DJI Pays $30K for Robot Vacuum Hack: Business Lessons
A tinkerer accidentally hacked 7,000 Romo robot vacuums while trying to connect a PS5 controller. DJI's $30,000 reward reveals critical lessons for modern businesses.
When Innovation Meets Vulnerability: The $30,000 Robot Vacuum Hack
Learn more about ki editor: the ast-based editor revolutionizing code
A security researcher's weekend project to control his robot vacuum with a PlayStation 5 controller unexpectedly exposed a critical vulnerability affecting 7,000 Romo robotic vacuums. DJI responded by paying the researcher $30,000 through its bug bounty program, turning a potential crisis into a masterclass in corporate security response.
This incident reveals essential lessons about cybersecurity, responsible disclosure, and how businesses should approach product vulnerabilities in an increasingly connected world. The story highlights a growing challenge for companies manufacturing Internet of Things (IoT) devices.
As consumer products become smarter and more connected, they also become potential targets for exploitation. For business leaders, this case study demonstrates why proactive security measures and transparent vulnerability management programs are essential components of product strategy.
How Did a Hobbyist Discover This Major Security Flaw?
The security researcher had a simple goal: customize his robot vacuum's controls. What started as a hobbyist project quickly revealed a significant security flaw that could potentially grant unauthorized access to thousands of devices.
The vulnerability allowed external parties to access camera feeds, control device functions, and potentially compromise user privacy. This wasn't a sophisticated attack by a malicious actor.
It was an engineer exploring the capabilities of a product he owned. The ease with which he discovered the vulnerability underscores a critical business reality: if one curious individual can find a security flaw, organized bad actors certainly can too. The researcher's decision to report the issue responsibly rather than exploit it or publish it publicly demonstrates the value of ethical hacking communities.
Why Do Bug Bounty Programs Matter for Business Security?
DJI's decision to pay $30,000 for this discovery reflects a mature approach to product security. Bug bounty programs have become essential tools for companies serious about protecting their customers and products. These programs incentivize security researchers to report vulnerabilities privately rather than selling them on dark web markets or disclosing them publicly.
The financial reward serves multiple business purposes beyond just compensating the researcher. It sends a clear message to the security community that DJI values their contributions.
It also costs significantly less than the potential damage from a public breach, regulatory fines, or class-action lawsuits that could follow a major security incident. According to industry data, the average cost of a data breach reached $4.45 million in 2023. Compared to these potential losses, a $30,000 bug bounty payment represents exceptional value.
What Business Benefits Do Bug Bounty Programs Provide?
Bug bounty programs create a win-win scenario for companies and security researchers. Businesses gain access to a global network of skilled professionals who test their products from angles internal teams might miss.
Researchers earn compensation for their skills while building reputations in the cybersecurity community. For DJI, this program demonstrates commitment to customer safety and product quality.
In an era where consumers increasingly consider privacy and security when making purchase decisions, this commitment becomes a competitive advantage. Companies that transparently address vulnerabilities build stronger brand trust than those that hide problems or respond defensively. The program also provides valuable market intelligence about potential attack vectors and helps companies understand how malicious actors might target their products.
What Does This Vulnerability Reveal About IoT Security Risks?
For a deep dive on magnetic vortices predicted 50 years ago finally observed, see our full guide
The Romo robot vacuum vulnerability exposed common weaknesses in IoT device security. These products often prioritize functionality and cost-effectiveness over robust security measures. Many manufacturers treat security as an afterthought rather than a fundamental design principle.
Robot vacuums equipped with cameras and sensors collect substantial amounts of data about users' homes. They map floor plans, capture images, and often connect to home networks.
For a deep dive on lab-grown pork at berkeley bowl: bay area's meat future, see our full guide
A compromised device could expose sensitive information about residents' routines, property layouts, and personal belongings. The vulnerability affecting 7,000 devices demonstrates how security flaws can scale rapidly in connected products. Unlike traditional software that users update manually, IoT devices often lack robust update mechanisms.
