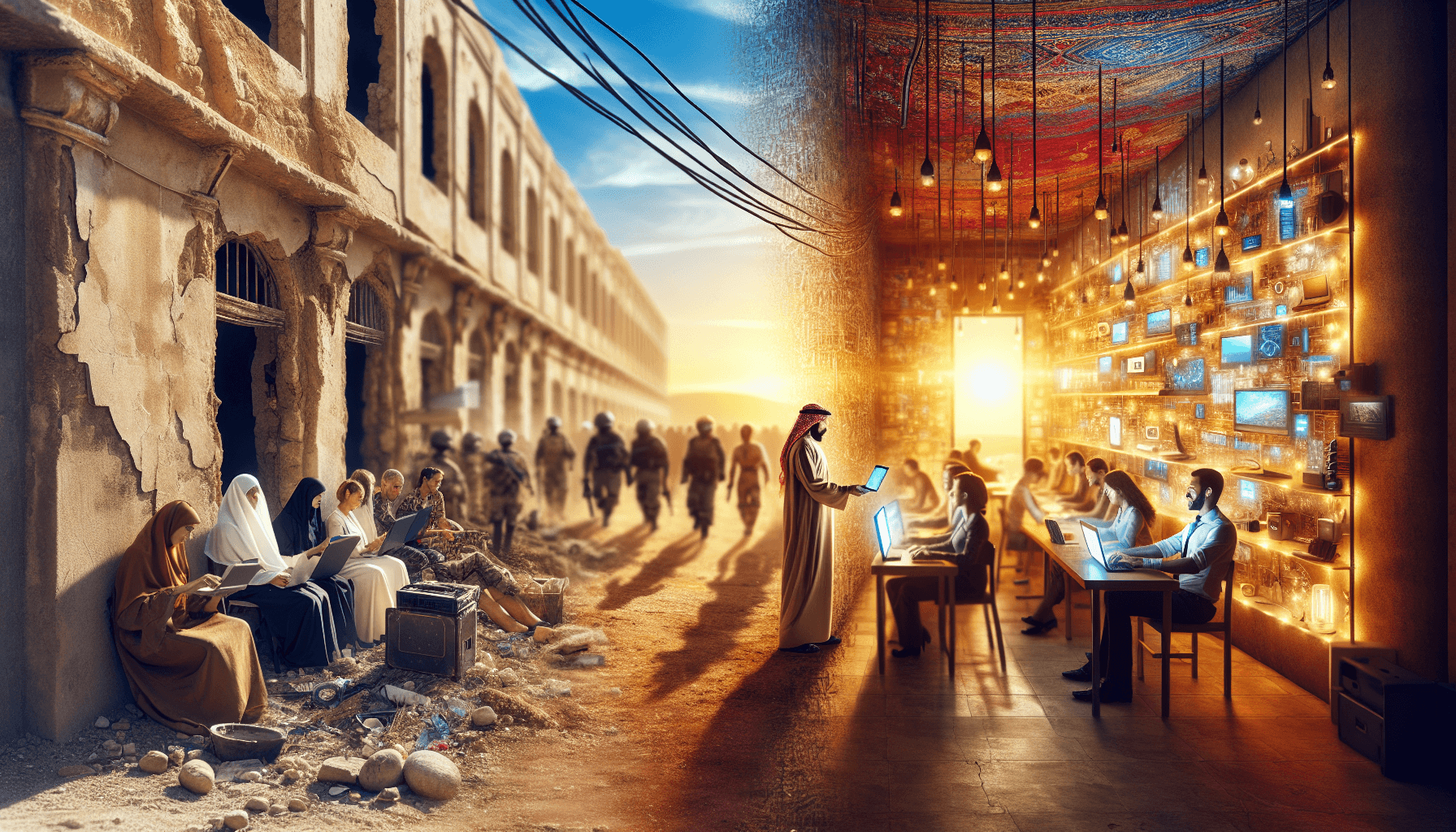
Transforming Gaza: From Conflict Zone to Tech Hub
A leaked plan from the Trump administration reveals a bold strategy to turn Gaza into a thriving high-tech hub. Discover the potential.
Sep 3, 2025
AI Tools Reveal Identities of ICE Officers Online
AI's emerging role in unmasking ICE officers spotlights the intersection of technology, privacy, and ethics, sparking a crucial societal debate.
Sep 2, 2025