How Should Companies Respond to Security Vulnerabilities?
DJI's handling of this incident offers several actionable lessons for business leaders across industries. The company's response demonstrates how organizations can turn potential crises into opportunities for building trust and improving products.
Why Does Transparency Build Customer Trust?
DJI published a detailed blog post explaining the vulnerability, their response, and steps taken to protect users. This transparency contrasts sharply with companies that try to minimize or hide security issues.
Public acknowledgment shows respect for customers and demonstrates accountability. The company outlined specific technical details about the vulnerability without providing a roadmap for exploitation.
This balance allows informed users to understand the risk while preventing malicious actors from easily replicating the attack. Businesses should develop crisis communication protocols before incidents occur. Having pre-approved messaging frameworks and designated spokespersons enables faster, more consistent responses when vulnerabilities emerge.
What Makes a Vulnerability Management Program Effective?
Successful vulnerability management requires more than just bug bounty programs. Companies need comprehensive strategies that include several key components.
Regular security audits ensure periodic assessments of products and systems by internal teams and external experts. Secure development practices integrate security considerations throughout the product development lifecycle.
Rapid response capabilities establish processes for quickly validating, patching, and deploying fixes for reported vulnerabilities. Clear disclosure policies create guidelines that define how researchers should report issues and what they can expect in return. User notification systems develop mechanisms for informing affected customers about vulnerabilities and available patches.
What ROI Do Proactive Security Investments Deliver?
Investing in security before problems occur delivers measurable business value. Companies with mature security programs experience fewer breaches, face lower regulatory scrutiny, and maintain stronger customer relationships.
The financial benefits extend beyond avoiding breach costs. Proactive security measures reduce insurance premiums, as cyber insurance providers offer better rates to well-protected organizations.
They also facilitate business development, as enterprise customers increasingly require vendors to demonstrate robust security practices before signing contracts. For consumer-facing businesses, security becomes a marketing differentiator. Products marketed as secure and privacy-focused command premium prices and attract customers willing to pay more for peace of mind.
Why Does IoT Security Require Special Attention?
The proliferation of connected devices creates unprecedented security challenges for businesses. Unlike traditional computers or smartphones, IoT devices often have limited processing power, minimal user interfaces, and long product lifecycles.
These constraints complicate security implementation and maintenance. Many IoT devices ship with default passwords, unencrypted communications, or outdated software components.
Manufacturers sometimes prioritize rapid market entry over security rigor, creating vulnerabilities that persist for years. The Romo incident exemplifies how these shortcuts can expose thousands of users to risk.
What Regulations Govern IoT Device Security?
Governments worldwide are implementing stricter regulations for connected devices. The European Union's Cyber Resilience Act will require manufacturers to ensure products remain secure throughout their lifecycle.
Similar regulations are emerging in other jurisdictions, creating compliance obligations for global businesses. These regulations typically mandate security by design, regular updates, and transparent vulnerability disclosure.
Non-compliance can result in substantial fines and market access restrictions. Companies that proactively address security position themselves advantageously as regulations tighten. Business leaders should monitor regulatory developments in their markets and adjust product strategies accordingly.
How Can Companies Build Security Into Product Development?
Successful IoT security requires integration throughout the product development process. Security cannot be added as a final step before launch.
Companies should conduct threat modeling during design phases, implement secure coding practices during development, and perform penetration testing before release. This approach, known as "security by design," treats protection as a core product feature rather than an add-on.
It requires collaboration between engineering, security, and business teams to balance functionality, cost, and protection. Organizations should also plan for the entire product lifecycle, including establishing update mechanisms, defining end-of-life policies, and ensuring devices can receive security patches years after purchase.
What Actions Should Businesses Take Now?
The DJI incident provides a roadmap for companies manufacturing connected products or handling customer data. Several specific actions can strengthen security posture and reduce vulnerability exposure.
Should Your Company Launch a Bug Bounty Program?
Companies without bug bounty programs should evaluate whether implementing one makes strategic sense. Even small programs can provide valuable security insights.
Organizations should clearly define program scope, reward structures, and response timelines. Existing programs should be regularly reviewed and updated.
Are rewards competitive with industry standards? Do researchers receive timely responses? Is the submission process straightforward? Partnering with established bug bounty platforms can simplify program management by handling researcher verification, payment processing, and communication.
How Do Cross-Functional Security Teams Improve Protection?
Effective security requires collaboration across organizational silos. Cross-functional teams that include representatives from engineering, product management, legal, communications, and customer support can respond more effectively to vulnerabilities.
These teams should meet regularly to review security posture, discuss emerging threats, and coordinate responses to reported issues. They should also conduct tabletop exercises simulating security incidents to test response procedures and identify gaps.
Executive sponsorship is critical for these teams to succeed. Security decisions often require resource allocation and strategic tradeoffs that need C-level support.
Why Is Security Training Essential for All Employees?
Every employee plays a role in organizational security. Developers need training on secure coding practices.
Customer service representatives should understand how to handle security-related inquiries. Executives must grasp the business implications of security decisions.
Regular training programs keep security top-of-mind and help teams recognize potential vulnerabilities. These programs should evolve as threats change and should include practical, role-specific guidance rather than generic awareness content. Companies should also foster cultures where employees feel comfortable reporting potential security issues without fear of blame.
How Does Security Leadership Create Competitive Advantage?
Companies that excel at security gain competitive advantages beyond risk reduction. Security leadership builds brand reputation, enables premium pricing, and opens market opportunities that competitors cannot access.
Can Security Differentiate Your Products in the Market?
As consumers become more aware of privacy and security risks, they increasingly factor protection into purchase decisions. Products with strong security reputations command customer loyalty and word-of-mouth recommendations.
This is particularly valuable in markets where switching costs are low and alternatives are abundant. B2B customers often require security certifications and compliance demonstrations before purchasing.
Companies with mature security programs can pursue enterprise opportunities that smaller, less secure competitors cannot. Marketing security requires careful messaging that focuses on positive benefits like privacy protection and peace of mind rather than threat scenarios.
How Does Security Posture Affect Investment Opportunities?
Investors increasingly evaluate security posture when making funding decisions. Companies with strong security practices present lower risk profiles and better long-term prospects.
This is especially true for businesses handling sensitive data or operating in regulated industries. Strategic partnerships also depend on security credibility.
Larger companies conducting due diligence on potential partners thoroughly assess security capabilities. Demonstrated security excellence can accelerate partnership discussions and improve negotiating positions. Publicly traded companies face additional scrutiny from shareholders and analysts regarding cybersecurity practices.
What Is a Bug Bounty Program and Why Do Companies Use Them?
A bug bounty program is a crowdsourced security initiative where companies reward external researchers for discovering and reporting vulnerabilities in their products or systems. Companies use these programs because they provide cost-effective access to diverse security expertise that internal teams might lack.
Continue learning: Next, explore homepod pricing information could appear on device
Programs incentivize responsible disclosure rather than public exposure or exploitation of vulnerabilities. They typically cost
Related Articles
Acer's New Chromebook: A Game-Changer for Businesses?
Acer's Chromebook Plus Spin 514 combines AI and potent computing, offering businesses a glimpse into the future of work.
Sep 5, 2025
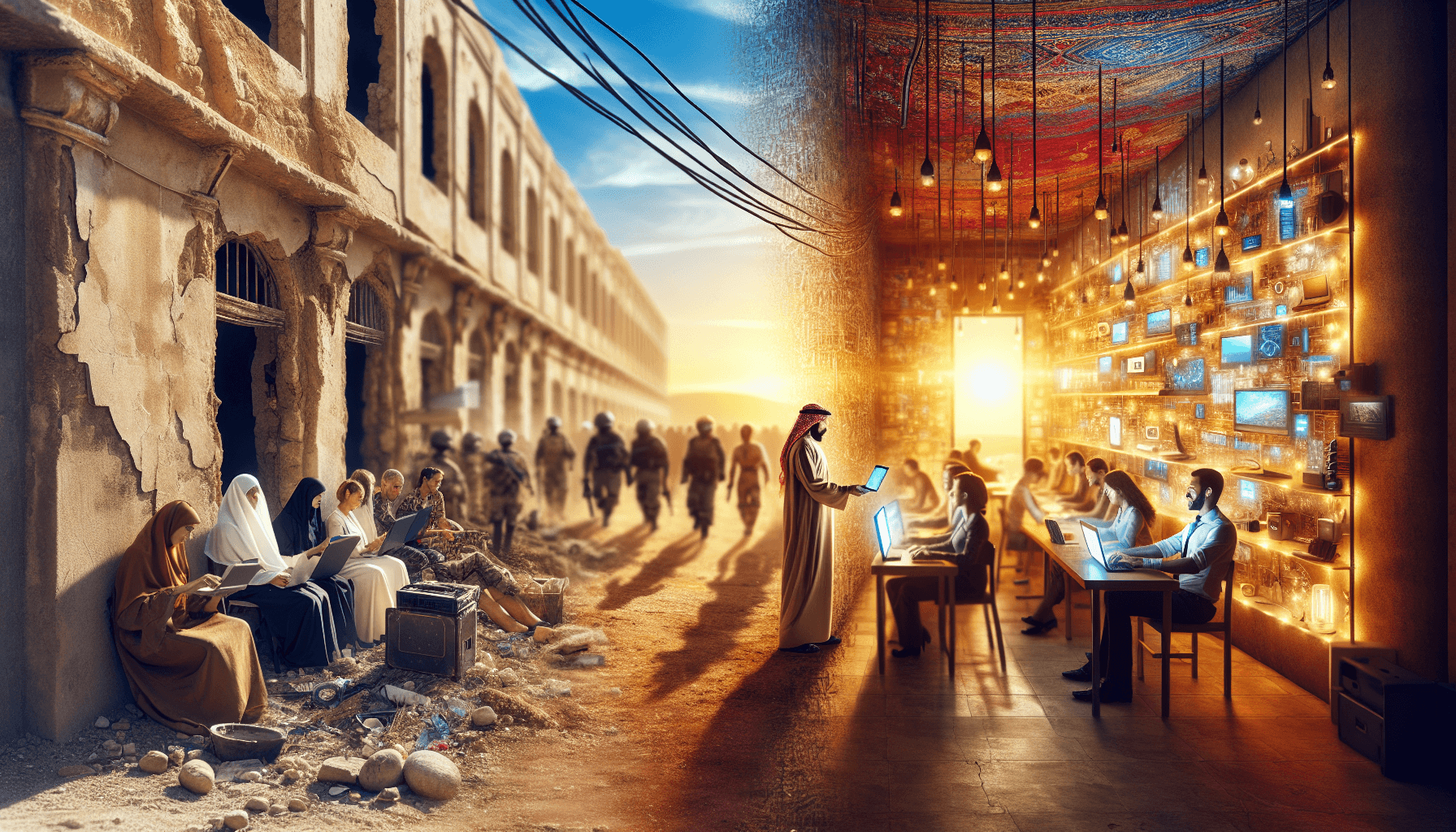
Transforming Gaza: From Conflict Zone to Tech Hub
A leaked plan from the Trump administration reveals a bold strategy to turn Gaza into a thriving high-tech hub. Discover the potential.
Sep 3, 2025
Sony's Paywall Strategy: Xperia Feature Sparks Debate
Sony's recent strategy to lock a key Xperia feature behind a subscription has sparked a debate on innovation versus monetization.
Sep 4, 2025